
Red Hat Enterprise Linux 9
Considerations in adopting RHEL 9
Key differences between RHEL 8 and RHEL 9
Last Updated: 2024-08-09


Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
Key differences between RHEL 8 and RHEL 9

Legal Notice
Copyright © 2024 Red Hat, Inc.
The text of and illustrations in this document are licensed by Red Hat under a Creative Commons
Attribution–Share Alike 3.0 Unported license ("CC-BY-SA"). An explanation of CC-BY-SA is
available at
http://creativecommons.org/licenses/by-sa/3.0/
. In accordance with CC-BY-SA, if you distribute this document or an adaptation of it, you must
provide the URL for the original version.
Red Hat, as the licensor of this document, waives the right to enforce, and agrees not to assert,
Section 4d of CC-BY-SA to the fullest extent permitted by applicable law.
Red Hat, Red Hat Enterprise Linux, the Shadowman logo, the Red Hat logo, JBoss, OpenShift,
Fedora, the Infinity logo, and RHCE are trademarks of Red Hat, Inc., registered in the United States
and other countries.
Linux ® is the registered trademark of Linus Torvalds in the United States and other countries.
Java ® is a registered trademark of Oracle and/or its affiliates.
XFS ® is a trademark of Silicon Graphics International Corp. or its subsidiaries in the United States
and/or other countries.
MySQL ® is a registered trademark of MySQL AB in the United States, the European Union and
other countries.
Node.js ® is an official trademark of Joyent. Red Hat is not formally related to or endorsed by the
official Joyent Node.js open source or commercial project.
The OpenStack ® Word Mark and OpenStack logo are either registered trademarks/service marks
or trademarks/service marks of the OpenStack Foundation, in the United States and other
countries and are used with the OpenStack Foundation's permission. We are not affiliated with,
endorsed or sponsored by the OpenStack Foundation, or the OpenStack community.
All other trademarks are the property of their respective owners.
Abstract
This document provides an overview of changes in RHEL 9 since RHEL 8 to help you evaluate an
upgrade to RHEL 9.

. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
Table of Contents
PROVIDING FEEDBACK ON RED HAT DOCUMENTATION
CHAPTER 1. PREFACE
CHAPTER 2. ARCHITECTURES
CHAPTER 3. REPOSITORIES
CHAPTER 4. APPLICATION STREAMS
CHAPTER 5. CLOUD
5.1. NOTABLE CHANGES TO AZURE
5.2. NOTABLE CHANGES TO GCP
CHAPTER 6. CONTAINERS
6.1. NOTABLE CHANGES TO CONTAINERS
CHAPTER 7. COMPILERS AND DEVELOPMENT TOOLS
7.1. NOTABLE CHANGES TO GLIBC
CHAPTER 8. DESKTOP
8.1. NOTABLE CHANGES TO DESKTOP
CHAPTER 9. DYNAMIC PROGRAMMING LANGUAGES, WEB SERVERS, DATABASE SERVERS
9.1. NOTABLE CHANGES TO DYNAMIC PROGRAMMING LANGUAGES, WEB AND DATABASE SERVERS
CHAPTER 10. EDGE
10.1. RHEL FOR EDGE
CHAPTER 11. FILE SYSTEMS AND STORAGE
11.1. FILE SYSTEMS
11.2. STORAGE
CHAPTER 12. HARDWARE ENABLEMENT
12.1. UNMAINTAINED HARDWARE SUPPORT
12.2. REMOVED HARDWARE SUPPORT
CHAPTER 13. HIGH AVAILABILITY AND CLUSTERS
13.1. NOTABLE CHANGES TO HIGH AVAILABILITY AND CLUSTERS
CHAPTER 14. IDENTITY MANAGEMENT
14.1. NEW FEATURES
14.2. KNOWN ISSUES
14.3. RELOCATED PACKAGES
14.4. REMOVED FUNCTIONALITY
CHAPTER 15. INFRASTRUCTURE SERVICES
15.1. NOTABLE CHANGES TO INFRASTRUCTURE SERVICES
CHAPTER 16. INSTALLER AND IMAGE CREATION
16.1. INSTALLER
16.2. IMAGE CREATION
CHAPTER 17. KERNEL
17.1. NOTABLE CHANGES TO KDUMP MEMORY ALLOCATION
17.2. NOTABLE CHANGES TO THE RHEL FOR REAL TIME KERNEL
4
5
6
7
8
9
9
9
10
10
12
12
13
13
19
19
21
21
24
24
27
29
29
32
34
34
35
35
37
38
39
42
42
43
43
45
47
47
47
Table of Contents
1

. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
. . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . . .
17.3. NOTABLE CHANGES TO KERNEL
17.4. NOTABLE CHANGES TO BOOT LOADER
CHAPTER 18. NETWORKING
18.1. KERNEL
18.2. NETWORK TYPES
18.3. NETWORKMANAGER
18.4. MPTCP
18.5. FIREWALL
18.6. INFINIBAND AND RDMA NETWORKS
18.7. REMOVED FUNCTIONALITY
CHAPTER 19. PERFORMANCE
19.1. NOTABLE CHANGES TO PERFORMANCE
CHAPTER 20. SECURITY
20.1. SECURITY COMPLIANCE
20.2. CRYPTO-POLICIES, RHEL CORE CRYPTOGRAPHIC COMPONENTS, AND PROTOCOLS
20.3. SELINUX
CHAPTER 21. SHELLS AND COMMAND-LINE TOOLS
21.1. NOTABLE CHANGES TO SYSTEM MANAGEMENT
21.2. NOTABLE CHANGES TO COMMAND-LINE TOOLS
CHAPTER 22. SOFTWARE MANAGEMENT
22.1. NOTABLE CHANGES TO SOFTWARE MANAGEMENT
CHAPTER 23. SUBSCRIPTION MANAGEMENT
23.1. NOTABLE CHANGES TO SUBSCRIPTION MANAGEMENT
CHAPTER 24. SYSTEM ROLES
24.1. PERFORMING SYSTEM ADMINISTRATION TASKS WITH RHEL SYSTEM ROLES
CHAPTER 25. VIRTUALIZATION
25.1. NOTABLE CHANGES TO KVM
25.2. NOTABLE CHANGES TO LIBVIRT
25.3. NOTABLE CHANGES TO QEMU
25.4. NOTABLE CHANGES TO SPICE
CHAPTER 26. THE WEB CONSOLE
26.1. CHANGES TO THE RHEL WEB CONSOLE
APPENDIX A. CHANGES TO PACKAGES
A.1. NEW PACKAGES
A.2. PACKAGE REPLACEMENTS
A.3. MOVED PACKAGES
A.4. REMOVED PACKAGES
A.5. PACKAGES WITH REMOVED SUPPORT
48
49
51
51
51
52
52
52
53
53
54
54
57
57
57
62
64
64
65
66
66
69
69
70
70
72
72
72
73
73
75
75
76
76
131
154
191
265
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
2

Table of Contents
3

PROVIDING FEEDBACK ON RED HAT DOCUMENTATION
We appreciate your feedback on our documentation. Let us know how we can improve it.
Submitting feedback through Jira (account required)
1. Log in to the Jira website.
2. Click Create in the top navigation bar
3. Enter a descriptive title in the Summary field.
4. Enter your suggestion for improvement in the Description field. Include links to the relevant
parts of the documentation.
5. Click Create at the bottom of the dialogue.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
4

CHAPTER 1. PREFACE
This document provides an overview of differences between two major versions of Red Hat
Enterprise Linux: RHEL 8 and RHEL 9. It provides a list of changes relevant for evaluating an upgrade to
RHEL 9 rather than an exhaustive list of all alterations.
For details regarding RHEL 9 usage, see the RHEL 9 product documentation .
For guidance regarding an in-place upgrade from RHEL 8 to RHEL 9, see Upgrading from RHEL 8 to
RHEL 9.
For information about major differences between RHEL 7 and RHEL 8, see Considerations in adopting
RHEL 8.
Capabilities and limits of Red Hat Enterprise Linux 9 as compared to other versions of the system are
available in the Knowledgebase article Red Hat Enterprise Linux technology capabilities and limits .
Information regarding the Red Hat Enterprise Linux life cycle is provided in the Red Hat Enterprise Linux
Life Cycle document.
The Package manifest document provides a package listing for RHEL 9, including licenses and
application compatibility levels.
Application compatibility levels are explained in the Red Hat Enterprise Linux 9: Application
Compatibility Guide document.
CHAPTER 1. PREFACE
5

CHAPTER 2. ARCHITECTURES
Red Hat Enterprise Linux 9 is distributed with the kernel version 5.14, which provides support for the
following architectures at the minimum required version:
AMD and Intel 64-bit architectures (x86-64-v2)
The 64-bit ARM architecture (ARMv8.0-A)
IBM Power Systems, Little Endian (POWER9)
64-bit IBM Z (z14)
Make sure you purchase the appropriate subscription for each architecture.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
6

CHAPTER 3. REPOSITORIES
Red Hat Enterprise Linux 9 is distributed through two main repositories:
BaseOS
AppStream
Both repositories are required for a basic RHEL installation, and are available with all RHEL
subscriptions.
Content in the BaseOS repository is intended to provide the core set of the underlying OS functionality
that provides the foundation for all installations. This content is available in the RPM format and is
subject to support terms similar to those in previous releases of RHEL. For more information, see the
Scope of Coverage Details document.
Content in the AppStream repository includes additional user-space applications, runtime languages,
and databases in support of the varied workloads and use cases.
In addition, the CodeReady Linux Builder repository is available with all RHEL subscriptions. It provides
additional packages for use by developers. Packages included in the CodeReady Linux Builder
repository are unsupported.
Additional resources
Package manifest
CHAPTER 3. REPOSITORIES
7

CHAPTER 4. APPLICATION STREAMS
Multiple versions of user-space components are delivered as Application Streams and updated more
frequently than the core operating system packages. This provides greater flexibility to customize RHEL
without impacting the underlying stability of the platform or specific deployments.
Each Application Stream component has a given life cycle, either the same as RHEL 9 or shorter. For
RHEL life cycle information, see Red Hat Enterprise Linux Life Cycle and Red Hat Enterprise Linux
Application Streams Life Cycle.
Application Streams are available in the following formats:
the familiar RPM format
as an extension to the RPM format called modules
as Software Collections
as Flatpaks.
RHEL 9 improves the Application Streams experience by providing initial Application Stream versions
that can be installed as RPM packages using the traditional dnf install command.
NOTE
Certain initial Application Streams in the RPM format have a shorter life cycle than Red
Hat Enterprise Linux 9.
Some additional Application Stream versions will be distributed as modules with a shorter life cycle in
future minor RHEL 9 releases. It is recommended to review the Red Hat Enterprise Linux Application
Stream Lifecycle definitions for any content life cycle considerations.
Always determine what version of an Application Stream you want to install and make sure to review the
Red Hat Enterprise Linux Application Stream Lifecycle first.
Content that needs rapid updating, such as alternate compilers and container tools, is available in rolling
streams that will not provide alternative versions in parallel. Rolling streams can be packaged as RPMs or
modules.
For information about Application Streams available in RHEL 9 and their application compatibility level,
see the Package manifest. Application compatibility levels are explained in the Red Hat Enterprise Linux
9: Application Compatibility Guide document.
Additional resources
Red Hat Enterprise Linux Life Cycle
Red Hat Enterprise Linux Application Stream Lifecycle
Red Hat Enterprise Linux 9: Application Compatibility Guide
Managing software with the DNF tool
Package manifest
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
8

CHAPTER 5. CLOUD
The following chapters contain the most notable changes to public cloud platforms between RHEL 8
and RHEL 9:
5.1. NOTABLE CHANGES TO AZURE
TDX support is available a Technology Preview for RHEL on Azure
The Intel Trust Domain Extension (TDX) feature can as a Technology Preview now be used in RHEL 9.4
guest operating systems. If the host system supports TDX, you can deploy hardware-isolated RHEL 9
virtual machines (VMs), called trust domains (TDs). As a result, you will be able to create a CVM image
with SecureBoot enabled on the Azure platform.
5.2. NOTABLE CHANGES TO GCP
TDX support is available a Technology Preview for RHEL on GCP
The Intel Trust Domain Extension (TDX) feature can as a Technology Preview now be used in RHEL 9.4
guest operating systems. If the host system supports TDX, you can deploy hardware-isolated RHEL 9
virtual machines (VMs), called trust domains (TDs). With this enhancement, you can use the Intel Trust
Domain Extension (TDX) feature in RHEL 9.4 on Google Cloud Platform.
CHAPTER 5. CLOUD
9

CHAPTER 6. CONTAINERS
The following chapter contains the most notable changes to containers between RHEL 8 and RHEL 9.
6.1. NOTABLE CHANGES TO CONTAINERS
The container-tools meta-package is now available
The container-tools RPM meta-package, which includes Podman, Buildah, Skopeo, CRIU, Udica, and all
required libraries, is available in RHEL 9. The stable streams are not available on RHEL 9. To receive
stable access to Podman, Buildah, Skopeo, and others, use the RHEL EUS subscription.
To install the container-tools meta-package:
Install the container-tools meta-package:
$ sudo dnf install container-tools
Improved control group performance
The previous version of control groups, cgroup version 1 (cgroup v1), caused performance problems with
a variety of applications. The latest release of control groups, cgroup version 2 (cgroup v2) enables
system administrators to limit resources for any application without causing performance problems.
In RHEL 9, the new version of control groups, cgroups v2, is enabled by default.
Podman now supports secure short names
Short-name aliases for images can now be configured in the registries.conf file in the [aliases] table.
The short-names modes are:
Enforcing: If no matching alias is found during the image pull, Podman prompts the user to
choose one of the unqualified-search registries. If the selected image is pulled successfully,
Podman automatically records a new short-name alias in the $HOME/.cache/containers/short-
name-aliases.conf file (rootless user) and in the /var/cache/containers/short-name-
aliases.conf (root user). If the user cannot be prompted (for example, stdin or stdout are not a
TTY), Podman fails. Note that the short-name-aliases.conf file has precedence over
registries.conf file if both specify the same alias. The enforcing mode is default in RHEL 9.
Permissive: Similar to enforcing mode, but Podman does not fail if the user cannot be
prompted. Instead, Podman searches in all unqualified-search registries in the given order. Note
that no alias is recorded. The permissive mode is default in RHEL 8.
Example:
unqualified-search-registries=["registry.fedoraproject.org", "quay.io"]
[aliases]
"fedora"="registry.fedoraproject.org/fedora"
Default container registries in registries.conf
You can find the list of container registries in the /etc/containers/registries.conf file as a root user and
in $HOME/.config/containers/registries.conf as a non-root user. By changing the registries.conf file,
you can change the default system-wide search settings.
For RHEL 8, the unqualified-search-registries is:
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
10

unqualified-search-registries = ["registry.access.redhat.com", "registry.redhat.io", "docker.io"]
short-name-mode = "permissive"
For RHEL 9, the unqualified-search-registries is:
unqualified-search-registries = ["registry.access.redhat.com", "registry.redhat.io", "docker.io"]
short-name-mode = "enforcing"
Default OCI runtime change
The crun OCI runtime is now available for the container-tools:rhel8 module. The crun container
runtime supports an annotation that enables the container to access the rootless user’s additional
groups. This is useful for container operations when volume mounting in a directory where setgid is set,
or when the user only has group access.
The default container runtime in RHEL 8 is runc.
The default container runtime in RHEL 9 is crun.
Running RHEL 9 containers on a RHEL 7 host is not supported
Running RHEL 9 containers on a RHEL 7 host is not supported.
For more information, see Red Hat Enterprise Linux Container Compatibility Matrix .
Default network stacks
Podman uses CNI as the default network stack in RHEL 8 and Netavark as the default network stack in
fresh installs of RHEL 9.
If you perform an in-place upgrade from RHEL 8 to RHEL 9, Podman’s network stack is set as:
Netavark if the network_backend parameter in the /etc/containers/containers.conf file is not
set or if you manually upgraded Podman’s network stack in RHEL 8 to Netavark.
CNI if there are containers, images, pods, or networks presented when Podman is first run after
an upgrade. You can then manually upgrade to the new Netavark network stack. For instructions
on how to switch between the CNI and Netavark network stacks, see 8.6 Switching network
stack from CNI to Netavark and 8.7 Switching the network stack from Netavark to CNI.
Red Hat recommends explicitly specifying the network_backend parameter to ensure that the correct
backend is selected.
WARNING
You cannot migrate the existing containers to a different network stack system
using the podman container checkpoint and the podman container restore
commands. If you want to switch from the CNI network stack to the Netavark
network stack, recreate the container from the container image.
CHAPTER 6. CONTAINERS
11

CHAPTER 7. COMPILERS AND DEVELOPMENT TOOLS
The following chapter contains the most notable changes to compilers and development tools between
RHEL 8 and RHEL 9.
7.1. NOTABLE CHANGES TO GLIBC
All threading APIs now merged into libc.so.6
In RHEL 8, the system threading library, libpthread.so, was a distinct library. In RHEL 9, all threading
APIs have been merged into the core C library libc.so.6. Moving threading into the core C library
enables the library to support threads by default. With a single file the in-place upgrade process is also
made smoother since the thread APIs and core C, POSIX and BSD APIs are all updated at the same
time (no distinct libraries).
Developers can continue to use the -lpthread option when linking threaded applications, but it is no
longer necessary.
Historically, libraries used a weak reference to pthread_create or pthread_cancel to detect if
processes could possibly be multi-threaded. Since this check now always succeeds, because
libpthread.so is now in the core C library, libraries should use the __libc_single_threaded symbol for
this instead.
The libdl library now merged into libc.so.6
In RHEL 8, the libdl library was a distinct library. In RHEL 9, the libdl library has been merged into the
core C library libc.so.6. This means that interposing the dlsym function is now much more difficult.
Applications that need to control the way how symbol resolution works should switch to the auditor
(LD_AUDIT) interfaces.
Name Service Switch service plugins for dns and files now merged into libc.so.6
In RHEL 8, the Name Service Switch (NSS) services for files and dns, which provides data to user and
group identity management APIs, was a distinct plugin. In RHEL 9, the plugins have been merged into
the core C library libc.so.6. Moving the files and dns service providers ensures that applications that
need to cross a mount namespace boundary (for example, enter a container) can do so knowing that
NSS files and dns access services are always loaded at process startup.
When calling user and group APIs, where those APIs depend on an nsswitch.conf that references files
or dns, developers can expect those services to always be present and provide the underlying service
data.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
12

CHAPTER 8. DESKTOP
The following chapter contains the most notable changes to desktop between RHEL 8 and RHEL 9.
8.1. NOTABLE CHANGES TO DESKTOP
GNOME updated to version 40
The GNOME environment is now updated from GNOME 3.28 to GNOME 40 with many new features.
GNOME 40 includes a new and improved Activities Overview design. This gives the overview a more
coherent look, and provides an improved experience for navigating the system and launching
applications. Workspaces are now arranged horizontally, and the window overview and application grid
are accessed vertically.
Other improvements to GNOME include:
The performance and resource usage of GNOME has been significantly improved.
The visual style, including the user interface, the login screen, the icons, and the desktop, has
been refreshed.
GNOME applications no longer use the application menu, which was available from the top
panel. The functionality is now located in a primary menu within the application window.
The Settings application has been redesigned.
Screen sharing and remote desktop sessions have been improved.
If you use the proprietary NVIDIA drivers, you can now launch applications using the discrete
GPU:
a. Open the overview.
b. Right-click the application icon in the dash.
c. Select the Launch on Discrete GPU item in the menu.
The Power Off / Log Out menu now includes the Suspend option and a new Restart option,
which can reboot the system to the boot loader menu when you hold Alt.
Flatpak applications now update automatically.
You can now group application icons in the overview together into folders using drag and drop.
The Terminal application now supports right-to-left and bi-directional text.
The Pointer Location accessibility feature now works in the Wayland session. When the feature
is enabled, pressing Ctrl highlights the pointer location on the screen.
GNOME Shell extensions are now managed by the Extensions application, rather than
Software. The Extensions application handles updating extensions, configuring extension
preferences, and removing or disabling extensions.
The notifications popover now includes a Do Not Disturb button. When the button enabled,
notifications do not appear on the screen.
CHAPTER 8. DESKTOP
13

System dialogs that require a password now have an option to reveal the password text by
clicking the eye () icon.
The Software application now automatically detects metered networks, such as mobile data
networks. When the current network is metered, Software pauses updates in order to reduce
data usage.
Each connected display can now use a different refresh rate in the Wayland session.
Fractional display scaling is available as an experimental option. It includes several preconfigured
fractional ratios.
To enable the experimental fractional scaling, add the scale-monitor-framebuffer value to the
list of enabled experimental features:
$ gsettings set \
org.gnome.mutter experimental-features \
"['scale-monitor-framebuffer']"
As a result, fractional scaling options are accessible on the Display panel in Settings.
NOTE
If the command fails with the following error:
error: Failed to execute child process “dbus-launch” (No such file or directory)
Install the dbus-launch package and repeat the command.
For more details on the changes in GNOME, see versions 3.30 to 40.0 in Release Notes.
X.org Server is now deprecated
The X.org display server is deprecated, and will be removed in a future major RHEL release. The default
desktop session is now the Wayland session in most cases.
The X11 protocol remains fully supported using the XWayland back end. As a result, applications that
require X11 can run in the Wayland session.
Red Hat is working on resolving the remaining problems and gaps in the Wayland session.
You can switch your user session back to the X.org back end. For more information, see Selecting
GNOME environment and display protocol.
The Wayland session is now the default with NVIDIA drivers
When using the NVIDIA drivers, the desktop session now selects the Wayland display protocol by default,
if the driver configuration supports Wayland. In previous RHEL releases, the NVIDIA drivers always
disabled Wayland.
To enable Wayland with the NVIDIA drivers on your system, add the following options to the kernel
command line:
nvidia-drm.modeset=1
NVreg_PreserveVideoMemoryAllocations=1
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
14

Note that Wayland has been the default display protocol with other graphics drivers since RHEL 8.0.
Under certain conditions, the NVIDIA drivers disable the Wayland display protocol and revert to the
X.org display server:
If the version of the NVIDIA driver is lower than 470.
If the system is a laptop that uses hybrid graphics.
If you have not enabled the required NVIDIA driver options.
If the NVIDIA driver has not installed the required systemd services.
Additionally, Wayland is enabled but the desktop session uses X.org by default if the version of the
NVIDIA driver is lower than 510.
Currently, the Wayland session with the NVIDIA drivers is still incomplete and presents certain known
issues. Red Hat is actively working with NVIDIA to address these gaps and problems across the GPU
stack.
X.Org X11 video drivers have been replaced by modesetting
The following X.Org X11 video drivers have been removed and replaced by the generic modesetting
driver:
xorg-x11-drv-ati
xorg-x11-drv-intel
xorg-x11-drv-nouveau
xorg-x11-drv-qxl
xorg-x11-drv-vesa
GPUs supported by RHEL now automatically use the modesetting driver.
If you apply a custom X.Org configuration for any of the removed drivers in RHEL 8 or earlier, your
configuration will have no effect in RHEL 9. Before upgrading to RHEL 9, check your X.Org
configuration files and directories, such as /etc/X11/xorg.conf.d/.
This change does not affect the proprietary NVIDIA driver, which is not maintained by Red Hat.
PipeWire is now the default audio service
The PipeWire service now manages all audio output and input. PipeWire replaces the PulseAudio
service in general use cases and the JACK service in professional use cases. The system now redirects
audio from applications that use PulseAudio, JACK, or the ALSA framework into PipeWire.
Benefits of PipeWire over the previous solutions include:
A unified solution for consumer and professional users
A flexible, modular architecture
High performance and low latency, similar to the JACK service
Isolation between audio clients for better security
CHAPTER 8. DESKTOP
15

You no longer have to configure the JACK service for applications that use it. All JACK applications
now work in the default RHEL configuration.
PulseAudio is still available in RHEL, and you can enable it instead of PipeWire. For details, see
Switching from PipeWire to PulseAudio .
GNOME Boxes have been removed
The GNOME Boxes application has been removed from RHEL 9. Boxes used the SPICE system to
connect to virtual machines (VMs). In RHEL 9, SPICE is no longer available, and as a consequence,
Boxes have also been removed.
If you require Boxes, Red Hat suggests to install Boxes from the Flathub repository: Boxes on Flathub.
This version of Boxes continues to use SPICE, and as a result, it supports the missing features listed
previously.
WARNING
Flathub is a community repository. Red Hat provides no support or guarantees for
Boxes installed from Flathub.
For more information about SPICE in RHEL 9, see the SPICE section.
Power profiles are available in GNOME
You can now switch between several power profiles in the Power panel of Settings in the GNOME
environment. The power profiles optimize various system settings for the selected goal.
The following power profiles are available:
Performance
Optimizes for high system performance and reduces battery life. This profile is only available on
certain selected system configurations.
Balanced
Provides standard system performance and power consumption. This is the default profile.
Power Saver
Increases battery life and reduces system performance. This profile activates automatically on low
battery.
Your power profile configuration persists across system reboots.
The power profiles functionality is available from the power-profiles-daemon package, which is installed
by default.
Lightweight, single-application environment
For graphical use cases that only present a single application, a lightweight user interface (UI) is now
available.
You can start GNOME in a single-application session, also known as kiosk mode. In this session, GNOME
displays only a full-screen window of an application that you have configured.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
16

The single-application session is significantly less resource intensive than the standard GNOME session.
For more information, see Restricting the session to a single application .
Language support is now provided by langpacks
Support for various languages is now available from langpacks packages. You can customize the level
of language support that you want to install using the following package names, where code is the short
ISO code for the language, such as es for Spanish:
langpacks-core-code
Provides a basic language support, including:
The glibc locale
The default font
The default input method if the language requires it
langpacks-core-font-code
Provides only the default font for the language.
langpacks-code
Provides the complete language support, including the following in addition to the basic language
support:
Translations
Spell checker dictionaries
Additional fonts
Motif has been deprecated
The Motif widget toolkit has been deprecated in RHEL, because development in the upstream Motif
community is inactive.
The following Motif packages have been deprecated, including their development and debugging
variants:
motif
openmotif
openmotif21
openmotif22
Additionally, the motif-static package has been removed.
Red Hat recommends using the GTK toolkit as a replacement. GTK is more maintainable and provides
new features compared to Motif.
Several bitmap fonts have been removed
The following bitmap font packages have been removed:
CHAPTER 8. DESKTOP
17

bitmap-console-fonts
bitmap-fixed-fonts
bitmap-fonts-compat
bitmap-lucida-typewriter-fonts
Red Hat has decided to remove these fonts because bitmap fonts have a limited pixel size. When you try
to set a font size that is unavailable, the text might display in a different size or a different font, possibly
a scalable one. This also decreases the rendering quality of bitmap fonts and disrupts the user
experience.
Additionally, the fontconfig system ignores the Portable Compiled Format (PCF), one of the major
bitmap font formats, because it contains no metadata to estimate the language coverage.
Note that the bitmap-fangsongti-fonts bitmap font package continues to be available to support the
Lorax tool.
No Sign In button on the login screen
The login screen has been redesigned in this release. As a consequence, the login screen no longer
includes a Sign In button, which was present in previous RHEL releases.
To confirm your password, press Enter instead.
Note also that the login options button (⚙) is now located in the lower-right corner of the screen.
TigerVNC is deprecated
The TigerVNC remote desktop solution is now deprecated. It will be removed in a future major RHEL
release and replaced by a different remote desktop solution.
TigerVNC provides the server and client implementation of the Virtual Network Computing (VNC)
protocol in RHEL 9.
The following packages are deprecated:
tigervnc
tigervnc-icons
tigervnc-license
tigervnc-selinux
tigervnc-server
tigervnc-server-minimal
tigervnc-server-module
The Connections application (gnome-connections) continues to be supported as an alternative VNC
client, but it does not provide a VNC server.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
18
CHAPTER 9. DYNAMIC PROGRAMMING LANGUAGES, WEB
SERVERS, DATABASE SERVERS
The following chapter contains the most notable changes to dynamic programming languages, web
servers, and database servers between RHEL 8 and RHEL 9.
9.1. NOTABLE CHANGES TO DYNAMIC PROGRAMMING LANGUAGES,
WEB AND DATABASE SERVERS
Initial Application Streams versions in RHEL 9
RHEL 9 improves the Application Streams experience by providing initial Application Stream versions
that can be installed as RPM packages using the traditional dnf install command.
RHEL 9.0 provides the following dynamic programming languages:
Node.js 16
Perl 5.32
PHP 8.0
Python 3.9
Ruby 3.0
RHEL 9.0 includes the following version control systems:
Git 2.31
Subversion 1.14
The following web servers are distributed with RHEL 9.0:
Apache HTTP Server 2.4
nginx 1.20
The following proxy caching servers are available:
Varnish Cache 6.6
Squid 5.2
RHEL 9.0 offers the following database servers:
MariaDB 10.5
MySQL 8.0
PostgreSQL 13
Redis 6.2
Some additional Application Stream versions will be distributed as modules with a shorter life cycle in
future minor RHEL 9 releases.
CHAPTER 9. DYNAMIC PROGRAMMING LANGUAGES, WEB SERVERS, DATABASE SERVERS
19

Major differences in the Python ecosystem since RHEL 8
The unversioned python command
The unversioned form of the python command (/usr/bin/python) is available in the python-
unversioned-command package. On some systems, this package is not installed by default. To install
the unversioned form of the python command manually, use the dnf install /usr/bin/python command.
In RHEL 9, the unversioned form of the python command points to the default Python 3.9 version and
it is an equivalent to the python3 and python3.9 commands. In RHEL 9, you cannot configure the
unversioned command to point to a different version than Python 3.9.
The python command is intended for interactive sessions. In production, it is recommended to use
python3, python3.9, or python3.11 explicitly.
You can uninstall the unversioned python command by using the dnf remove /usr/bin/python
command.
If you need a different python or python3 command, you can create custom symlinks in /usr/local/bin
or ~/.local/bin, or use a Python virtual environment.
Several other unversioned commands are available, such as /usr/bin/pip in the python3-pip package. In
RHEL 9, all unversioned commands point to the default Python 3.9 version.
Architecture-specific Python wheels
Architecture-specific Python wheels built on RHEL 9 newly adhere to the upstream architecture
naming, which allows customers to build their Python wheels on RHEL 9 and install them on non-RHEL
systems. Python wheels built on previous releases of RHEL are forward compatible and can be installed
on RHEL 9. Note that this affects only wheels containing Python extensions, which are built for each
architecture, not Python wheels with pure Python code, which is not architecture-specific.
Notable changes to libdb
RHEL 8 and RHEL 9 currently provide Berkeley DB (libdb) version 5.3.28, which is distributed under the
LGPLv2 license. The upstream Berkeley DB version 6 is available under the AGPLv3 license, which is
more restrictive.
The libdb package is deprecated as of RHEL 9 and might not be available in future major RHEL releases.
Cryptographic algorithms have been removed from libdb in RHEL 9. Multiple libdb dependencies have
been removed from RHEL 9.
Users of libdb are advised to migrate to a different key-value database. For more information, see the
Knowledgebase article Available replacements for the deprecated Berkeley DB (libdb) in RHEL .
Tomcat available since RHEL 9.2
RHEL 9.2 introduces the Apache Tomcat server version 9. Tomcat is the servlet container that is used
in the official Reference Implementation for the Java Servlet and JavaServer Pages technologies. The
Java Servlet and JavaServer Pages specifications are developed by Sun under the Java Community
Process. Tomcat is developed in an open and participatory environment and released under the Apache
Software License version 2.0.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
20
CHAPTER 10. EDGE
The following chapter contains the most notable changes to RHEL Edge between RHEL 8 and RHEL 9.
10.1. RHEL FOR EDGE
This version introduces the following enhancements over the previous versions.
Ability to add SQL backend for storing and querying FDO Owner Vouchers as Technology
Preview
With this Technology Preview, you can select an SQL datastore in the FDO servers options, along with
credentials and other parameters, to store the Owner Vouchers for the following FDO servers:
manufacturer-server
onboarding-server
rendezvous-server
Ability to build FIPS enabled RHEL for Edge images
During the image provisioning, you can build FIPS enabled images for the following RHEL for Edge
image types:
edge-installer
edge-simplified-installer
edge-raw-image
edge-ami
edge-vsphere
Support to build RHEL for Edge AMI images
You have support to build .ami images for RHEL for Edge, customize the blueprint with Ignition to inject
the credentials into the image during boot, and upload the .ami image to AWS and boot an EC2
instance in AWS.
Support to build RHEL for Edge VMDK images
You can also build RHEL for RHEL for Edge VMDK images, customize the blueprint with Ignition to inject
the credentials into the image during the initial boot, and load the image on vSphere and boot the
image in a VM vSphere.
Support for RHEL for Edge minimal raw image that boots on 64-bit ARM architectures
The RHEL for Edge minimal raw image type now supports the 64-bit ARM architecture, and AMD and
Intel 64-bit architectures.
New FIDO Device Onboarding Servers container images available
The following FIDO Device Onboarding Servers container images available in Red Hat Container
Catalog:
rhel9/fdo-manufacturing-server
CHAPTER 10. EDGE
21
rhel9/fdo-owner-onboarding-server
rhel9/fdo-rendezvous-server
rhel9/fdo-serviceinfo-api-server
RHEL for Edge Simplified images have support to the Ignition provisioning utility
You can customize your blueprints configuration with the Ignition provisioning utility to create your
RHEL for Edge images. The Ignition injects the user configuration into the images at an early stage of
the boot process. During the first boot into the system, the Ignition utility reads its configuration either
from a remote URL or a file embedded in the Simplified Installer image and applies that configuration
into the image.
The FDO customization in blueprints is now optional
You are no longer required to add the FDO customization section in blueprints to build a Simplified
Installer image.
Support to specify the user configuration directly in blueprints for the following images:
Simplified Installer images
FDO images
Ignition images
You can create RHEL for Edge Simplified Installer images with RHEL image builder GUI
Previously, the Simplified Installer images could be created only by using the command-line interface.
Support for automatic provisioning and onboarding RHEL for Edge images using FDO
You have support for automatic provisioning and onboarding RHEL for Edge images using the FDO
(FIDO device onboarding) process. With this, you can build a RHEL for Edge Simplified Installer image,
provision it to a RHEL for Edge image. Then, you can use the FDO process to automatically provision
and onboard your Edge devices, exchange data with other devices and systems connected on the
networks.
Support to rpm-ostree upgrades from RHEL 8 to RHEL 9
You can upgrade RHEL 8 systems to RHEL 9 using rpm-ostree rebase.
Support to auto-rollbacks
The health checks run during the boot process and can determine if the nodes are functioning properly.
If the health checks fail, a counter tracks the number of attempts and the node uses rpm-ostree to
rollback the update. Podman automatically rollbacks the container if a new application version exits
when the update fails.
Support to build a RHEL for Edge Simplified Installer image
You can use RHEL image builder to build a RHEL for Edge Simplified Installer image. It enables an
unattended installation to a device, and provisioning the image to a RHEL for Edge image.
Support to build a RHEL for Edge Raw image
You can also build RHEL for RHEL for Edge Raw image. These are compressed raw images, which
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
22

You can also build RHEL for RHEL for Edge Raw image. These are compressed raw images, which
consist of a file that contains a partition layout with an existing deployed OSTree commit in it. The RHEL
for Edge Raw Images can be used to flash on a hard disk drive or boot on a virtual machine.
The RHEL 9 for Edge minimal installation is much smaller
The RHEL 9 for Edge minimal installation is much smaller, when compared with RHEL 8:
Minimal RHEL 8 install Minimal RHEL 9 install Minimal RHEL 9 install (with
firmware & Podman)
302 rpms 244 rpms 292 rpms
1.1G of disk 652M of disk 863M of disk
Supported RHEL for Edge image types
With RHEL for Edge, you can compose customized RHEL (rpm-ostree) images using RHEL image
builder, and then remotely install and manage the images on Edge servers.
The following image types are supported in RHEL 9:
RHEL for Edge Commit (.tar)
RHEL for Edge Container (.tar)
RHEL for Edge Installer (.iso)
RHEL for Edge Raw Image (.raw.xz)
RHEL for Edge Simplified Installer (.iso)
Supported RHEL for Edge image names
Previously, the image types were prefixed by rhel-. This prefix was removed, but the previous image
names, such as rhel-edge-container and rhel-edge-installer still work as aliases to the new names.
These names are considered deprecated and may be removed completely in future versions. The
following RHEL for Edge image names are supported in RHEL 9:
edge-commit
edge-container
edge-installer
CHAPTER 10. EDGE
23

CHAPTER 11. FILE SYSTEMS AND STORAGE
The following chapters contain the most notable changes to file systems and storage between RHEL 8
and RHEL 9.
11.1. FILE SYSTEMS
The XFS filesystem now supports bigtime and inobtcount features
The XFS filesystem now supports two new on-disk features, each of which is enabled by default by
mkfs.xfs in RHEL 9. These two new features are:
Timestamp support beyond the year 2038 (bigtime).
Inode btree counters (inobtcount), to reduce mount time on large filesystems.
As a result of this update, filesystems created with default mkfs.xfs parameters will not be mountable
on RHEL 8 systems.
To create a new filesystem that will be compatible with the RHEL 8 kernel, disable these new features by
adding -m bigtime=0,inobtcount=0 to the mkfs.xfs command line. A filesystem created in this way will
not support timestamps beyond the year 2038.
A filesystem created in RHEL 8 which does not support these features may be upgraded using the
xfs_admin utility on the unmounted block device containing the filesystem. It is recommended to check
the filesystem for consistency prior to this operation. The command will also cause an xfs_repair to be
run on the device after the change.
To enable bigtime support:
xfs_admin -O bigtime=1 /dev/device
To enable inode btree counters:
xfs_admin -O inobtcount=1 /dev/device
To enable both at the same time:
xfs_admin -O bigtime=1,inobtcount=1 /dev/device
See the xfs_admin(8) man page for details.
The exFAT filesystem is now supported in RHEL 9
The exFAT filesystem is now supported in RHEL 9. This is a filesystem designed for external USB
storage and interoperability and data exchange with other operating systems. The filesystem is not
intended as a general-purpose, performant, or scalable Linux filesystem. An exFAT filesystem may be
created by installing the exfatprogs package and using the mkfs.exfat utility.
See the mkfs.exfat(8) man page for details.
ext4 filesystem now supports timestamps beyond the year 2038
The ext4 filesystem is now supporting timestamps beyond the year 2038. This feature is fully automatic
and does not require any user action to leverage it. The only requirement is that the inode size is larger
than 128 bytes, which it is by default.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
24

New nfsv4-client-utils package
New package nfsv4-client-utils, which contains a minimal set of the demons and tool required to
support only NFSv4 has been added. This is a replacement for the standard nfs-utils package.
GFS2 file systems are now created with format version 1802
GFS2 file systems in RHEL 9 are created with format version 1802. This enables the following features:
Extended attributes in the trusted namespace ("trusted.* xattrs") are recognized by gfs2 and
gfs2-utils.
The rgrplvb option is active by default. This allows gfs2 to attach updated resource group data
to DLM lock requests, so the node acquiring the lock does not need to update the resource
group information from disk. This improves performance in some cases.
File systems created with the new format version will not be able to be mounted under earlier RHEL
versions and older versions of the fsck.gfs2 utility will not be able to check them.
Users can create a file system with the older format version by running the mkfs.gfs2 command with
the option -o format=1801.
Users can upgrade the format version of an older file system running tunegfs2 -r 1802 device on an
unmounted file system. Downgrading the format version is not supported.
Options in Samba utilities have been renamed and removed for a consistent user
experience
The Samba utilities have been improved to provide a consistent command-line interface. These
improvements include renamed and removed options. Therefore, to avoid problems after the update,
review your scripts that use Samba utilities, and update them, if necessary.
Samba 4.15 introduces the following changes to the Samba utilities:
Previously, Samba command-line utilities silently ignored unknown options. To prevent
unexpected behavior, the utilities now consistently reject unknown options.
Several command-line options now have a corresponding smb.conf variable to control their
default value. See the man pages of the utilities to identify if a command-line option has an
smb.conf variable name.
By default, Samba utilities now log to standard error (stderr). Use the --debug-stdout option to
change this behavior.
The --client-protection=off|sign|encrypt option has been added to the common parser.
The following options have been renamed in all utilities:
--kerberos to --use-kerberos=required|desired|off
--krb5-ccache to --use-krb5-ccache=CCACHE
--scope to --netbios-scope=SCOPE
--use-ccache to --use-winbind-ccache
The following options have been removed from all utilities:
-e and --encrypt
CHAPTER 11. FILE SYSTEMS AND STORAGE
25

-C removed from --use-winbind-ccache
-i removed from --netbios-scope
-S and --signing
To avoid duplicate options, certain options have been removed or renamed from the following
utilities:
ndrdump: -l is no longer available for --load-dso
net: -l is no longer available for --long
sharesec: -V is no longer available for --viewsddl
smbcquotas: --user has been renamed to --quota-user
nmbd: --log-stdout has been renamed to --debug-stdout
smbd: --log-stdout has been renamed to --debug-stdout
winbindd: --log-stdout has been renamed to --debug-stdout
cramfs module has been removed
Due to lack of users, the cramfs kernel module is removed. squashfs is recommended as an alternative
solution.
Mandatory file locking support has been removed from RHEL 9
Mandatory file locking is no longer supported in RHEL 9 and later versions. The mand mount option is
ignored by this kernel and its use generates a warning in the system log.
NFSv2 is no longer supported
RHEL 9 NFS client and server no longer support NFSv2.
Stratis storage manager is now available
Stratis is a local storage manager. It provides managed file systems on top of pools of storage with
additional features to the user:
Manage snapshots and thin provisioning
Automatically grow file system sizes as needed
Maintain file systems
Pool Level Encryption
TMP2 and NBDE Support
To administer Stratis storage, use the stratis utility, which communicates with the stratisd background
service.
For more information, see the Stratis documentation: Setting up Stratis file systems.
DAX mount option and reflink are now compatible
Reflinked files are now generally compatible with DAX mode. The file system DAX mount option -o
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
26

Reflinked files are now generally compatible with DAX mode. The file system DAX mount option -o
dax=always is compatible with reflink-enabled file systems. Files that were reflinked can be set to DAX
mode using inode flags. For more information see the xfs(5) man page.
11.2. STORAGE
NVMe-FC Boot from SAN is now fully supported
The Non-volatile Memory Express (NVMe) over Fibre Channel (NVMe/FC) Boot, which was introduced
in Red Hat Enterprise Linux 9.2 as a Technology Preview, is now fully supported. Some NVMe/FC host
bus adapters support a NVMe/FC boot capability. For more information on programming a Host Bus
Adapter (HBA) to enable NVMe/FC boot capability, see the NVMe/FC host bus adapter manufacturer’s
documentation.
Converting a standard LV to a thin LV by using lvconvert is now possible
By specifying a standard logical volume (LV) as a thin pool data volume, you can now convert a standard
LV to a thin LV by using the lvconvert command. With this update, you can convert existing LVs to use
the thin provisioning facility.
Integrity targets now generate Audit events
The integrity target now generates Audit events. You can use these Audit events for logging of
additional security-relevant event types.
dm-verity now supports forward error correction
The dm-verity target now supports forward error correction (FEC). With FEC, you can use pre-
generated error correction data to recover from corrupted blocks.
NVMe native multipathing is now enabled by default
Non-volatile Memory Express (NVMe) native multipathing is enabled by default in Red Hat
Enterprise Linux 9 and is the recommended multipathing solution. You can now configure multipathing
on NVMe without using the DM Multipath framework. NVMe native multipathing provides higher
performance.
The default kernel setting for the nvme_core.multipath option is now set to Y, which means that native
NVMe multipathing is enabled.
VDO Management software has been removed
The python-based VDO Management software is no longer available in RHEL 9. Instead of this
software, use the LVM-VDO implementation for managing VDO volumes.
Multiple write policies from VDO has been removed
VDO no longer has multiple write policies. VDO now uses the async write policy exclusively. The 'sync'
and 'async-unsafe' write policies have been removed.
Stratis storage manager is now available
Stratis is a local storage manager. It provides managed file systems on top of pools of storage with
additional features to the user:
Manage snapshots and thin provisioning
Automatically grow file system sizes as needed
CHAPTER 11. FILE SYSTEMS AND STORAGE
27

Maintain file systems
Pool Level Encryption
TMP2 and NBDE Support
To administer Stratis storage, use the stratis utility, which communicates with the stratisd background
service.
For more information, see the Stratis documentation: Setting up Stratis file systems.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
28

CHAPTER 12. HARDWARE ENABLEMENT
The following chapters contain the most notable changes to hardware enablement between RHEL 8 and
RHEL 9.
12.1. UNMAINTAINED HARDWARE SUPPORT
The following devices (drivers, adapters) are available but are no longer tested or updated on a routine
basis in Red Hat Enterprise Linux 9. Red Hat may fix serious bugs, including security bugs, at its
discretion. These devices should no longer be used in production, and it is possible they will be disabled
in the next major release.
PCI device IDs are in the format of vendor:device:subvendor:subdevice. If no device ID is listed, all
devices associated with the corresponding driver are unmaintained. To check the PCI IDs of the
hardware on your system, run the lspci -nn command.
Device ID Driver Device name
dl2k
hdlc_fr
arp_tabl
es
ip_set
ip_table
s
ip6_tabl
es
nft_com
pat
siw
rdma_rx
e
usnic_ve
rbs
vmw_pvr
dma
hfi1
CHAPTER 12. HARDWARE ENABLEMENT
29

bnx2 QLogic BCM5706/5708/5709/5716 Driver
e1000 Intel® PRO/1000 Network Driver
hpsa Hewlett-Packard Company: Smart Array Controllers
0x10df:0x0724 lpfc Emulex Corporation: OneConnect FCoE Initiator (Skyhawk)
0x10df:0xe200 lpfc Emulex Corporation: LPe15000/LPe16000 Series
8Gb/16Gb Fibre Channel Adapter
0x10df:0xf011 lpfc Emulex Corporation: Saturn: LightPulse Fibre Channel Host
Adapter
0x10df:0xf015 lpfc Emulex Corporation: Saturn: LightPulse Fibre Channel Host
Adapter
0x10df:0xf100 lpfc Emulex Corporation: LPe12000 Series 8Gb Fibre Channel
Adapter
0x10df:0xfc40 lpfc Emulex Corporation: Saturn-X: LightPulse Fibre Channel
Host Adapter
0x10df:0xe220 be2net Emulex Corporation: OneConnect NIC (Lancer)
0x1000:0x0071 megarai
d_sas
Broadcom / LSI: MR SAS HBA 2004
0x1000:0x0073 megarai
d_sas
Broadcom / LSI: MegaRAID SAS 2008 [Falcon]
0x1000:0x0079 megarai
d_sas
Broadcom / LSI: MegaRAID SAS 2108 [Liberator]
0x1000:0x005b megarai
d_sas
Broadcom / LSI: MegaRAID SAS 2208 [Thunderbolt]
0x1000:0x006E mpt3sas Broadcom / LSI: SAS2308 PCI-Express Fusion-MPT SAS-2
0x1000:0x0080 mpt3sas Broadcom / LSI: SAS2208 PCI-Express Fusion-MPT SAS-2
0x1000:0x0081 mpt3sas Broadcom / LSI: SAS2208 PCI-Express Fusion-MPT SAS-2
0x1000:0x0082 mpt3sas Broadcom / LSI: SAS2208 PCI-Express Fusion-MPT SAS-2
0x1000:0x0083 mpt3sas Broadcom / LSI: SAS2208 PCI-Express Fusion-MPT SAS-2
Device ID Driver Device name
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
30

0x1000:0x0084 mpt3sas Broadcom / LSI: SAS2208 PCI-Express Fusion-MPT SAS-2
0x1000:0x0085 mpt3sas Broadcom / LSI: SAS2208 PCI-Express Fusion-MPT SAS-2
0x1000:0x0086 mpt3sas Broadcom / LSI: SAS2308 PCI-Express Fusion-MPT SAS-2
0x1000:0x0087 mpt3sas Broadcom / LSI: SAS2308 PCI-Express Fusion-MPT SAS-2
mptbase Fusion MPT SAS Host driver
mptsas Fusion MPT SAS Host driver
mptscsi
h
Fusion MPT SCSI Host driver
mptspi Fusion MPT SAS Host driver
myri10g
e
Myricom 10G driver (10GbE)
netxen_
nic
QLogic/NetXen (1/10) GbE Intelligent Ethernet Driver
0x1077:0x2031 qla2xxx QLogic Corp.: ISP8324-based 16Gb Fibre Channel to PCI
Express Adapter
0x1077:0x2532 qla2xxx QLogic Corp.: ISP2532-based 8Gb Fibre Channel to PCI
Express HBA
0x1077:0x8031 qla2xxx QLogic Corp.: 8300 Series 10GbE Converged Network
Adapter (FCoE)
qla3xxx QLogic ISP3XXX Network Driver v2.03.00-k5
0x1924:0x0803 sfc Solarflare Communications: SFC9020 10G Ethernet
Controller
0x1924:0x0813 sfc Solarflare Communications: SFL9021 10GBASE-T Ethernet
Controller
0x177d:0xa01e nicpf Cavium ThunderX NIC PF driver
0x177d:0xa034 nicvf Cavium ThunderX NIC VF driver
0x177d:0x0011 nicvf Cavium ThunderX NIC VF driver
Device ID Driver Device name
CHAPTER 12. HARDWARE ENABLEMENT
31

nvmet-
fc
NVMe/Fabrics FC target driver
nvmet_t
cp
NVMe/TCP target driver
Device ID Driver Device name
12.2. REMOVED HARDWARE SUPPORT
The following devices (drivers, adapters) have been removed from RHEL 9.
PCI device IDs are in the format of vendor:device:subvendor:subdevice. If no device ID is listed, all
devices associated with the corresponding driver are unmaintained. To check the PCI IDs of the
hardware on your system, run the lspci -nn command.
Device ID Driver Device name
Soft-RoCE (rdma_rxe)
HNS-RoCE HNS GE/10GE/25GE/50GE/100GE RDMA Network
Controller
liquidio Cavium LiquidIO Intelligent Server Adapter Driver
liquidio_vf Cavium LiquidIO Intelligent Server Adapter Virtual
Function Driver
aarch64:Amper
e:Potenza
Ampere eMAG
aarch64:APM:P
otenza
Applied Micro X-Gene
ppc64le:ibm:4d
:*
Power8
ppc64le:ibm:4b
:*
Power8E
ppc64le:ibm:4c:
*
Power8NVL
s390x:ibm:296
4:*
z13
s390x:ibm:296
5:*
z13s
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
32

v4l/dvb television and video capture devices
Device ID Driver Device name
CHAPTER 12. HARDWARE ENABLEMENT
33

CHAPTER 13. HIGH AVAILABILITY AND CLUSTERS
The following chapter contains the most notable changes to high availability and clusters between
RHEL 8 and RHEL 9.
13.1. NOTABLE CHANGES TO HIGH AVAILABILITY AND CLUSTERS
pcs commands that support the clufter tool have been removed
The pcs commands that support the clufter tool for analyzing cluster configuration formats have been
removed. The following commands have been removed:
pcs config import-cman for importing CMAN / RHEL6 HA cluster configuration
pcs config export for exporting cluster configuration to a list of pcs commands which recreate
the same cluster
pcs suppport for OCF Resource Agent API 1.1 standard
The pcs command-line interface now supports OCF 1.1 resource and STONITH agents. As part of the
implementation of this support, any agent’s metadata must comply with the OCF schema, whether the
agent is an OCF 1.0 or OCF 1.1 agent. If an agent’s metadata does not comply with the OCF schema, pcs
considers the agent invalid and will not create or update a resource of the agent unless the --force
option is specified. The pcsd Web UI and pcs commands for listing agents now omit agents with invalid
metadata from the listing.
New pcs parsing requires meta keyword when specifying clone meta attributes
To ensure consistency in the pcs command format, configuring clone meta attributes with the pcs
resource clone, pcs resource promotable, and pcs resource create commands without specifying
the meta keyword is now deprecated.
Previously, the meta keyword was ignored in the pcs resource clone and pcs resource promotable
commands. In the pcs resource create command, however, the meta attributes specified after the
meta keyword when it followed the clone keyword were assigned to the resource rather than to the
clone. With this updated parsing algorithm, meta attributes specified after the meta keyword when it
follows the clone keyword are assigned to the clone. To maintain compatibility with existing scripts
which rely on the older format, you must specify the --future command option to enable this new
argument processing when creating a cloned resource with the pcs resource create command.
The following command now creates a resource with the meta attribute mv=v1 and a clone with the
meta attribute mv=v2:
pcs resource create dummy1 ocf:pacemaker:Dummy meta m1=v1 clone meta m2=v2 --future
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
34

CHAPTER 14. IDENTITY MANAGEMENT
The following chapters contain the most notable changes to Identity Management (IdM) between RHEL
8 and RHEL 9.
14.1. NEW FEATURES
A new passwordless authentication method is available in SSSD
As of RHEL 9.4, you can enable and configure passwordless authentication in SSSD to use a biometric
device that is compatible with the FIDO2 specification, for example a YubiKey. You must register the
FIDO2 token in advance and store this registration information in the user account in RHEL IdM, Active
Directory, or an LDAP store. RHEL implements FIDO2 compatibility with the libfido2 library, which
currently only supports USB-based tokens.
Identity Management API is now fully supported
As of RHEL 9.3, the Identity Management (IdM) API is a fully supported feature.
Users can use existing tools and scripts even if the IdM API is enhanced to enable multiple versions of
API commands. These enhancements do not change the behavior of a command in an incompatible way.
This has the following benefits:
Administrators can use previous or later versions of IdM on the server than on the managing
client.
Developers can use a specific version of an IdM call, even if the IdM version changes on the
server.
The communication with the server is possible, regardless if one side uses, for example, a newer version
that introduces new options for a feature.
NOTE
While IdM API provides a JSON-RPC interface, this type of access is not supported. Red Hat
recommends accessing the API with Python instead. Using Python automates important parts such
as the metadata retrieval from the server, which allows listing all available commands.
Identity Management installation packages have been demodularized
Previously in RHEL 8, IdM packages were distributed as modules, which required you to enable a stream
and install the profile that corresponds to your desired installation. IdM installation packages have been
demodularized in RHEL 9, so you can use the following dnf commands to install IdM server packages:
For a server without integrated DNS services:
# dnf install ipa-server
For a server with integrated DNS services:
# dnf install ipa-server ipa-server-dns
The SSSD implicit files provider domain is disabled by default
The SSSD implicit files provider domain, which retrieves user information from local files such as
/etc/shadow and group information from /etc/groups, is now disabled by default.
CHAPTER 14. IDENTITY MANAGEMENT
35

To retrieve user and group information from local files with SSSD:
1. Configure SSSD. Choose one of the following options:
a. Explicitly configure a local domain with the id_provider=files option in the sssd.conf
configuration file.
[domain/local]
id_provider=files
...
b. Enable the files provider by setting the enable_files_domain=true option in the sssd.conf
configuration file.
[sssd]
enable_files_domain = true
2. Configure the name services switch.
# authselect enable-feature with-files-provider
New realm configuration template for KDC enabling FIPS 140-3-compliant key encryption
This update provides a new, EXAMPLE.COM, example realm configuration in the
/var/kerberos/krb5kdc/kdc.conf file. It brings two changes:
The FIPS 140-3-compliant AES HMAC SHA-2 family is added to the list of supported types for
key encryption.
The encryption type of the KDC master key is switched from AES 256 HMAC SHA-1 to AES
256 HMAC SHA-384.
WARNING
This update is about standalone MIT realms. Do not change the Kerberos
Distribution Center (KDC) configuration in RHEL Identity Management.
Using the new configuration template is recommended for new realms. The template does not affect
any realm already deployed. If you are planning to upgrade the configuration of your realm according to
the template, consider the following points:
For upgrading the master key, changing the setting in the KDC configuration is not enough. Follow the
process described in the MIT Kerberos documentation.
Adding the AES HMAC SHA-2 family to the supported types for key encryption is safe at any point
because it does not affect existing entries in the KDC. Keys will be generated only when creating new
principals or when renewing credentials. Note that keys of this new type cannot be generated based on
existing keys. To make these new encryption types available for a certain principal, its credentials have
to be renewed, which means renewing keytabs for service principals too.
The only case where principals should not feature an AES HMAC SHA-2 key is the Active Directory
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
36

The only case where principals should not feature an AES HMAC SHA-2 key is the Active Directory
(AD) cross-realm ticket-granting ticket (TGT) ones. Because AD does not implement RFC8009, it does
not use the AES HMAC SHA-2 encryption types family. Therefore, a cross-realm TGS-REQ using an
AES HMAC SHA-2-encrypted cross-realm TGT would fail. The best way to keep the MIT Kerberos
client from using AES HMAC SHA-2 against AD is to not provide AES HMAC SHA-2 keys for the AD
cross-realm principals. To do so, ensure that you create the cross-realm TGT entries with an explicit list
of key encryption types that are all supported by AD:
kadmin.local <<EOF
add_principal +requires_preauth -e aes256-cts-hmac-sha1-96,aes128-cts-hmac-sha1-96 -pw
[password] krbtgt/[MIT realm]@[AD realm]
add_principal +requires_preauth -e aes256-cts-hmac-sha1-96,aes128-cts-hmac-sha1-96 -pw
[password] krbtgt/[AD realm]@[MIT realm]
EOF
To ensure the MIT Kerboros clients use the AES HMAC SHA-2 encryption types, you must also set
these encryption types as permitted in both the client and the KDC configuration. On RHEL, this setting
is managed by the crypto-policy system. For example, on RHEL 9, hosts using the DEFAULT crypto-
policy allow AES HMAC SHA-2 and AES HMAC SHA-1 encrypted tickets, while hosts using the FIPS
crypto-policy only accept AES HMAC SHA-2 ones.
Improved SSSD multi-threaded performance
Previously, SSSD serialized parallel requests from multi-threaded applications, such as Red Hat
Directory Server and Identity Management. Starting with RHEL 9.1, all SSSD client libraries, such as nss
and pam, do not serialize requests, therefore allowing requests from multiple threads to be executed in
parallel for better performance.
To enable the previous behavior of serialization, set the environment variable SSS_LOCKFREE to NO.
14.2. KNOWN ISSUES
Users without SIDs cannot log in to IdM after an upgrade
After upgrading your Identity Management (IdM) replica to RHEL 9.2, the IdM Kerberos Distribution
Centre (KDC) might fail to issue ticket-granting tickets (TGTs) to users who do not have Security
Identifiers (SIDs) assigned to their accounts. Consequently, the users cannot log in to their accounts.
To work around the problem, generate SIDs by running the following command as an IdM administrator
on another IdM replica in the topology:
# ipa config-mod --enable-sid --add-sids
Afterward, if users still cannot log in, examine the Directory Server error log. You might have to adjust ID
ranges to include user POSIX identities.
Adding a RHEL 9 replica in FIPS mode to an IdM deployment in FIPS mode that was
initialized with RHEL 8.6 or earlier fails
The default RHEL 9 FIPS cryptographic policy aiming to comply with FIPS 140-3 does not allow the use
of the AES HMAC-SHA1 encryption types' key derivation function as defined by RFC3961, section 5.1.
This constraint does not allow you to add a RHEL 9 IdM replica in FIPS mode to a RHEL 8 IdM
environment in FIPS mode in which the first server was installed on a RHEL 8.6 or earlier systems. This is
because there are no common encryption types between RHEL 9 and the previous RHEL versions, which
CHAPTER 14. IDENTITY MANAGEMENT
37

commonly use the AES HMAC-SHA1 encryption types but do not use the AES HMAC-SHA2 encryption
types.
To work around the problem, enable the use of AES HMAC-SHA1 on the RHEL 9 replica:
# update-crypto-policies --set FIPS:AD-SUPPORT
By setting the cryptographic policy to FIPS:AD-SUPPORT, you are adding the following encryption
types to the list of already allowed encryption types that comply with FIPS 140-3:
aes256-cts:normal
aes256-cts:special
aes128-cts:normal
aes128-cts:special
As a result, adding the RHEL 9 replica to the IdM deployment proceeds correctly.
NOTE
There is ongoing work to provide a procedure to generate missing AES HMAC-SHA2-
encrypted Kerberos keys on RHEL 7 and RHEL 8 servers. This will achieve FIPS 140-3
compliance on the RHEL 9 replica. However, this process cannot be fully automated,
because the design of Kerberos key cryptography makes it impossible to convert existing
keys to different encryption types. The only way is to ask users to renew their passwords.
NOTE
You can view the encryption type of your IdM master key by entering the following
command on the first IdM server in the RHEL 8 deployment:
# kadmin.local getprinc K/M | grep -E '^Key:'
If the string in the output contains the sha1 term, you must enable the use of AES
HMAC-SHA1 on the RHEL 9 replica.
WARNING
Microsoft’s Active Directory implementation does not yet support any of the
RFC8009 Kerberos encryption types that use SHA-2 HMAC. If you have an IdM-AD
trust configured, FIPS:AD-SUPPORT crypto subpolicy use is therefore required
even if the encryption type of your IdM master key is aes256-cts-hmac-sha384-
192.
14.3. RELOCATED PACKAGES
ansible-freeipa is now available in the AppStream repository with all dependencies
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
38

Previously in RHEL 8.5 and earlier, before installing the ansible-freeipa package, you first had to enable
the Ansible repository and install the ansible package. In RHEL 9, you can install ansible-freeipa
without any preliminary steps. Installing ansible-freeipa automatically installs ansible-core as a
dependency. Both packages are available in the rhel-9-for-x86_64-appstream-rpms repository.
ansible-freeipa in RHEL 9 contains all the modules that it contained in RHEL 8.5 and earlier.
Clustered Samba packages are now available from the Resilient Storage and Gluster
Samba Repository
The ctdb clustered Samba packages are now available from the Resilient Storage and Gluster Samba
Repository. Previously in RHEL 8, clustered Samba packages were available from the BaseOS
repository.
14.4. REMOVED FUNCTIONALITY
The nss-pam-ldapd package has been removed
The nss-pam-ldapd package has been removed from RHEL. Red Hat recommends migrating to SSSD
and its ldap provider, which fully replaces the functionality of the nslcd service. SSSD has features that
specifically address the needs of nss-pam-ldapd users, such as:
hosts databases
networks databases
services databases
NIS packages have been removed
The following Network Information Service (NIS) components have been removed from RHEL:
nss_nis
yp-tools
ypbind
ypserv
There is no direct replacement with fully compatible features because the NIS technology is based on
outdated design patterns and is no longer considered secure.
Red Hat recommends using RHEL Identity Management and SSSD instead.
The openssh-ldap package has been removed
As the openssh-ldap subpackage is not maintained upstream, it has been removed from RHEL. Red Hat
recommends using SSSD and the sss_ssh_authorizedkeys helper, which integrate better with other
IdM solutions and are more secure.
By default, the SSSD ldap and ipa providers read the sshPublicKey LDAP attribute of the user object,
if available. Note that you cannot use the default SSSD configuration for the ad provider or IdM trusted
domains to retrieve SSH public keys from Active Directory (AD), since AD does not have a default LDAP
attribute to store a public key.
To allow the sss_ssh_authorizedkeys helper to get the key from SSSD, enable the ssh responder by
adding ssh to the services option in the sssd.conf file. See the sssd.conf(5) man page for details.
CHAPTER 14. IDENTITY MANAGEMENT
39

To allow sshd to use sss_ssh_authorizedkeys, add the following options to the /etc/ssh/sshd_config
file as described by the sss_ssh_authorizedkeys(1) man page:
AuthorizedKeysCommand /usr/bin/sss_ssh_authorizedkeys
AuthorizedKeysCommandUser nobody
The custodia package has been removed
The custodia package has been integrated into Red Hat Identity Management in RHEL 9 and is no
longer shipped as a separate service.
The gssntlmssp package has been removed
As Windows New Technology LAN Manager (NTLM) is considered insecure, the gssntlmssp package
has been removed.
The nsslapd-conntablesize configuration parameter has been removed from 389-ds-base
The nsslapd-conntablesize configuration parameter has been removed from the 389-ds-base package
in RHEL 9.3. Previously, the nsslapd-conntablesize configuration attribute specified the size of the
connection table that managed established connections. With the introduction of the multi-listener
feature, which improves the management of established connections, Directory Server now calculates
the size of the connection table dynamically. This also resolves issues, when the connection table size
was set too low and it affected the number of connections the server was able to support. Starting with
RHEL 9.3, use only nsslapd-maxdescriptors and nsslapd-reservedescriptors attributes to manage
the number of TCP/IP connections Directory Server can support.
Limited support for FreeRADIUS
In RHEL 9, the following external authentication modules are not supported as part of the FreeRADIUS
offering:
The MySQL, PostgreSQL, SQlite, and unixODBC database connectors
The Perl language module
The REST API module
NOTE
The PAM authentication module and other authentication modules that are provided as
part of the base package are not affected.
You can find replacements for the removed modules in community-supported packages, for example in
the Fedora project.
In addition, the scope of support for the freeradius package is now limited to the following use cases:
Using FreeRADIUS as an authentication provider with Identity Management (IdM) as the
backend source of authentication. The authentication is happening through the krb5 and LDAP
authentication packages or as PAM authentication in the main FreeRADIUS package.
Using FreeRADIUS to provide a source-of-truth for authentication in IdM, through the Python
3 authentication package.
In contrast to these removals, Red Hat is now strengthening its support of the following external
authentication modules with FreeRADIUS:
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
40

Authentication based on krb5 and LDAP
Python 3 authentication
The focus on these integration options is in close alignment with the strategic direction of Red Hat IdM.
CHAPTER 14. IDENTITY MANAGEMENT
41

CHAPTER 15. INFRASTRUCTURE SERVICES
The following chapter contains the most notable changes to infrastructure services between RHEL 8
and RHEL 9.
15.1. NOTABLE CHANGES TO INFRASTRUCTURE SERVICES
Support for Berkeley DB dynamic back end has been removed
With this release, the Berkeley DB (libdb) dynamic back end is no longer supported. The named-sdb
build is no longer provided. You can use the DLZ loadable plugins for each back end, for example,
sqlite3 or mysql. Those plugins are not built or shipped and have to be built from the source.
The mod_php module provided with PHP for use with the Apache HTTP Server has been
removed
The mod_php module provided with PHP for use with the Apache HTTP Server is no longer available in
RHEL 9.
Since RHEL 8, PHP scripts are run using the FastCGI Process Manager (php-fpm) by default. For more
information, see Using PHP with the Apache HTTP Server .
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
42

CHAPTER 16. INSTALLER AND IMAGE CREATION
The following chapters contain the most notable changes to installer and image creation between RHEL
8 and RHEL 9.
16.1. INSTALLER
Anaconda activates network automatically for interactive installations
Anaconda now activates the network automatically when performing interactive installation, without
requiring users to manually activate it in the network spoke. This update does not change the installation
experience for Kickstart installations and installations using the ip= boot option.
New options to Lock root account and Allow root SSH login with password
RHEL 9 adds following new options to the root password configuration screen:
Lock root account: To lock the root access to the machine.
Allow root SSH login with password: To enable password-based SSH root logins.
During Kickstart installations, you can enable root access via SSH with password by using the --allow-
ssh option of the rootpw Kickstart command. For more information, see rootpw (required).
Licensing, system, and user setting configuration screens have been disabled post
standard installation
Previously, RHEL users configured Licensing, System (Subscription manager), and User Settings prior
to gnome-initial-setup and login screens. Starting with RHEL 9, the initial setup screens have been
disabled by default to improve user experience. If you must run the initial setup for user creation or
license display, install the following packages based on the requirements.
1. To install initial setup packages:
# dnf install initial-setup initial-setup-gui
2. To enable initial setup after the next reboot of the system.
# systemctl enable initial-setup
3. Reboot the system to view initial setup.
For Kickstart installations, add initial-setup-gui to the packages section and enable the initial-setup
service.
firstboot --enable
%packages
@^graphical-server-environment
initial-setup-gui
%end
The rhsm command for machine provisioning through Kickstart for Satellite is now
available
The rhsm command replaces the %post scripts for machine provisioning on RHEL 9. The rhsm
CHAPTER 16. INSTALLER AND IMAGE CREATION
43

The rhsm command replaces the %post scripts for machine provisioning on RHEL 9. The rhsm
command helps with all provisioning tasks such as registering the system, attaching RHEL subscriptions,
and installing from a Satellite instance.
New Kickstart command - timesource
The new timesource Kickstart command is optional and it helps to set NTP, NTS servers, and NTP pools
that provide time data. It also helps to control enabling or disabling the NTP services on the system. The
--ntpservers option from the timezone command has been deprecated and has been replaced with this
new command.
Support for Anaconda boot arguments without inst. prefix is no longer available
Anaconda boot arguments without the inst. prefix have been deprecated since RHEL 7. Support for
these boot arguments has been removed in RHEL 9. To continue using these options, use the inst.
prefix
For example, to force the installation program to run in the text mode instead of the graphical mode,
use the following option:
inst.text
Removed Kickstart commands and options
The following Kickstart commands and options have been removed from RHEL 9. Using them in
Kickstart files causes an error.
device
deviceprobe
dmraid
install - use the subcommands or methods directly as commands
multipath
bootloader --upgrade
ignoredisk --interactive
partition --active
harddrive --biospart
autostep
Where only specific options and values are listed, the base command and its other options are still
available and not removed.
Removed boot options
The following boot options have been removed from Red Hat Enterprise Linux:
inst.zram
RHEL 9 does not support the zram service. See the zram-generator(8) man page for more
information.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
44

inst.singlelang
The single language mode is not supported on RHEL 9.
inst.loglevel
The log level is always set to debug.
16.2. IMAGE CREATION
This version introduces the following enhancements over the previous versions.
Blueprints now support adding a tailoring file for scap security profile
Starting with 9.4, RHEL image builder supports OpenSCAP customizations in the blueprint by adding a
tailoring file for scap security profile. You can add customized tailoring options for a profile to the
osbuild-composer blueprint customizations by using the following options:
selected for the list of rules that you want to add.
unselected for the list of rules that you want to remove.
When you build an image from the blueprint customized with tailoring file for scap security profile, it
creates a tailoring file with a new tailoring profile ID and saves it to the image as
/usr/share/xml/osbuild-oscap-tailoring/tailoring.xml. The new profile ID will have _osbuild_tailoring
appended as a suffix to the base profile, for example,
xccdf_org.ssgproject.content_profile_cis_osbuild_tailoring, if you use the cis base profile.
AWS EC2 images now support both BIOS and UEFI boot
This update extends the AWS EC2 AMD or Intel 64-bit architecture .ami images created by RHEL
image builder to support UEFI boot, in addition to the legacy BIOS boot.
Support to build VMware VSphere (OVA)
RHEL image builder can build VMware VSphere Open Virtual Appliance (OVA) files that you can deploy
more easily to VMware vSphere by using the vSphere GUI client.
A new and improved way to create blueprints and images in the RHEL image builder web
console
With the new unified version of the image builder tool, you can much more easily create blueprints and
images. Notable enhancements include the following:
You can now use all the customizations previously supported only in the command-line
interface, such as kernel, file system, firewall, locale, and other customizations, in the image
builder web console.
You can import, export, and save blueprints in the .JSON or .TOML format.
Ability to create images with support to different partitioning modes
With RHEL image builder, you can build VMware VSphere Open Virtual Appliance (OVA) files. You can
deploy such files to VMware vSphere by using the vSphere GUI client .
Filesystem customization policy changes in image builder
The following policy changes are in place when using the RHEL image builder filesystem customization in
blueprints:
CHAPTER 16. INSTALLER AND IMAGE CREATION
45

You can set the`mountpoint` and minimum partition minsize entries in the blueprint.
The following image types do not support filesystem customizations:
image-installer
edge-installer
edge-simplified-installer
The following image types do not create partitioned operating systems images.
edge-commit
edge-container
tar
container
Customizing the filesystem of such images has no result.
The blueprint now supports the mountpoint customization for the tpm directory and its sub-
directories.
RHEL image builder supports creating customized files and directories in the /etc directory
With the new`[[customizations.files]]` and the [[customizations.directories]] blueprint
customizations, you can create customized files and directories in the /etc image directory. Currently,
these customizations are only available in the /etc directory. You can use the customizations for all
available image types, except image types that deploy OSTree commits, such as:
edge-raw-image
edge-installer
edge-simplified-installer
.vhd images built with RHEL image builder now have support for 64-bit ARM
You can now build .vhd images using image builder and upload them to the Microsoft Azure cloud.
RHEL image builder supports customized file system partitions on LVM
With support for customized file system partitions on LVM, if you add any file system customization to
your system, the file systems are converted to an LVM partition.
RHEL image builder now supports file system configuration
As of Red Hat Enterprise Linux 9.0, Image Builder provides support for users to specify a custom
filesystem configuration in blueprints to create images with a specific disk layout, instead of using the
default layout configuration.
RHEL image builder can create bootable ISO Installer images
You can use image uilder GUI and CLI to create bootable ISO Installer images. These images consist of
a tar file that contains a root file system which you can use to install directly to a bare metal server.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
46

CHAPTER 17. KERNEL
The following chapters contain the most notable changes to kernel between RHEL 8 and RHEL 9.
17.1. NOTABLE CHANGES TO KDUMP MEMORY ALLOCATION
The kexec-tools package now supports the default crashkernel memory reservation values
for RHEL 9
The kexec-tools package now maintains the default crashkernel memory reservation values. The
kdump service uses the default value to reserve the crashkernel memory for each kernel. This
implementation also improves memory allocation for kdump when a system has less than 4GB of
available memory.
If the memory reserved by the default crashkernel value is not sufficient on your system, you can
increase the crashkernel parameter using the default value as a reference.
To query the default crashkernel value:
$ kdumpctl get-default-crashkernel
Note that the crashkernel=auto option in the boot command line is no longer supported on RHEL 9
and later releases.
For more information, see the /usr/share/doc/kexec-tools/crashkernel-howto.txt file.
17.2. NOTABLE CHANGES TO THE RHEL FOR REAL TIME KERNEL
The TPM 1.2 secure cryptoprocessor is no longer supported on RHEL 9
The Trusted Platform Module (TPM) secure cryptoprocessor version 1.2 has been removed and is no
longer supported on RHEL 9 and later versions. TPM 2.0 replaces TPM 1.2 and provides many
improvements over TPM 1.2. TPM 2.0 is not backward compatible.
Note that for applications that require support for TPM 1.2, Red Hat recommends that you use RHEL 8.
Dynamic preemptive scheduling enabled on ARM, AMD, and Intel 64-bit architectures
Using Dynamic Scheduling, you can change the preemption mode of the kernel at boot or runtime
instead of compile time. With dynamic preemptive handling, you can override the default preemption
model to improve scheduling latency.
The /sys/kernel/debug/sched/preempt file contains the current setting that supports runtime
modification. Using the DYNAMIC_PREEMPT option, set the preempt= variable at boot to either none,
voluntary or full. The voluntary preemption is the default.
A new command line interface has been added to the tuna tool
The tuna tool now provides a command line interface with more standardized menu of commands and
options that is easier to use and maintain. The new command line interface is based on the argparse
parsing module. With this enhancement, you can perform the following tasks:
Change the attributes of the application and kernel threads.
Operate on interrupt requests (IRQs) by name or number.
CHAPTER 17. KERNEL
47

Operate on tasks or threads by using the process identifier.
Specify CPUs and sets of CPUs with the CPU or the socket number.
By using the tuna -h command, you can print the command line arguments and their corresponding
options. For each command, there are optional arguments, which you can view with the tuna
[command] -h command.
The runtime verification mechanism available for real-time kernel
Runtime verification is a lightweight and rigorous method to check the behavioral equivalence between
system events and its formal specifications. Runtime verification has monitors integrated in the kernel
that attach to tracepoints. If a state deviates from defined specifications, the runtime verification
program activates reactors to inform or enable a reaction such as capturing the event in the log file or a
system shutdown to avoid failure propagation in an extreme case.
For more information see, Optimizing RHEL 9 for Real Time for low latency operation .
CONFIG_RT_GROUP_SCHED is disabled in RHEL 9
In RHEL 8, the default control group was cgroups v1, and you could specify CPU bandwidth for
realtime tasks on a per cgroup basis by using control files, for example,
/sys/fs/cgroup/cpu,cpuacct/cpu.rt_period_us and /sys/fs/cgroup/cpu,cpuacct/cpu.rt_runtime_us.
However, in RHEL 9, the CONFIG_RT_GROUP_SCHED kernel configuration option is disabled because
cgroups v2 is the default control group and the equivalent control files do not exist for the cgroups v2
CPU controller. Note that the /proc/sys/kernel/sched_rt_runtime_us and
/proc/sys/kernel/sched_rt_period_us global settings are still available, and you can use them with the
stalld background process to prevent CPU time starvation.
17.3. NOTABLE CHANGES TO KERNEL
The 64k page size kernel
In addition to the RHEL 9 for ARM kernel which supports 4k pages, Red Hat now offers an optional
kernel package that supports 64k pages: kernel-64k.
The 64k page size kernel is a useful option for large datasets on ARM platforms. It enables better
performance for some types of memory- and CPU-intensive operations.
You must choose page size on 64-bit ARM architecture systems at the time of installation. You can
install kernel-64k only by Kickstart by adding the kernel-64k package to the package list in the
Kickstart file.
For more information about installing kernel-64k, see Installing Kernel-64k on ARM .
cgroup-v2 enabled by default in RHEL 9
The control groups version 2 (cgroup-v2) feature implements a single hierarchy model that simplifies
the management of control groups. Also, it ensures that a process can only be a member of a single
control group at a time. Deep integration with systemd improves the end-user experience when
configuring resource control on a RHEL system.
Development of new features is mostly done for cgroup-v2, which has some features that are missing in
cgroup-v1. Similarly, cgroup-v1 contains some legacy features that are missing in cgroup-v2. Also, the
control interfaces are different. Therefore, third party software with direct dependency on cgroup-v1
may not run properly in the cgroup-v2 environment.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
48

To use cgroup-v1, you need to add the following parameters to the kernel command-line:
systemd.unified_cgroup_hierarchy=0
systemd.legacy_systemd_cgroup_controller
NOTE
Both cgroup-v1 and cgroup-v2 are fully enabled in the kernel. There is no default control
group version from the kernel point of view, and is decided by systemd to mount at
startup.
Kernel changes potentially affecting third party kernel modules
Linux distributions with a kernel version prior to 5.9 supported exporting GPL functions as non-GPL
functions. As a result, users could link proprietary functions to GPL kernel functions through the shim
mechanism. With this release, the RHEL kernel incorporates upstream changes that enhance the ability
of RHEL to enforce GPL by rebuffing shim.
IMPORTANT
Partners and independent software vendors (ISVs) should test their kernel modules with
an early version of RHEL 9 to ensure their compliance with GPL.
Core scheduling is supported in RHEL 9
With the core scheduling functionality users can prevent tasks that should not trust each other from
sharing the same CPU core. Likewise, users can define groups of tasks that can share a CPU core.
These groups can be specified:
To improve security by mitigating some cross-Symmetric Multithreading (SMT) attacks
To isolate tasks that need a whole core. For example for tasks in real-time environments, or for
tasks that rely on specific processor features such as Single Instruction, Multiple Data (SIMD)
processing
For more information, see Core Scheduling.
The kernelopts environment variable has been removed in RHEL 9
In RHEL 8, the kernel command-line parameters for systems using the GRUB2 bootloader were defined
in the kernelopts environment variable. This variable was stored in the /boot/grub2/grubenv file for
each kernel boot entry. However, storing the kernel command-line parameters using kernelopts was
not robust. Therefore, Red Hat removed kernelopts and the kernel command-line parameters are now
stored in the Boot Loader Specification (BLS) snippet, instead of in the
/boot/loader/entries/<KERNEL_BOOT_ENTRY>.conf file.
Red Hat protects kernel symbols only for minor releases
Red Hat guarantees that a kernel module will continue to load in all future updates within an Extended
Update Support (EUS) release, only if you compile the kernel module using protected kernel symbols.
There is no kernel Application Binary Interface (ABI) guarantee between minor releases of RHEL 9.
17.4. NOTABLE CHANGES TO BOOT LOADER
Boot loader menu hidden by default
CHAPTER 17. KERNEL
49

Boot loader menu hidden by default
Starting with RHEL 9.1, the GRUB boot loader is now configured to hide the boot menu by default if
RHEL is the only installed operating system and if the previous boot succeeded. This results in a
smoother boot experience on such systems.
To access the boot menu, use one of the following options:
Repeatedly press Esc after booting the system.
Repeatedly press F8 after booting the system.
Hold Shift during boot.
To disable this function and configure the boot loader menu to display by default, use the following
command:
# grub2-editenv - unset menu_auto_hide
Boot loader configuration files are unified across CPU architectures
Configuration files for the GRUB boot loader are now stored in the /boot/grub2/ directory on all
supported CPU architectures. The /boot/efi/EFI/redhat/grub.cfg file, which GRUB previously used as
the main configuration file on UEFI systems, now simply loads the /boot/grub2/grub.cfg file.
This change simplifies the layout of the GRUB configuration file, improves user experience, and
provides the following notable benefits:
You can boot the same installation with either EFI or legacy BIOS.
You can use the same documentation and commands for all architectures.
GRUB configuration tools are more robust, because they no longer rely on symbolic links and
they do not have to handle platform-specific cases.
The usage of the GRUB configuration files is aligned with images generated by CoreOS
Assembler (COSA) and OSBuild.
The usage of the GRUB configuration files is aligned with other Linux distributions.
RHEL no longer boots on 32-bit UEFI
Support for the 32-bit UEFI firmware was removed from the GRUB and shim boot loaders. As a
consequence, RHEL 9 requires a 64-bit UEFI, and can no longer boot on 64-bit systems that use a 32-
bit UEFI.
The following packages have been removed as part of this change:
grub2-efi-ia32
grub2-efi-ia32-cdboot
grub2-efi-ia32-modules
shim-ia32
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
50
CHAPTER 18. NETWORKING
The following chapters contain the most notable changes to networking between RHEL 8 and RHEL 9.
18.1. KERNEL
WireGuard VPN is available as a Technology Preview
WireGuard, which Red Hat provides as an unsupported Technology Preview, is a high-performance VPN
solution that runs in the Linux kernel. It uses modern cryptography and is easier to configure than other
VPN solutions. Additionally, the small code-basis of WireGuard reduces the surface for attacks and,
therefore, improves the security.
For further details, see Setting up a WireGuard VPN .
The PRP and HSR protocols are available as a Technology Preview
Starting with RHEL 9.3, the hsr kernel module is available as an unsupported Technology Preview. The
module provides the following protocols:
Parallel Redundancy Protocol (PRP)
High-availability Seamless Redundancy (HSR)
The IEC 62439-3 standard defines these protocols, and you can use this feature to configure zero-loss
redundancy in Ethernet networks.
Segment Routing over IPv6 (SRv6) is available as a Technology Preview
The RHEL 9.3 kernel provides Segment Routing over IPv6 (SRv6) as an unsupported Technology
Preview. You can use this functionality to optimize traffic flows in edge computing or to improve
network programmability in data centers. However, the most significant use case is the end-to-end
(E2E) network slicing in 5G deployment scenarios. In that area, the SRv6 protocol provides you with the
programmable custom network slices and resource reservations to address network requirements for
specific applications or services. At the same time, the solution can be deployed on a single-purpose
appliance, and it satisfies the need for a smaller computational footprint.
NetworkManager and the Nmstate API support MACsec hardware offload
You can use both NetworkManager and the Nmstate API to enable MACsec hardware offload if the
hardware supports this feature. As a result, you can offload MACsec operations, such as encryption,
from the CPU to the network interface card.
Note that this feature is an unsupported Technology Preview.
18.2. NETWORK TYPES
Network teams are deprecated
The teamd service and the libteam library are deprecated in Red Hat Enterprise Linux 9 and will be
removed in the next major release. As a replacement, configure a bond instead of a network team.
Red Hat focuses its efforts on kernel-based bonding to avoid maintaining two features, bonds and
teams, that have similar functions. The bonding code has a high customer adoption, is robust, and has an
active community development. As a result, the bonding code receives enhancements and updates.
For details about how to migrate a team to a bond, see Migrating a network team configuration to
CHAPTER 18. NETWORKING
51

For details about how to migrate a team to a bond, see Migrating a network team configuration to
network bond.
18.3. NETWORKMANAGER
NetworkManager stores new network configurations in a key file format
Previously, NetworkManager stored new network configurations to /etc/sysconfig/network-scripts/ in
the ifcfg format. Starting with RHEL 9.0, RHEL stores new network configurations at
/etc/NetworkManager/system-connections/ in a key file format. The connections for which the
configurations are stored to /etc/sysconfig/network-scripts/ in the old format still work uninterrupted.
Modifications in existing profiles continue updating the older files.
If Red Hat adds support for more connection profile properties, note that these properties work only in
profiles in keyfile format.
The WEP Wi-Fi connection method has been removed
The insecure wired equivalent privacy (WEP) Wi-Fi connection method has been removed from RHEL 9.
For secure Wi-Fi connections, use the Wi-Fi Protected Access 3 (WPA3) or WPA2 connection methods.
18.4. MPTCP
The mptcpd service is available
With this update the mptcpd service is available for usage. It is a user space based MPTCP path
manager with integrated mptcpize tool.
The mptcpd service provides the simplified automatic configuration of the MPTCP`paths. It benefits
with better reliability of the `MPTCP socket in case of network failure or reconfiguration.
Now you can use the mptcpize tool to enable the MPTCP protocol on the existing systemd units
without additional external dependencies.
18.5. FIREWALL
The ipset and iptables-nft packages have been deprecated
The ipset and iptables-nft packages have been deprecated in RHEL. The iptables-nft package
contains different tools such as iptables, ip6tables, ebtables and arptables. These tools will no longer
receive new features and using them for new deployments is not recommended. As a replacement, it is
recommended to use the nft command line tool provided by the nftables package. Existing setups
should migrate to nft when possible.
For more information about migrating to nftables, see Migrating from iptables to nftables , as well as the
iptables-translate(8) and ip6tables-translate(8) man pages.
The unsupported xt_u32 Netfilter module has been removed
RHEL 8 contained the unsupported xt_u32 module, which enabled iptables users to match arbitrary 32
bits in the packet header or payload. This module has been removed from RHEL 9. As a replacement,
use the nftables packet filtering framework. If no native match exists in nftables, use the raw payload
matching feature of nftables. For details, see the raw payload expression section in the nft(8) man
page.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
52

18.6. INFINIBAND AND RDMA NETWORKS
The ibdev2netdev script has been removed from RHEL 9
ibdev2netdev was a helper utility that was able to display all the associations between network devices
and Remote Direct Memory Access (RDMA) adapter ports. Previously, Red Hat was including
ibdev2netdev in the rdma-core package. From Red Hat Enterprise Linux 9, ibdev2netdev has been
removed and replaced by the rdmatool utility. Now, the iproute package includes rdmatool.
18.7. REMOVED FUNCTIONALITY
RHEL 9 does not contain the legacy network scripts
RHEL 9 does not contain the network-scripts package that provided the deprecated legacy network
scripts in RHEL 8. To configure network connections in RHEL 9, use NetworkManager. For details, see
the Configuring and managing networking documentation.
The unsupported xt_u32 Netfilter module has been removed
RHEL 8 contained the unsupported xt_u32 module, which enabled iptables users to match arbitrary 32
bits in the packet header or payload. This module has been removed from RHEL 9. As a replacement,
use the nftables packet filtering framework. If no native match exists in nftables, use the raw payload
matching feature of nftables. For details, see the raw payload expression section in the nft(8) man
page.
Data Encryption Standard (DES) algorithm is not available for net-snmp communication in
Red Hat Enterprise Linux 9
In previous versions of RHEL, DES was used as an encryption algorithm for secure communication
between net-snmp clients and servers. In RHEL 9, the DES algorithm isn’t supported by the OpenSSL
library. The algorithm is marked as insecure and hence the DES support for net-snmp has been
removed.
CHAPTER 18. NETWORKING
53

CHAPTER 19. PERFORMANCE
The following chapter contains the most notable changes to performance between RHEL 8 and RHEL 9.
19.1. NOTABLE CHANGES TO PERFORMANCE
Performance Co-Pilot rebased to version 6.0
Starting in RHEL 9.2, Performance Co-Pilot (PCP) has been updated to version 6.0. Notable
improvements include:
1. Version 3 PCP archive support:
This includes support for instance domain change-deltas, Y2038-safe timestamps,
nanosecond-precision timestamps, arbitrary timezones support, and 64-bit file offsets used
throughout for larger (beyond 2GB) individual volumes.
This feature is currently opt-in via the PCP_ARCHIVE_VERSION setting in the /etc/pcp.conf
file.
Version 2 archives remain the default.
2. Only OpenSSL is used throughout PCP. Mozilla NSS/NSPR use has been dropped:
This impacts libpcp, PMAPI clients and PMCD use of encryption. These elements are now
configured and used consistently with pmproxy HTTPS support and redis-server, which were
both already using OpenSSL.
3. New nanosecond precision timestamp PMAPI calls for PCP library interfaces that make use of
timestamps.
These are all optional, and full backward compatibility is preserved for existing tools.
4. The following tools and services have been updated:
pcp2elasticsearch
Implemented authentication support.
pcp-dstat
Implemented support for the top-alike plugins.
pcp-htop
Updated to the latest stable upstream release.
pmseries
Added sum, avg, stdev, nth_percentile, max_inst, max_sample, min_inst and
min_sample functions.
pmdabpf
Added CO-RE (Compile Once - Run Everywhere) modules and support for AMD64, Intel
64-bit, 64-bit ARM, and IBM Power Systems.
pmdabpftrace
Moved example autostart scripts to the /usr/share directory.
pmdadenki
Added support for multiple active batteries.
pmdalinux
Updates for the latest /proc/net/netstat changes.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
54

pmdaopenvswitch
Added additional interface and coverage statistics.
pmproxy
Request parameters can now be sent in the request body.
pmieconf
Added several pmie rules for Open vSwitch metrics.
pmlogger_farm
Added a default configuration file for farm loggers.
pmlogger_daily_report
Some major efficiency improvements.
The sadf(1) tool now generates PCP archives from native sadc(1) archives
Starting in RHEL 9, the sadf(1) tool provided by the sysstat package can generate PCP archives from
native sadc(1) archives.
By default, when the - flag is used with sadc(1), sadc(1) writes the data to the standard system activity
daily data file. This file is named saDD and is located in the /var/log/sa directory by default. Conversely,
when no input datafile is specified, the sadf(1) tool uses the standard system activity daily data file to
generate archives. Pass numbers as an argument to tell sadf(1) to generate archives from data recorded
that specified number of days in the past.
To generate a PCP archive from an sadc(1) archive recorded 2 days ago, run:
# sadf -l -O pcparchive=/tmp/recording -2
To show a list of metrics in the PCP archive generated from an sadc(1) archive archive, run:
$ pminfo --archive /tmp/recording
Disk.dev.avactive
Disk.dev.read
Disk.dev.write
Disk.dev.blkread
[...]
To show the timespace of the archive and hostname of the PCP archive generated from an
sadc(1) archive
$ pmdumplog --label /tmp/recording
Log Label (Log Format Version 2)
Performance metrics from host shard
commencing Tue Jul 20 00:10:30.642477 2021
ending Wed Jul 21 00:10:30.222176 2021
You can then analyze the PCP archive generated from an sadc(1) archive by using PCP
commands, for example:
$ pmchart --archive /tmp/recording
New PCP PMDA - pmdabpf
RHEL 9 is distributed with the pcp-pmda-bpf package, which provides the pmdabpf Performance Co-
CHAPTER 19. PERFORMANCE
55

RHEL 9 is distributed with the pcp-pmda-bpf package, which provides the pmdabpf Performance Co-
Pilot (PCP) Performance Metric Domain Agent (PMDA).
The pmdabpf PMDA extracts live performance data from eBPF programs utilizing BPF CO-RE
(Compile Once - Run Everywhere), that is libbpf and BTF.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
56

CHAPTER 20. SECURITY
The following chapters contain the most notable changes to security between RHEL 8 and RHEL 9.
20.1. SECURITY COMPLIANCE
CIS and DISA STIG profiles provided as DRAFT
The profiles based on benchmarks from the Center for Internet Security (CIS) and Defence Industry
Security Association Security Technical Implementation Guides (DISA STIG) are provided as DRAFT
because the issuing authorities have not yet published an official benchmark for RHEL 9. In addition, the
OSSP profile is in DRAFT because it is being implemented.
For a complete list of profiles available in RHEL 9, see SCAP Security Guide profiles supported in RHEL
9.
OpenSCAP no longer supports SHA-1 and MD5
Due to removal of SHA-1 and MD5 hash functions in Red Hat Enterprise Linux 9, support for OVAL
filehash_test has been removed from OpenSCAP. Also, support for SHA-1 and MD5 hash functions has
been removed from OVAL filehash58_test implementation in OpenSCAP. As a result, OpenSCAP
evaluates rules in SCAP content that use the OVAL filehash_test as notchecked. In addition,
OpenSCAP returns notchecked also when evaluating OVAL filehash58_test with the hash_type
element within filehash58_object set to SHA-1 or MD5.
To update your OVAL content, rewrite the affected SCAP content so that it uses filehash58_test
instead of filehash_test and use one of SHA-224, SHA-256, SHA-384, SHA-512 in the hash_type
element within filehash58_object.
OpenSCAP uses the data stream file instead of the XCCDF file
The SCAP source data stream file (ssg-rhel9-ds.xml) contains all the data that in previous versions of
RHEL were contained in the XCCDF file (ssg-rhel9-xccdf.xml). The SCAP source data stream is a
container file that includes all the components (XCCDF, OVAL, CPE) needed to perform a compliance
scan. Using the SCAP source data stream instead of XCCDF has been recommended since RHEL 7. In
previous versions of RHEL, the data in the XCCDF file and SCAP source data stream was duplicated. In
RHEL 9, this duplication is removed to reduce the RPM package size. If your scenario requires using
separate files instead of the data stream, you can split the data stream file by using this command: #
oscap ds sds-split /usr/share/xml/scap/ssg/content/ssg-rhel9-ds.xml output_directory.
20.2. CRYPTO-POLICIES, RHEL CORE CRYPTOGRAPHIC
COMPONENTS, AND PROTOCOLS
Continuing SHA-1 deprecation
In RHEL 9, SHA-1 usage for signatures is restricted in the DEFAULT system-wide cryptographic policy.
Except for HMAC, SHA-1 is no longer allowed in TLS, DTLS, SSH, IKEv2, DNSSEC, and Kerberos
protocols. Individual applications not controlled by the RHEL system-wide crypto policies are also
moving away from using SHA-1 hashes in RHEL 9.
If your scenario requires the use of SHA-1 for verifying existing or third-party cryptographic signatures,
you can enable it by entering the following command:
# update-crypto-policies --set DEFAULT:SHA1
Alternatively, you can switch the system-wide crypto policies to the LEGACY policy. Note that LEGACY
CHAPTER 20. SECURITY
57

Alternatively, you can switch the system-wide crypto policies to the LEGACY policy. Note that LEGACY
also enables many other algorithms that are not secure. See the Re-enabling SHA-1 section in the RHEL
9 Security hardening document for more information.
For solutions of compatibility problems with systems that still require SHA-1, see the following KCS
articles:
SSH from RHEL 9 to RHEL 6 systems does not work
Packages signed with SHA-1 cannot be installed or upgraded
Failed connection with SSH servers and clients that do not support the 'server-sig-algs'
extension
DNSSEC records signed with RSASHA1 fail to verify
Algorithms disabled in all policy levels
The following algorithms are disabled in the LEGACY, DEFAULT and FUTURE crypto policies provided
with RHEL 9:
TLS older than version 1.2 (since RHEL 9, was < 1.0 in RHEL 8)
DTLS older than version 1.2 (since RHEL 9, was < 1.0 in RHEL 8)
DH with parameters < 2048 bits (since RHEL 9, was < 1024 bits in RHEL 8)
RSA with key size < 2048 bits (since RHEL 9, was < 1024 bits in RHEL 8)
DSA (since RHEL 9, was < 1024 bits in RHEL 8)
3DES (since RHEL 9)
RC4 (since RHEL 9)
FFDHE-1024 (since RHEL 9)
DHE-DSS (since RHEL 9)
Camellia (since RHEL 9)
ARIA
SEED
IDEA
Integrity-only cipher suites
TLS CBC mode cipher suites using SHA-384 HMAC
AES-CCM8
All ECC curves incompatible with TLS 1.3, including secp256k1
IKEv1 (since RHEL 8)
NSEC3DSA in the BIND configuration (since RHEL 9.2)
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
58
WARNING
If your scenario requires a policy that has been disabled, you can enable it by
applying a custom cryptographic policy or by an explicit configuration of individual
applications, but the resulting configuration will not be supported.
Changes to TLS
In RHEL 9, TLS configuration is performed using the system-wide cryptographic policies mechanism.
TLS versions below 1.2 are not supported anymore. DEFAULT, FUTURE and LEGACY cryptographic
policies allow only TLS 1.2 and 1.3. See Using system-wide cryptographic policies for more information.
The default settings provided by libraries included in RHEL 9 are secure enough for most deployments.
The TLS implementations use secure algorithms where possible while not preventing connections from
or to legacy clients or servers. Apply hardened settings in environments with strict security requirements
where legacy clients or servers that do not support secure algorithms or protocols are not expected or
allowed to connect.
The Extended Master Secret TLS Extension is now enforced on FIPS-enabled systems
With the release of the RHSA-2023:3722 advisory, the TLS Extended Master Secret (EMS) extension
(RFC 7627) is mandatory for TLS 1.2 connections on FIPS-enabled RHEL 9 systems. This is in
accordance with FIPS-140-3 requirements. TLS 1.3 is not affected.
Legacy clients that do not support EMS or TLS 1.3 now cannot connect to FIPS servers running on
RHEL 9. Similarly, RHEL 9 clients in FIPS mode cannot connect to servers that only support TLS 1.2
without EMS. This in practice means that these clients cannot connect to servers on RHEL 6, RHEL 7
and non-RHEL legacy operating systems. This is because the legacy 1.0.x versions of OpenSSL do not
support EMS or TLS 1.3.
SCP not supported in RHEL 9
The secure copy protocol (SCP) protocol is no longer supported because it is difficult to secure. It has
already caused security issues, for example CVE-2020-15778. In RHEL 9, SCP is replaced by the SSH
File Transfer Protocol (SFTP) by default.
WARNING
By default, SSH cannot connect from RHEL 9 systems to older systems (for
example, RHEL 6) or from older systems to RHEL 9. This is because the
cryptographic algorithms used in older versions are now considered insecure. If your
scenario requires connecting with older systems, you can either use the ECDSA and
ECDH algorithms as keys on the legacy system or use the legacy cryptographic
policy on the RHEL 9 system. For additional details, see the solutions SSH from
RHEL 9 to RHEL 6 systems does not work and Failed connection with SSH servers
and clients that do not support the server-sig-algs extension.
CHAPTER 20. SECURITY
59

Interoperability of FIPS:OSPP hosts impacted due to CNSA 1.0
The OSPP subpolicy has been aligned with Commercial National Security Algorithm (CNSA) 1.0. This
affects the interoperability of hosts that use the FIPS:OSPP policy-subpolicy combination, with the
following major aspects:
Minimum RSA key size is mandated at 3072 bits.
Algorithm negotiations no longer support AES-128 ciphers, the secp256r1 elliptic curve, and the
FFDHE-2048 group.
OpenSSH root password login disabled by default
The default configuration of OpenSSH in RHEL 9 disallows users to log in as root with a password to
prevent attackers from gaining access through brute-force attacks on passwords.
OpenSSH further enforces SHA-2
As part of the effort to migrate further from the less secure SHA-1 message digest for cryptographic
purposes, the following changes were made in OpenSSH:
Added a check on sshd startup whether using SHA-1 is configured on the system. If it is not
available, OpenSSH does not try to use SHA-1 for operations. This eliminates loading DSS keys
when they are present and also enforces advertising rsa-sha2 combinations when they are
available.
On SSH private key conversion, OpenSSH explicitly uses SHA-2 for testing RSA keys.
When SHA-1 signatures are unavailable on the server side, sshd uses SHA-2 to confirm host key
proof. This might be incompatible with clients on RHEL 8 and earlier versions.
When the SHA-1 algorithm is unavailable on the client side, OpenSSH uses SHA-2.
On the client side, OpenSSH permits SHA-2-based key proofs from the server when SHA-1 was
used in key proof request or when the hash algorithm is not specified (assuming default). This is
aligned with the already present exception for RSA certificates, and allows connecting by using
modern algorithms when supported.
GnuTLS requires EMS with TLS 1.2 in FIPS mode
To comply with the FIPS-140-3 standard, GnuTLS servers and clients require the Extended Master
Secret (EMS) extension (RFC 7627) for all TLS 1.2 connections negotiated in FIPS mode. If your
scenario requires preserving compatibility with older servers and clients that do not support EMS and
you cannot use TLS 1.3, you can apply the NO-ENFORCE-EMS system-wide cryptographic subpolicy:
# update-crypto-policies --set FIPS:NO-ENFORCE-EMS
WARNING
If you allow TLS 1.2 connections without EMS, your system no longer meets the
FIPS-140-3 requirements.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
60

GnuTLS no longer supports TPM 1.2
The GnuTLS library no longer supports the Trusted Platform Module (TPM) 1.2 technology. Your
applications using TPM through the GnuTLS API must support TPM 2.0.
GnuTLS support for GOST has been removed
In RHEL 8, the GOST ciphers have been disabled through the system-wide cryptographic policies. In
RHEL 9, support for these ciphers has been removed from the GnuTLS library.
cyrus-sasl now uses GDBM instead of Berkeley DB
The cyrus-sasl package is now built without the libdb dependency, and the sasldb plugin uses the
GDBM database format instead of Berkeley DB. To migrate your existing Simple Authentication and
Security Layer (SASL) databases stored in the old Berkeley DB format, use the cyrusbdb2current tool
with the following syntax:
$ cyrusbdb2current <sasldb_path> <new_path>
NSS now enforce EMS in FIPS mode
The Network Security Services (NSS) libraries now contain the TLS-REQUIRE-EMS policy to require
the Extended Master Secret (EMS) extension (RFC 7627) for all TLS 1.2 connections as mandated by
the FIPS 140-3 standard. NSS use the new policy when the system-wide cryptographic policies are set to
FIPS.
If your scenario requires interoperating with legacy systems without support for EMS or TLS 1.3, you can
apply the NO-ENFORCE-EMS system-wide cryptographic subpolicy. Such a change violates the FIPS-
140-3 requirements.
NSS no longer support DBM and pk12util defaults changed
The Network Security Services (NSS) libraries no longer support the DBM file format for the trust
database. In RHEL 8, the SQLite file format became the default format, and the existing DBM
databases were opened on read-only mode and automatically converted to SQLite. Before you upgrade
to RHEL 9, update all trust databases from DBM to SQLite.
See the Updating NSS databases from DBM to SQLite procedure for detailed instructions.
NSS pk12util no longer uses DES-3 and SHA-1 by default
The pk12util tool now uses the AES and SHA-256 algorithms instead of DES-3 and SHA-1 by default
when exporting private keys.
Note that SHA-1 is disabled by the default system-wide cryptographic policy for all signatures in RHEL
9.
NSS no longer support RSA keys shorter than 1023 bits
The update of the Network Security Services (NSS) libraries changes the minimum key size for all RSA
operations from 128 to 1023 bits. This means that NSS no longer perform the following functions:
Generate RSA keys shorter than 1023 bits.
Sign or verify RSA signatures with RSA keys shorter than 1023 bits.
Encrypt or decrypt values with RSA key shorter than 1023 bits.
OpenSSL ENGINE extension API is not supported in FIPS mode
CHAPTER 20. SECURITY
61

The legacy extension system to OpenSSL, the ENGINE API, is not compatible with the new provider API.
Therefore, applications that depend on functionality provided by OpenSSL engines, such as the
openssl-pkcs11 and openssl-ibmca modules, cannot be used in FIPS mode.
FIPS mode in OpenSSL must be enabled to work correctly
If you are using non-default values in the openssl.cnf configuration file with FIPS mode enabled, and
especially when using a third-party FIPS provider, add fips=yes to the openssl.cnf file.
OpenSSL does not accept explicit curve parameters in FIPS mode
Elliptic curve cryptography parameters, private keys, public keys, and certificates that specified explicit
curve parameters no longer work in FIPS mode. Specifying the curve parameters using ASN.1 object
identifiers, which use one of the FIPS-approved curves, still works in FIPS mode.
Libreswan now requests ESN by default
In Libreswan, the default value for the configuration option esn= has changed from no to either. This
means that when initiating connections, Libreswan requests the use of Extended Serial Number (ESN)
by default. In particular, when hardware offload is used, this new behavior prevents certain network
interface cards (NIC) from establishing IPsec connection if they do not support ESN. To disable ESN, set
esn= to no and the replay_window= option to a value of 32 or lower. For example:
esn=no
replay_window=32
The replay_window= option is necessary because a different mechanism uses ESN for anti-replay
protection with window sizes larger than 32.
20.3. SELINUX
Support for disabling SELinux through /etc/selinux/config has been removed
With the RHEL 9.0 release, support for disabling SELinux through the SELINUX=disabled option in the
/etc/selinux/config file has been removed from the kernel. When you disable SELinux only through
/etc/selinux/config, the system starts with SELinux enabled but with no policy loaded, and SELinux
security hooks remain registered in the kernel. This means that SELinux disabled by using
/etc/selinux/config still requires some system resources, and you should instead disable SELinux by
using the kernel command line in all performance-sensitive scenarios.
Furthermore, the Anaconda installation program and the corresponding man pages have been updated
to reflect this change. This change also enables read-only-after-initialization protection for the Linux
Security Module (LSM) hooks.
If your scenario requires disabling SELinux, add the selinux=0 parameter to your kernel command line.
See the Remove support for SELinux run-time disable Fedora wiki page for more information.
Additional services confined in the SELinux policy
The RHEL 9.3 release added additional rules to the SELinux policy that confine the following systemd
services:
qat
systemd-pstore
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
62

boothd
fdo-manufacturing-server
fdo-rendezvous-server
fdo-client-linuxapp
fdo-owner-onboarding-server
As a result, these services do not run with the unconfined_service_t SELinux label anymore, and run
successfully in SELinux enforcing mode.
The glusterd SELinux module moved to a separate glusterfs-selinux package
With this update, the glusterd SELinux module is maintained in the separate glusterfs-selinux
package. The module is therefore no longer part of the selinux-policy package. For any actions that
concern the glusterd module, install and use the glusterfs-selinux package.
CHAPTER 20. SECURITY
63

CHAPTER 21. SHELLS AND COMMAND-LINE TOOLS
The following chapters contain the most notable changes to shells and command-line tools between
RHEL 8 and RHEL 9.
21.1. NOTABLE CHANGES TO SYSTEM MANAGEMENT
Data Encryption Standard (DES) algorithm is not available for net-snmp communication in
Red Hat Enterprise Linux 9
In previous versions of RHEL, DES was used as an encryption algorithm for secure communication
between net-snmp clients and servers. In RHEL 9, the DES algorithm isn’t supported by the OpenSSL
library. The algorithm is marked as insecure and the DES support for net-snmp has therefore been
removed.
The ABRT tool has been removed
The Automatic Bug Reporting Tool (ABRT) for detecting and reporting application crashes is not
available in RHEL 9.
As a replacement, use the systemd-coredump tool to log and store core dumps, which are
automatically generated files after a program crashes.
The hidepid=n mount option is not supported in RHEL 9 systemd
The mount option hidepid=n, which controls who can access information in /proc/[pid] directories, is not
compatible with systemd infrastructure provided in RHEL 9.
In addition, using this option might cause certain services started by systemd to produce SELinux AVC
denial messages and prevent other operations from being completed.
The dump utility from the dump package has been removed
The dump utility used for backup of file systems has been deprecated in Red Hat Enterprise Linux 8 and
is not available in RHEL 9.
In RHEL 9, Red Hat recommends using the tar, or dd as a backup tool for ext2, ext3, and ext4 file
systems. The dump utility will be a part of the EPEL 9 repository.
Note that the restore utility from the dump package remains available and supported in RHEL 9 and is
available as the restore package.
RHEL 9 does not contain ReaR crontab
The /etc/cron.d/rear crontab in the rear package, which runs rear mkrescue after the disk layout
changes, has been removed in RHEL 9.
If you relied on the /etc/cron.d/rear crontab to run rear mkrescue, you can manually configure periodic
runs of ReaR instead.
NOTE
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
64

NOTE
The rear package in RHEL contains the following examples for scheduling jobs:
the /usr/share/doc/rear/rear.cron example crontab
the /usr/share/doc/rear/rear.{service,timer} example systemd unit
Do not use these examples without site-specific modifications or other actions to take
updated backups for system recovery. You must take regular backups in addition to re-
creating the rescue image. The steps to take a backup depend on the local configuration.
If you run the rear mkrescue command without taking an updated backup at the same
time, the system recovery process would use a previous backup that might be
inconsistent with the saved layout.
21.2. NOTABLE CHANGES TO COMMAND-LINE TOOLS
Support for the raw command-line tool has been removed
With this release, the raw (/usr/bin/raw) command-line tool has been removed from the util-linux
package, because Linux kernel does not support raw devices since version 5.14.
Currently, there is no replacement available.
cgroupsv1 is deprecated in RHEL 9
cgroups is a kernel subsystem used for process tracking, system resource allocation and partitioning.
Systemd service manager supports booting in the cgroups v1 mode and in cgroups v2 mode. In Red
Hat Enterprise Linux 9, the default mode is v2. In the next major release, systemd will not support
booting in the cgroups v1 mode and only cgroups v2 mode will be available.
The lsb-release binary is not available in RHEL 9
The information in the /etc/os-release file was previously available by calling the lsb-release binary. This
binary was included in the redhat-lsb package, which was removed in RHEL 9. Now, you can display
information about the operating system, such as the distribution, version, code name, and associated
metadata, by reading the /etc/os-release file. This file is provided by Red Hat and any changes to it are
overwritten with each update of the redhat-release package. The format of the file is KEY=VALUE, and
you can safely source the data for a shell script.
CHAPTER 21. SHELLS AND COMMAND-LINE TOOLS
65

CHAPTER 22. SOFTWARE MANAGEMENT
The following chapter contains the most notable changes to software management between RHEL 8
and RHEL 9.
22.1. NOTABLE CHANGES TO SOFTWARE MANAGEMENT
Package management with DNF/YUM
In Red Hat Enterprise Linux 9, software installation is ensured by DNF. Red Hat continues to support the
usage of the yum term for consistency with previous major versions of RHEL. If you type dnf instead of
yum, the command works as expected because both are aliases for compatibility.
Although RHEL 8 and RHEL 9 are based on DNF, they are compatible with YUM used in RHEL 7.
For more information, see Managing software with the DNF tool.
Notable RPM features and changes
Red Hat Enterprise Linux 9 is distributed with RPM version 4.16. This version introduces many
enhancements over its previous versions.
Notable features include:
New SPEC features, most notably:
Fast macro-based dependency generators
It is now possible to define dependency generators as regular RPM macros. This is especially
useful in combination with the embedded Lua interpreter (%{lua:…}) because it enables
writing sophisticated yet fast generators and avoiding redundant forking and executing a
shell script.
Example:
%__foo_provides() %{basename:%{1}}
The %generate_buildrequires section that enables generating dynamic build
dependencies
Additional build dependencies can now be generated programmatically at RPM build time,
using the newly available %generate_buildrequires section. This is useful when packaging
software written in a language in which a specialized utility is commonly used to determine
run-time or build-time dependencies, such as Rust, Golang, Node.js, Ruby, Python or
Haskell.
Meta (unordered) dependencies
A new dependency qualifier called meta enables expressing dependencies that are not
specifically install-time or run-time dependencies. This is useful for avoiding unnecessary
dependency loops that could otherwise arise from the normal dependency ordering, such as
when specifying the dependencies of a meta package.
Example:
Requires(meta): <pkgname>
Native version comparison in expressions
It is now possible to compare arbitrary version strings in expressions by using the newly
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
66

It is now possible to compare arbitrary version strings in expressions by using the newly
supported v"…" format.
Example:
%if v"%{python_version}" < v"3.9"
Caret version operator, opposite of tilde
The new caret (^) operator can be used to express a version that is higher than the base
version. It is a complement to the existing tilde (~) operator which has the opposite
semantics.
%elif, %elifos and %elifarch statements
Optional automatic patch and source numbering
Patch: and Source: tags without a number are now automatically numbered based on the
order in which they are listed.
%autopatch now accepts patch ranges
The %autopatch macro now accepts the -m and -M parameters to limit the minimum and
maximum patch number to apply, respectively.
%patchlist and %sourcelist sections
It is now possible to list patch and source files without preceding each item with the
respective Patch: and Source: tags by using the newly added %patchlist and %sourcelist
sections.
A more intuitive way to declare build conditionals
Starting from RHEL 9.2, you can use the new %bcond macro to build conditionals. The
%bcond macro takes a build conditional name and the default value as arguments.
Compared to the old %bcond_with and %bcond_without macros, %bcond is easier to
understand and allows you to calculate the default value at build time. The default value can
be any numeric expression.
Example:
To create a gnutls build conditional, enabled by default:
%bcond gnutls 1
To create a bootstrap build conditional, disabled by default:
%bcond bootstrap 0
To create an openssl build conditional, defaulting to opposite of gnutls:
%bcond openssl %{without gnutls}
The RPM database is now based on the sqlite library. Read-only support for BerkeleyDB
databases has been retained for migration and query purposes.
A new rpm-plugin-audit plug-in for issuing audit log events on transactions, previously built into
RPM itself
Increased parallelism in package builds
CHAPTER 22. SOFTWARE MANAGEMENT
67

There have been numerous improvements to the way the package build process is parallelized.
These improvements involve various buildroot policy scripts and sanity checks, file classification,
and subpackage creation and ordering. As a result, package builds on multiprocessor systems,
particularly for large packages, should now be faster and more efficient.
Enforced UTF-8 validation of header data at build-time
RPM now supports the Zstandard (zstd) compression algorithm
In RHEL 9, the default RPM compression algorithm has switched to Zstandard (zstd). As a
result, packages now install faster, which can be especially noticeable during large transactions.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
68

CHAPTER 23. SUBSCRIPTION MANAGEMENT
The following chapter contains the most notable changes to subscription management between RHEL 8
and RHEL 9.
23.1. NOTABLE CHANGES TO SUBSCRIPTION MANAGEMENT
Merged system purpose commands under the subscription-manager syspurpose command
Previously, there were two different commands to set system purpose attributes; syspurpose and
subscription-manager. To unify all the system purpose attributes under one module, all the addons,
role, service-level, and usage commands from subscription-manager have been moved to the new
submodule, subscription-manager syspurpose.
Existing subscription-manager commands outside the new submodule are deprecated. The separate
package (python3-syspurpose) that provides the syspurpose command line tool has been removed in
RHEL 9.
This update provides a consistent way to view, set, and update all system purpose attributes using a
single command of subscription-manager. This command replaces all the existing system purpose
commands with their equivalent versions available as a new subcommand. For example, subscription-
manager role --set SystemRole becomes subscription-manager syspurpose role --set SystemRole
and so on.
For complete information about the new commands, options, and other attributes, see the
SYSPURPOSE OPTIONS section in the subscription-manager man page or Configuring system
purpose using the subscription manager command line tool.
virt-who now uses /etc/virt-who.conf for global options instead of /etc/sysconfig/virt-who
In RHEL 9, the global options for the virt-who utility on your system are stored in the /etc/virt-who.conf
file. Therefore, the /etc/sysconfig/virt-who file is not being used any more, and has been removed.
CHAPTER 23. SUBSCRIPTION MANAGEMENT
69

CHAPTER 24. SYSTEM ROLES
The following chapter contains the most notable changes to system roles between RHEL 8 and RHEL 9.
24.1. PERFORMING SYSTEM ADMINISTRATION TASKS WITH RHEL
SYSTEM ROLES
As of Red Hat Enterprise Linux 9.0 General Availability (GA) release, RHEL system roles includes the
ansible-core 2.12 package. This is a version of Ansible that has only the core functionality - that is, it
does not include modules such as blivet for the storage role, gobject for the network role, and plugins
such as json_query.
With RHEL system roles, you can take advantage of a configuration interface to remotely manage
multiple RHEL systems. As an option to the traditional RHEL system roles format, you can benefit from
Ansible Collections, available in the Automation Hub only for Ansible Automation Platform Customers
or via RPM package, available for RHEL users.
RHEL system roles support
Support for the following roles are available:
The cockpit RHEL system role. You can automate the deployment and configuration of the web
console and, thus, be able to manage your RHEL systems from a web browser.
The firewall RHEL system role.
The ha_cluster RHEL system role, formerly presented as a Technology Preview, is now fully
supported.
The nbde_client RHEL system role now supports servers with static IP addresses.
The Microsoft SQL (microsoft.sql.server) role for Microsoft SQL Server. It simplifies and
automates the configuration of RHEL with recommended settings for MSSQL Server
workloads. Currently, the SQL Server does not support running on RHEL 9. You can only run the
role on a RHEL 9 control node to manage the SQL Server on RHEL 7 and RHEL 8.
The VPN RHEL system role, to configure VPN connections on RHEL systems by using Red Hat
Ansible Automation Platform. Users can use it to set up host-to-host, network-to-network, VPN
Remote Access Server, and Mesh configurations.
The IPMI modules, to automate hardware management interfaces available in the rhel_mgmt
Collection.
To learn more about the RHEL system roles, see the documentation title Administration and
configuration tasks using system roles in RHEL.
Support for Ansible Engine 2.9 is no longer available in RHEL 9
Ansible Engine 2.9 is no longer available in Red Hat Enterprise Linux 9. Playbooks that previously ran
on Ansible Engine 2.9 might generate error messages related to missing plugins or modules. If your use
case for Ansible falls outside of the limited scope of support for Ansible Core provided in RHEL, contact
Red Hat to discuss the available offerings.
RHEL system roles now uses Ansible Core
As of the RHEL 9 General Availability release, Ansible Core is provided with a limited scope of support
to enable RHEL supported automation use cases. Ansible Core is available in the AppStream
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
70

repository for RHEL. For details on the scope of support, refer to Scope of support for the Ansible Core
package included in the RHEL 9 AppStream.
NOTE
As of Red Hat Enterprise Linux 9.0, the scope of support for Ansible Core in the RHEL
AppStream is limited to any Ansible playbooks, roles, and modules that are included with
or generated by a Red Hat product, such as RHEL system roles.
The deprecated --token option of the subscription-manager register command will stop
working at the end of November 2024
The default entitlement server, subscription.rhsm.redhat.com, will no longer be allowing token-based
authentication from the end of November 2024. As a result, the deprecated --token=<TOKEN> option
of the subscription-manager register command will no longer be a supported authentication method.
As a consequence, if you use subscription-manager register --token=<TOKEN>, the registration will
fail with the following error message:
Token authentication not supported by the entitlement server
To register your system, use other supported authorization methods, such as including paired options --
username / --password OR --org / --activationkey with the subscription-manager register
command.
RHEL system roles can be used to manage multiple different versions of RHEL
You can use RHEL system roles as a consistent interface to manage different versions of RHEL. This
can help to ease the transition between major versions of RHEL.
CHAPTER 24. SYSTEM ROLES
71

CHAPTER 25. VIRTUALIZATION
The following chapters contain the most notable changes to virtualization between RHEL 8 and RHEL 9.
25.1. NOTABLE CHANGES TO KVM
KVM virtualization is no longer supported on IBM POWER
Red Hat Kernel-based Virtual Machine (KVM) for RHEL 9.0 and later is not supported on IBM POWER
hardware.
KVM virtualization fully supported on 64-bit ARM architecture
In RHEL 9.4 and later, creating KVM virtual machines on systems that use 64-bit ARM (also known as
AArch64) CPUs is fully supported. Note, however, that certain virtualization features and functionalities
that are available on AMD64 and Intel 64 systems might work differently or be unsupported on 64-bit
ARM systems.
For details, see How virtualization on ARM 64 differs from AMD 64 and Intel 64 .
VM machine types based on RHEL 7.5 and earlier are unsupported
In RHEL 9, virtual machines (VMs) no longer support machine types based on RHEL 7.5 and earlier.
These also include pc-i440fx-rhel7.5.0 and earlier machine types, which were default in earlier major
versions of RHEL. As a consequence, attempting to start a VM with such machine types on a RHEL 9
host fails with an unsupported configuration error. If you encounter this problem after upgrading your
host to RHEL 9, see the Red Hat KnowledgeBase .
RHEL 9 still supports the pc-i440fx-rhel7.6.0 machine type. However, RHEL will remove support for all
i440x machine types in a future major update.
25.2. NOTABLE CHANGES TO LIBVIRT
Modular libvirt daemons
In RHEL 9, the libvirt library uses modular daemons that handle individual virtualization driver sets on
your host. For example, the virtqemud daemon handles QEMU drivers. This makes it possible to fine-
grain a variety of tasks that involve virtualization drivers, such as resource load optimization and
monitoring.
In addition, the monolithic libvirt daemon, libvirtd, has become deprecated. However, if you upgrade
from RHEL 8 to RHEL 9, your host will still use libvirtd, which you can continue using in RHEL 9.
Nevertheless, Red Hat recommends enabling modular libvirt daemons instead. For instructions, see the
Enabling modular libvirt daemons document.
Note, however, that if you switch to using modular libvirt daemons, pre-configured tasks that use
libvirtd will stop working.
External snapshots for virtual machines
RHEL 9.4 and later supports the external snapshot mechanism for virtual machines (VMs), which
replaces the previously deprecated internal snapshot mechanism. As a result, you can create, delete, and
revert to VM snapshots that are fully supported. External snapshots work more reliably both in the
command-line interface and in the RHEL web console. This also applies to snapshots of running VMs,
known as live snapshots.
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
72

Note, however, that some commands and utilities might still create internal snapshots. To verify that
your snapshot is fully supported, ensure that it is configured as external. For example:
# virsh snapshot-dumpxml VM-name snapshot-name | grep external
<disk name='vda' snapshot='external' type='file'>
virsh iface-* commands are now unsupported
The virsh iface-* commands, such as virsh iface-start and virsh iface-destroy, are no longer
supported in RHEL 9. Due to the removal of the netcf package, the majority of them do not work. To
create and modify network interfaces, use NetworkManager utilities, such as nmcli.
25.3. NOTABLE CHANGES TO QEMU
QEMU no longer includes the SGA option ROM
In RHEL 9, the Serial Graphics Adapter (SGA) option ROM has been replaced by an equivalent
functionality in SeaBIOS. However, if your virtual machine (VM) configuration uses the following XML
fragament, this change will not affect your VM functionality.
<bios useserial='yes'/>
TPM passthrough has been removed
It is no longer possible to assign a physical Trusted Platform Module (TPM) device using the
passthrough back end to a VM on RHEL 9. Note that this was an unsupported feature in RHEL 8.
Instead, use the vTPM functionality, which uses the emulator back end, and is fully supported.
Other unsupported devices
QEMU no longer supports the following virtual devices:
The Cirrus graphics device. The default graphics devices are now set to stdvga on BIOS-based
machines and bochs-display on UEFI-based machines.
The ac97 audio device. In RHEL 9, libvirt uses the ich9 device instead.
Intel vGPU removed
The packages required for the Intel vGPU feature were removed in RHEL 9.3.
Previously, as a Technology Preview, it was possible to divide a physical Intel GPU device into multiple
virtual devices referred to as mediated devices. These mediated devices could then be assigned to
multiple virtual machines (VMs) as virtual GPUs.
Since RHEL 9.3, you cannot use this feature.
25.4. NOTABLE CHANGES TO SPICE
SPICE has become unsupported
In RHEL 9, the SPICE remote display protocol is no longer supported. QXL, the graphics device used by
SPICE, has also become unsupported. On a RHEL 9 host, VMs configured to use SPICE or QXL fail to
start and instead display an unsupported configuration error.
Instead of SPICE, Red Hat recommends using alternate solutions for remote display streaming:
CHAPTER 25. VIRTUALIZATION
73

For remote console access, use the VNC protocol. However, note that certain features
available on SPICE are currently unsupported or do not work well on VNC. This includes:
Smart card sharing from the host to the VM (It is now supported only by third party remote
visualization solutions.)
Audio playback from the VM to the host
Automated VM screen resizing
USB redirection from the host to the VM
Drag & drop file transfer from the host to the VM
In addition, VNC cannot be used by the GNOME Boxes application. As a consequence,
Boxes is currently not available in RHEL 9.
For advanced remote display functions, use third party tools such as RDP, HP ZCentral Remote
Boost, or Mechdyne TGX.
For graphical VMs hosted on RHEL 9, Red Hat recommends using the virtio-vga and virtio-gpu virtual
graphics cards.
For more information on how to switch a VM from the SPICE protocol to VNC, see the Knowledgebase
article Unable to define, create or start a Virtual Machine using spice or qxl in RHEL 9 KVM .
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
74

CHAPTER 26. THE WEB CONSOLE
The following chapter contains the most notable changes to the web console between RHEL 8 and
RHEL 9.
26.1. CHANGES TO THE RHEL WEB CONSOLE
Remote root login disabled on new installations of RHEL 9.2 and later
Due to security reasons, on new installations of RHEL 9.2 and newer, it is not possible to connect to the
web console from a remote machine as a root user.
To enable the remote root login:
1. As a root user, open the /etc/cockpit/disallowed-users file in a text editor.
2. Remove the root user line from the file.
3. Save your changes.
CHAPTER 26. THE WEB CONSOLE
75

APPENDIX A. CHANGES TO PACKAGES
The following chapters contain changes to packages between RHEL 8 and RHEL 9, as well as changes
between minor releases of RHEL 9.
A.1. NEW PACKAGES
The following packages were added in RHEL 9:
Package Repository New in
389-ds-base-devel rhel9-CRB RHEL 9.3
a52dec rhel9-AppStream RHEL 9.0
adobe-source-code-pro-fonts rhel9-AppStream RHEL 9.1
afterburn rhel9-AppStream RHEL 9.0
afterburn-dracut rhel9-AppStream RHEL 9.0
alsa-plugins-pulseaudio rhel9-AppStream RHEL 9.1
alternatives rhel9-BaseOS RHEL 9.0
anaconda-install-img-deps rhel9-AppStream RHEL 9.0
anaconda-widgets-devel rhel9-CRB RHEL 9.1
ant-junit5 rhel9-AppStream RHEL 9.0
anthy-unicode rhel9-AppStream RHEL 9.0
anthy-unicode-devel rhel9-CRB RHEL 9.1
appstream rhel9-AppStream RHEL 9.0
appstream-compose rhel9-CRB RHEL 9.0
appstream-compose-devel rhel9-CRB RHEL 9.0
appstream-devel rhel9-CRB RHEL 9.0
appstream-qt rhel9-CRB RHEL 9.0
appstream-qt-devel rhel9-CRB RHEL 9.0
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
76

aspnetcore-runtime-7.0 rhel9-AppStream RHEL 9.1
aspnetcore-runtime-8.0 rhel9-AppStream RHEL 9.4
aspnetcore-targeting-pack-7.0 rhel9-AppStream RHEL 9.1
aspnetcore-targeting-pack-8.0 rhel9-AppStream RHEL 9.4
autoconf-latest rhel9-AppStream RHEL 9.4
autoconf271 rhel9-AppStream RHEL 9.4
autocorr-dsb rhel9-AppStream RHEL 9.0
autocorr-el rhel9-AppStream RHEL 9.0
autocorr-hsb rhel9-AppStream RHEL 9.0
autocorr-vro rhel9-AppStream RHEL 9.0
avahi-glib-devel rhel9-CRB RHEL 9.3
avahi-tools rhel9-AppStream RHEL 9.3
babel-doc rhel9-CRB RHEL 9.0
bind-dnssec-doc rhel9-AppStream RHEL 9.0
bind-dnssec-utils rhel9-AppStream RHEL 9.0
bind-doc rhel9-CRB RHEL 9.1
binutils-gold rhel9-BaseOS RHEL 9.0
blas64 rhel9-CRB RHEL 9.3
blas64_ rhel9-CRB RHEL 9.0
bmc-snmp-proxy rhel9-AppStream RHEL 9.0
boost-b2 rhel9-CRB RHEL 9.0
boost-contract rhel9-AppStream RHEL 9.0
boost-doctools rhel9-CRB RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
77

boost-json rhel9-AppStream RHEL 9.0
boost-nowide rhel9-AppStream RHEL 9.0
bootc rhel9-AppStream RHEL 9.4
bootupd rhel9-AppStream RHEL 9.0
Box2D rhel9-AppStream RHEL 9.0
butane rhel9-AppStream RHEL 9.0
byte-buddy rhel9-AppStream RHEL 9.0
byte-buddy-agent rhel9-CRB RHEL 9.0
byteman-bmunit rhel9-AppStream RHEL 9.0
catatonit rhel9-CRB RHEL 9.1
capstone rhel9-AppStream RHEL 9.2
capstone-devel rhel9-CRB RHEL 9.2
capstone-java rhel9-CRB RHEL 9.2
cdrskin rhel9-AppStream RHEL 9.0
cepces rhel9-AppStream RHEL 9.4
cepces-certmonger rhel9-AppStream RHEL 9.4
cepces-selinux rhel9-AppStream RHEL 9.4
cifs-utils-devel rhel9-CRB RHEL 9.2
cldr-emoji-annotation-dtd rhel9-AppStream RHEL 9.0
clevis-pin-tpm2 rhel9-AppStream RHEL 9.0
cockpit-ostree rhel9-AppStream RHEL 9.3
compat-hesiod rhel9-AppStream RHEL 9.0
compat-openssl11 rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
78

compat-paratype-pt-sans-fonts-f33-
f34
rhel9-AppStream RHEL 9.0
compat-sap-c++-12 rhel9-SAP RHEL 9.2
composefs rhel9-AppStream RHEL 9.4
composefs-libs rhel9-AppStream RHEL 9.4
console-login-helper-messages rhel9-AppStream RHEL 9.0
console-login-helper-messages-
issuegen
rhel9-AppStream RHEL 9.0
console-login-helper-messages-
motdgen
rhel9-AppStream RHEL 9.0
console-login-helper-messages-
profile
rhel9-AppStream RHEL 9.0
console-setup rhel9-AppStream RHEL 9.0
container-tools rhel9-AppStream RHEL 9.0
cups-printerapp rhel9-AppStream RHEL 9.0
curl-minimal rhel9-BaseOS RHEL 9.0
cxl-cli rhel9-AppStream RHEL 9.2
cxl-devel rhel9-CRB RHEL 9.2
cxl-libs rhel9-AppStream RHEL 9.2
cyrus-imapd-libs rhel9-AppStream RHEL 9.0
dbus-broker rhel9-BaseOS RHEL 9.0
dbus-python-devel rhel9-CRB RHEL 9.4
ddiskit rhel9-AppStream RHEL 9.0
debugedit rhel9-AppStream RHEL 9.0
dejavu-lgc-sans-mono-fonts rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
79

dejavu-lgc-serif-fonts rhel9-AppStream RHEL 9.0
docbook5-style-xsl rhel9-AppStream RHEL 9.0
docbook5-style-xsl-extensions rhel9-AppStream RHEL 9.0
dotnet-apphost-pack-7.0 rhel9-AppStream RHEL 9.1
dotnet-apphost-pack-8.0 rhel9-AppStream RHEL 9.4
dotnet-hostfxr-7.0 rhel9-AppStream RHEL 9.1
dotnet-hostfxr-8.0 rhel9-AppStream RHEL 9.4
dotnet-runtime-7.0 rhel9-AppStream RHEL 9.1
dotnet-runtime-8.0 rhel9-AppStream RHEL 9.4
dotnet-sdk-7.0 rhel9-AppStream RHEL 9.1
dotnet-sdk-7.0-source-built-artifacts rhel9-CRB RHEL 9.1
dotnet-sdk-8.0 rhel9-AppStream RHEL 9.4
dotnet-sdk-8.0-source-built-artifacts rhel9-CRB RHEL 9.4
dotnet-targeting-pack-7.0 rhel9-AppStream RHEL 9.1
dotnet-targeting-pack-8.0 rhel9-AppStream RHEL 9.4
dotnet-templates-7.0 rhel9-AppStream RHEL 9.1
dotnet-templates-8.0 rhel9-AppStream RHEL 9.4
double-conversion rhel9-AppStream RHEL 9.0
double-conversion-devel rhel9-CRB RHEL 9.1
drgn rhel9-AppStream RHEL 9.4
ecj rhel9-AppStream RHEL 9.2
edk2-tools rhel9-CRB RHEL 9.2
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
80

edk2-tools-doc rhel9-CRB RHEL 9.2
efs-utils rhel9-AppStream RHEL 9.4
efs-utils-selinux rhel9-AppStream RHEL 9.4
egl-utils rhel9-AppStream RHEL 9.1
emacs-auctex rhel9-AppStream RHEL 9.0
emacs-cython-mode rhel9-CRB RHEL 9.0
espeak-ng-devel rhel9-CRB RHEL 9.3
evince-previewer rhel9-AppStream RHEL 9.0
evince-thumbnailer rhel9-AppStream RHEL 9.0
evolution-data-server-ui rhel9-AppStream RHEL 9.4
evolution-data-server-ui-devel rhel9-AppStream RHEL 9.4
exfatprogs rhel9-BaseOS RHEL 9.0
expect-devel rhel9-CRB RHEL 9.4
fapolicyd-dnf-plugin rhel9-AppStream RHEL 9.0
fdk-aac-free rhel9-AppStream RHEL 9.0
fdk-aac-free-devel rhel9-CRB RHEL 9.1
fence-agents-openstack rhel9-HighAvailability RHEL 9.0
festival rhel9-AppStream RHEL 9.0
festival-data rhel9-AppStream RHEL 9.0
festvox-slt-arctic-hts rhel9-AppStream RHEL 9.0
fido2-tools rhel9-AppStream RHEL 9.4
fio-engine-dev-dax rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
81

fio-engine-http rhel9-AppStream RHEL 9.0
fio-engine-libaio rhel9-AppStream RHEL 9.0
fio-engine-libpmem rhel9-AppStream RHEL 9.0
fio-engine-nbd rhel9-AppStream RHEL 9.0
fio-engine-pmemblk rhel9-AppStream RHEL 9.0
fio-engine-rados rhel9-AppStream RHEL 9.0
fio-engine-rbd rhel9-AppStream RHEL 9.0
fio-engine-rdma rhel9-AppStream RHEL 9.0
firefox-x11 rhel9-AppStream RHEL 9.2
flashrom rhel9-AppStream RHEL 9.0
flexiblas rhel9-AppStream RHEL 9.0
flexiblas-devel rhel9-CRB RHEL 9.0
flexiblas-netlib rhel9-AppStream RHEL 9.0
flexiblas-netlib64 rhel9-CRB RHEL 9.0
flexiblas-openblas-openmp rhel9-AppStream RHEL 9.0
flexiblas-openblas-openmp64 rhel9-CRB RHEL 9.0
fonts-filesystem rhel9-BaseOS RHEL 9.0
fonts-rpm-macros rhel9-CRB RHEL 9.0
fonts-srpm-macros rhel9-AppStream RHEL 9.0
freeglut-devel rhel9-AppStream RHEL 9.1
freeradius-mysql rhel9-CRB RHEL 9.2
freeradius-perl rhel9-CRB RHEL 9.2
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
82

freeradius-postgresql rhel9-CRB RHEL 9.2
freeradius-rest rhel9-CRB RHEL 9.2
freeradius-sqlite rhel9-CRB RHEL 9.2
freeradius-unixODBC rhel9-CRB RHEL 9.2
frr-selinux rhel9-AppStream RHEL 9.2
fstrm-utils rhel9-CRB RHEL 9.0
fwupd-plugin-flashrom rhel9-AppStream RHEL 9.0
gawk-all-langpacks rhel9-AppStream RHEL 9.0
gcc-plugin-annobin rhel9-AppStream RHEL 9.0
gcc-toolset-12 rhel9-AppStream RHEL 9.1
gcc-toolset-12-annobin-annocheck rhel9-AppStream RHEL 9.1
gcc-toolset-12-annobin-docs rhel9-AppStream RHEL 9.1
gcc-toolset-12-annobin-plugin-gcc rhel9-AppStream RHEL 9.1
gcc-toolset-12-binutils rhel9-AppStream RHEL 9.1
gcc-toolset-12-binutils-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-binutils-gold rhel9-AppStream RHEL 9.1
gcc-toolset-12-build rhel9-AppStream RHEL 9.1
gcc-toolset-12-dwz rhel9-AppStream RHEL 9.1
gcc-toolset-12-gcc rhel9-AppStream RHEL 9.1
gcc-toolset-12-gcc-c++ rhel9-AppStream RHEL 9.1
gcc-toolset-12-gcc-gfortran rhel9-AppStream RHEL 9.1
gcc-toolset-12-gcc-plugin-annobin rhel9-AppStream RHEL 9.2
gcc-toolset-12-gcc-plugin-devel rhel9-AppStream RHEL 9.1
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
83

gcc-toolset-12-gdb rhel9-AppStream RHEL 9.1
gcc-toolset-12-libasan-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-libatomic-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-libgccjit rhel9-AppStream RHEL 9.1
gcc-toolset-12-libgccjit-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-libgccjit-docs rhel9-AppStream RHEL 9.1
gcc-toolset-12-libitm-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-liblsan-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-libquadmath-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-libstdc++-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-libstdc++-docs rhel9-AppStream RHEL 9.1
gcc-toolset-12-libtsan-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-libubsan-devel rhel9-AppStream RHEL 9.1
gcc-toolset-12-offload-nvptx rhel9-AppStream RHEL 9.1
gcc-toolset-12-runtime rhel9-AppStream RHEL 9.1
gcc-toolset-13 rhel9-AppStream RHEL 9.3
gcc-toolset-13-annobin-annocheck rhel9-AppStream RHEL 9.3
gcc-toolset-13-annobin-docs rhel9-AppStream RHEL 9.3
gcc-toolset-13-annobin-plugin-gcc rhel9-AppStream RHEL 9.3
gcc-toolset-13-binutils rhel9-AppStream RHEL 9.3
gcc-toolset-13-binutils-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-binutils-gold rhel9-AppStream RHEL 9.3
gcc-toolset-13-dwz rhel9-AppStream RHEL 9.3
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
84

gcc-toolset-13-gcc rhel9-AppStream RHEL 9.3
gcc-toolset-13-gcc-c++ rhel9-AppStream RHEL 9.3
gcc-toolset-13-gcc-gfortran rhel9-AppStream RHEL 9.3
gcc-toolset-13-gcc-plugin-annobin rhel9-AppStream RHEL 9.3
gcc-toolset-13-gcc-plugin-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-gdb rhel9-AppStream RHEL 9.3
gcc-toolset-13-libasan-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-libatomic-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-libgccjit rhel9-AppStream RHEL 9.3
gcc-toolset-13-libgccjit-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-libitm-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-liblsan-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-libquadmath-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-libstdc++-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-libstdc++-docs rhel9-AppStream RHEL 9.3
gcc-toolset-13-libtsan-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-libubsan-devel rhel9-AppStream RHEL 9.3
gcc-toolset-13-offload-nvptx rhel9-AppStream RHEL 9.3
gcc-toolset-13-runtime rhel9-AppStream RHEL 9.3
gcr-base rhel9-AppStream RHEL 9.0
gdb-minimal rhel9-AppStream RHEL 9.0
gedit-plugin-sessionsaver rhel9-AppStream RHEL 9.0
gedit-plugin-synctex rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
85

gegl04-devel-docs rhel9-AppStream RHEL 9.0
gegl04-tools rhel9-AppStream RHEL 9.0
glade rhel9-AppStream RHEL 9.0
glibc-doc rhel9-AppStream RHEL 9.0
glibc-langpack-ckb rhel9-BaseOS RHEL 9.0
glibc-langpack-mnw rhel9-BaseOS RHEL 9.0
glslang rhel9-AppStream RHEL 9.0
glslang-devel rhel9-CRB RHEL 9.1
glslc rhel9-AppStream RHEL 9.0
glusterfs-cloudsync-plugins rhel9-AppStream RHEL 9.0
gnome-connections rhel9-AppStream RHEL 9.0
gnome-devel-docs rhel9-AppStream RHEL 9.0
gnome-extensions-app rhel9-AppStream RHEL 9.0
gnome-kiosk rhel9-AppStream RHEL 9.0
gnome-kiosk-script-session rhel9-AppStream RHEL 9.1
gnome-kiosk-search-appliance rhel9-AppStream RHEL 9.1
gnome-shell-extension-background-
logo
rhel9-AppStream RHEL 9.0
gnome-shell-extension-custom-menu rhel9-AppStream RHEL 9.3
gnome-shell-extension-dash-to-panel rhel9-AppStream RHEL 9.4
gnome-software-devel rhel9-CRB RHEL 9.3
gnome-themes-extra rhel9-AppStream RHEL 9.0
gnome-tour rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
86

gnu-efi-compat rhel9-CRB RHEL 9.0
go-filesystem rhel9-AppStream RHEL 9.0
go-rpm-macros rhel9-AppStream RHEL 9.0
go-rpm-templates rhel9-AppStream RHEL 9.0
golang-github-cpuguy83-md2man rhel9-CRB RHEL 9.2
google-carlito-fonts rhel9-AppStream RHEL 9.0
google-crosextra-caladea-fonts rhel9-AppStream RHEL 9.3
google-noto-sans-mono-fonts rhel9-AppStream RHEL 9.0
google-noto-sans-sinhala-vf-fonts rhel9-AppStream RHEL 9.0
google-noto-sans-symbols2-fonts rhel9-CRB RHEL 9.1
google-noto-serif-gurmukhi-vf-fonts rhel9-AppStream RHEL 9.0
google-noto-serif-sinhala-vf-fonts rhel9-AppStream RHEL 9.0
gpsd-minimal rhel9-AppStream RHEL 9.3
gpsd-minimal-clients rhel9-AppStream RHEL 9.3
grafana-selinux rhel9-AppStream RHEL 9.4
graphene rhel9-AppStream RHEL 9.0
graphene-devel rhel9-AppStream RHEL 9.0
graphviz-ruby rhel9-AppStream RHEL 9.4
gstreamer1-plugins-base-tools rhel9-AppStream RHEL 9.2
gstreamer1-rtsp-server rhel9-AppStream RHEL 9.3
gtk-vnc2-devel rhel9-CRB RHEL 9.4
gtk3-devel-docs rhel9-CRB RHEL 9.1
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
87

gtk4 rhel9-AppStream RHEL 9.0
gtk4-devel rhel9-AppStream RHEL 9.0
gtksourceview4 rhel9-AppStream RHEL 9.0
gtksourceview4-devel rhel9-CRB RHEL 9.1
guestfs-tools rhel9-AppStream RHEL 9.0
gvisor-tap-vsock rhel9-AppStream RHEL 9.4
gvnc-devel rhel9-CRB RHEL 9.4
ha-cloud-support rhel9-HighAvailability RHEL 9.0
ha-openstack-support rhel9-AppStream RHEL 9.0
highcontrast-icon-theme rhel9-AppStream RHEL 9.0
hivex-libs rhel9-AppStream RHEL 9.0
ht-caladea-fonts rhel9-AppStream RHEL 9.0
httpd-core rhel9-AppStream RHEL 9.1
hunspell-filesystem rhel9-AppStream RHEL 9.0
hwdata-devel rhel9-CRB RHEL 9.3
hyphen-eo rhel9-AppStream RHEL 9.0
ibus-anthy rhel9-AppStream RHEL 9.0
ibus-anthy-python rhel9-AppStream RHEL 9.0
idm-jss rhel9-AppStream RHEL 9.1
idm-jss-tomcat rhel9-AppStream RHEL 9.4
idm-ldapjdk rhel9-AppStream RHEL 9.1
idm-pki-acme rhel9-AppStream RHEL 9.1
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
88
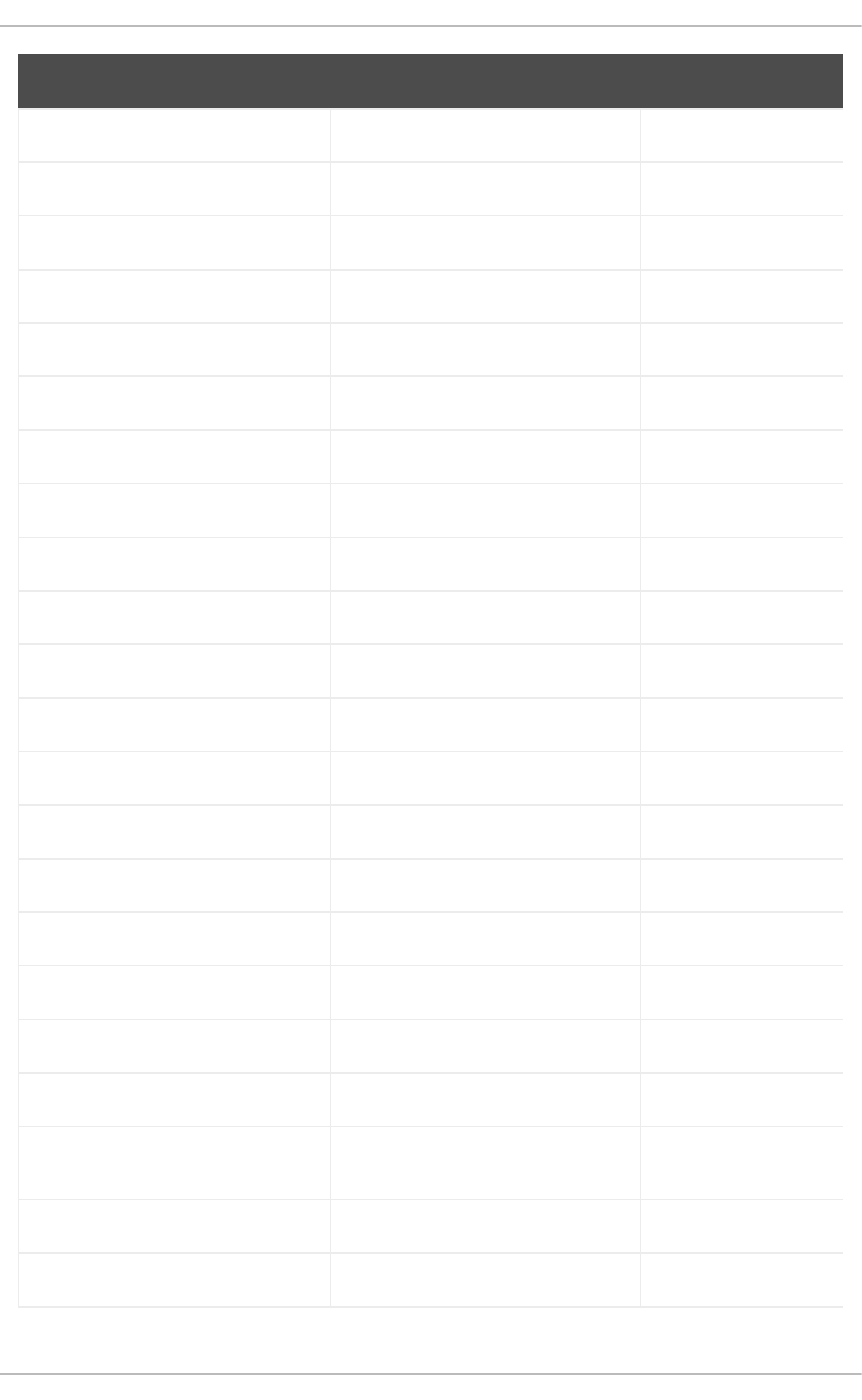
idm-pki-base rhel9-AppStream RHEL 9.1
idm-pki-ca rhel9-AppStream RHEL 9.1
idm-pki-est rhel9-AppStream RHEL 9.2
idm-pki-java rhel9-AppStream RHEL 9.1
idm-pki-kra rhel9-AppStream RHEL 9.1
idm-pki-server rhel9-AppStream RHEL 9.1
idm-pki-tools rhel9-AppStream RHEL 9.1
idm-tomcatjss rhel9-AppStream RHEL 9.1
ignition rhel9-AppStream RHEL 9.0
ignition-edge rhel9-AppStream RHEL 9.2
ignition-validate rhel9-AppStream RHEL 9.2
imath rhel9-AppStream RHEL 9.0
imath-devel rhel9-CRB RHEL 9.0
inih rhel9-BaseOS RHEL 9.0
inih-devel rhel9-CRB RHEL 9.1
initscripts-rename-device rhel9-BaseOS RHEL 9.0
initscripts-service rhel9-BaseOS RHEL 9.0
iptables-nft rhel9-BaseOS RHEL 9.0
iptables-nft-services rhel9-AppStream RHEL 9.0
jakarta-activation rhel9-AppStream RHEL 9.0
jakarta-activation2 rhel9-AppStream RHEL 9.2
jakarta-annotations rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
89

jakarta-mail rhel9-AppStream RHEL 9.0
jakarta-servlet rhel9-CRB RHEL 9.0
jasper rhel9-AppStream RHEL 9.0
jasper-utils rhel9-AppStream RHEL 9.0
java-21-openjdk rhel9-AppStream RHEL 9.3
java-21-openjdk-demo rhel9-AppStream RHEL 9.3
java-21-openjdk-demo-fastdebug rhel9-CRB RHEL 9.3
java-21-openjdk-demo-slowdebug rhel9-CRB RHEL 9.3
java-21-openjdk-devel rhel9-AppStream RHEL 9.3
java-21-openjdk-devel-fastdebug rhel9-CRB RHEL 9.3
java-21-openjdk-devel-slowdebug rhel9-CRB RHEL 9.3
java-21-openjdk-fastdebug rhel9-CRB RHEL 9.3
java-21-openjdk-headless rhel9-AppStream RHEL 9.3
java-21-openjdk-headless-fastdebug rhel9-CRB RHEL 9.3
java-21-openjdk-headless-slowdebug rhel9-CRB RHEL 9.3
java-21-openjdk-javadoc rhel9-AppStream RHEL 9.3
java-21-openjdk-javadoc-zip rhel9-AppStream RHEL 9.3
java-21-openjdk-jmods rhel9-AppStream RHEL 9.3
java-21-openjdk-jmods-fastdebug rhel9-CRB RHEL 9.3
java-21-openjdk-jmods-slowdebug rhel9-CRB RHEL 9.3
java-21-openjdk-slowdebug rhel9-CRB RHEL 9.3
java-21-openjdk-src rhel9-AppStream RHEL 9.3
java-21-openjdk-src-fastdebug rhel9-CRB RHEL 9.3
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
90

java-21-openjdk-src-slowdebug rhel9-CRB RHEL 9.3
java-21-openjdk-static-libs rhel9-AppStream RHEL 9.3
java-21-openjdk-static-libs-fastdebug rhel9-CRB RHEL 9.3
java-21-openjdk-static-libs-slowdebug rhel9-CRB RHEL 9.3
javapackages-generators rhel9-CRB RHEL 9.0
jaxb-api rhel9-AppStream RHEL 9.0
jaxb-api4 rhel9-AppStream RHEL 9.2
jaxb-codemodel rhel9-AppStream RHEL 9.2
jaxb-core rhel9-AppStream RHEL 9.2
jaxb-dtd-parser rhel9-AppStream RHEL 9.2
jaxb-istack-commons-runtime rhel9-AppStream RHEL 9.2
jaxb-istack-commons-tools rhel9-AppStream RHEL 9.2
jaxb-relaxng-datatype rhel9-AppStream RHEL 9.2
jaxb-rngom rhel9-AppStream RHEL 9.2
jaxb-runtime rhel9-AppStream RHEL 9.2
jaxb-txw2 rhel9-AppStream RHEL 9.2
jaxb-xjc rhel9-AppStream RHEL 9.2
jaxb-xsom rhel9-AppStream RHEL 9.2
jbigkit rhel9-AppStream RHEL 9.0
jbig2dec-devel rhel9-CRB RHEL 9.2
jigawatts-javadoc rhel9-AppStream RHEL 9.0
jitterentropy rhel9-BaseOS RHEL 9.0
jitterentropy-devel rhel9-CRB RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
91

jmc rhel9-CRB RHEL 9.2
jna-contrib rhel9-AppStream RHEL 9.0
kasumi-common rhel9-AppStream RHEL 9.0
kasumi-unicode rhel9-AppStream RHEL 9.0
kernel-debug-devel-matched rhel9-AppStream RHEL 9.0
kernel-devel-matched rhel9-AppStream RHEL 9.0
kernel-debug-modules-core rhel9-BaseOS RHEL 9.2
kernel-debug-uki-virt rhel9-BaseOS RHEL 9.2
kernel-modules-core rhel9-BaseOS RHEL 9.2
kernel-rt-debug-modules-core rhel9-NFV RHEL 9.2
kernel-rt-modules-core rhel9-NFV RHEL 9.2
kernel-srpm-macros rhel9-AppStream RHEL 9.0
kernel-uki-virt rhel9-BaseOS RHEL 9.2
keylime rhel9-AppStream RHEL 9.1
keylime-agent-rust rhel9-AppStream RHEL 9.1
keylime-base rhel9-AppStream RHEL 9.1
keylime-registrar rhel9-AppStream RHEL 9.1
keylime-selinux rhel9-AppStream RHEL 9.1
keylime-tenant rhel9-AppStream RHEL 9.1
keylime-verifier rhel9-AppStream RHEL 9.1
khmer-os-battambang-fonts rhel9-AppStream RHEL 9.0
khmer-os-bokor-fonts rhel9-AppStream RHEL 9.0
khmer-os-content-fonts rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
92

khmer-os-fasthand-fonts rhel9-AppStream RHEL 9.0
khmer-os-freehand-fonts rhel9-AppStream RHEL 9.0
khmer-os-handwritten-fonts rhel9-AppStream RHEL 9.0
khmer-os-metal-chrieng-fonts rhel9-AppStream RHEL 9.0
khmer-os-muol-fonts rhel9-AppStream RHEL 9.0
khmer-os-muol-fonts-all rhel9-AppStream RHEL 9.0
khmer-os-muol-pali-fonts rhel9-AppStream RHEL 9.0
khmer-os-siemreap-fonts rhel9-AppStream RHEL 9.0
khmer-os-system-fonts rhel9-AppStream RHEL 9.0
ksmtuned rhel9-AppStream RHEL 9.0
lame rhel9-AppStream RHEL 9.0
langpacks-bo rhel9-AppStream RHEL 9.0
langpacks-core-af rhel9-AppStream RHEL 9.0
langpacks-core-am rhel9-AppStream RHEL 9.0
langpacks-core-ar rhel9-AppStream RHEL 9.0
langpacks-core-as rhel9-AppStream RHEL 9.0
langpacks-core-ast rhel9-AppStream RHEL 9.0
langpacks-core-be rhel9-AppStream RHEL 9.0
langpacks-core-bg rhel9-AppStream RHEL 9.0
langpacks-core-bn rhel9-AppStream RHEL 9.0
langpacks-core-bo rhel9-AppStream RHEL 9.0
langpacks-core-br rhel9-AppStream RHEL 9.0
langpacks-core-bs rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
93

langpacks-core-ca rhel9-AppStream RHEL 9.0
langpacks-core-cs rhel9-AppStream RHEL 9.0
langpacks-core-cy rhel9-AppStream RHEL 9.0
langpacks-core-da rhel9-AppStream RHEL 9.0
langpacks-core-de rhel9-AppStream RHEL 9.0
langpacks-core-dz rhel9-AppStream RHEL 9.0
langpacks-core-el rhel9-AppStream RHEL 9.0
langpacks-core-en rhel9-AppStream RHEL 9.0
langpacks-core-en_GB rhel9-AppStream RHEL 9.0
langpacks-core-eo rhel9-AppStream RHEL 9.0
langpacks-core-es rhel9-AppStream RHEL 9.0
langpacks-core-et rhel9-AppStream RHEL 9.0
langpacks-core-eu rhel9-AppStream RHEL 9.0
langpacks-core-fa rhel9-AppStream RHEL 9.0
langpacks-core-fi rhel9-AppStream RHEL 9.0
langpacks-core-font-af rhel9-AppStream RHEL 9.0
langpacks-core-font-am rhel9-AppStream RHEL 9.0
langpacks-core-font-ar rhel9-AppStream RHEL 9.0
langpacks-core-font-as rhel9-AppStream RHEL 9.0
langpacks-core-font-ast rhel9-AppStream RHEL 9.0
langpacks-core-font-be rhel9-AppStream RHEL 9.0
langpacks-core-font-bg rhel9-AppStream RHEL 9.0
langpacks-core-font-bn rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
94

langpacks-core-font-bo rhel9-AppStream RHEL 9.0
langpacks-core-font-br rhel9-AppStream RHEL 9.0
langpacks-core-font-bs rhel9-AppStream RHEL 9.0
langpacks-core-font-ca rhel9-AppStream RHEL 9.0
langpacks-core-font-cs rhel9-AppStream RHEL 9.0
langpacks-core-font-cy rhel9-AppStream RHEL 9.0
langpacks-core-font-da rhel9-AppStream RHEL 9.0
langpacks-core-font-de rhel9-AppStream RHEL 9.0
langpacks-core-font-dz rhel9-AppStream RHEL 9.0
langpacks-core-font-el rhel9-AppStream RHEL 9.0
langpacks-core-font-en rhel9-AppStream RHEL 9.0
langpacks-core-font-eo rhel9-AppStream RHEL 9.0
langpacks-core-font-es rhel9-AppStream RHEL 9.0
langpacks-core-font-et rhel9-AppStream RHEL 9.0
langpacks-core-font-eu rhel9-AppStream RHEL 9.0
langpacks-core-font-fa rhel9-AppStream RHEL 9.0
langpacks-core-font-fi rhel9-AppStream RHEL 9.0
langpacks-core-font-fr rhel9-AppStream RHEL 9.0
langpacks-core-font-ga rhel9-AppStream RHEL 9.0
langpacks-core-font-gl rhel9-AppStream RHEL 9.0
langpacks-core-font-gu rhel9-AppStream RHEL 9.0
langpacks-core-font-he rhel9-AppStream RHEL 9.0
langpacks-core-font-hi rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
95
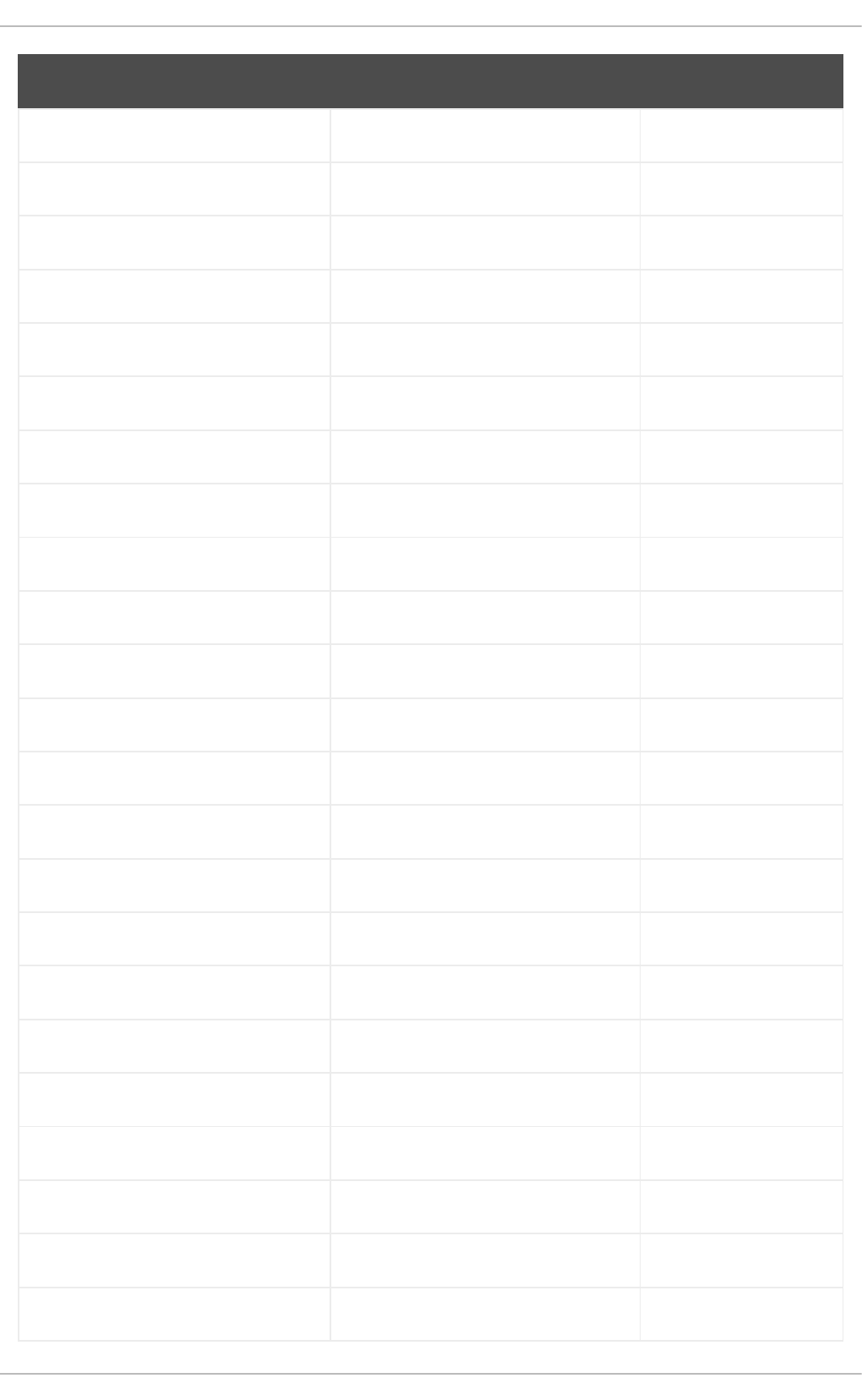
langpacks-core-font-hr rhel9-AppStream RHEL 9.0
langpacks-core-font-hu rhel9-AppStream RHEL 9.0
langpacks-core-font-ia rhel9-AppStream RHEL 9.0
langpacks-core-font-id rhel9-AppStream RHEL 9.0
langpacks-core-font-is rhel9-AppStream RHEL 9.0
langpacks-core-font-it rhel9-AppStream RHEL 9.0
langpacks-core-font-ja rhel9-AppStream RHEL 9.0
langpacks-core-font-ka rhel9-AppStream RHEL 9.0
langpacks-core-font-kk rhel9-AppStream RHEL 9.0
langpacks-core-font-km rhel9-AppStream RHEL 9.0
langpacks-core-font-kn rhel9-AppStream RHEL 9.0
langpacks-core-font-ko rhel9-AppStream RHEL 9.0
langpacks-core-font-ku rhel9-AppStream RHEL 9.0
langpacks-core-font-lt rhel9-AppStream RHEL 9.0
langpacks-core-font-lv rhel9-AppStream RHEL 9.0
langpacks-core-font-mai rhel9-AppStream RHEL 9.0
langpacks-core-font-mk rhel9-AppStream RHEL 9.0
langpacks-core-font-ml rhel9-AppStream RHEL 9.0
langpacks-core-font-mr rhel9-AppStream RHEL 9.0
langpacks-core-font-ms rhel9-AppStream RHEL 9.0
langpacks-core-font-my rhel9-AppStream RHEL 9.0
langpacks-core-font-nb rhel9-AppStream RHEL 9.0
langpacks-core-font-ne rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
96

langpacks-core-font-nl rhel9-AppStream RHEL 9.0
langpacks-core-font-nn rhel9-AppStream RHEL 9.0
langpacks-core-font-nr rhel9-AppStream RHEL 9.0
langpacks-core-font-nso rhel9-AppStream RHEL 9.0
langpacks-core-font-or rhel9-AppStream RHEL 9.0
langpacks-core-font-pa rhel9-AppStream RHEL 9.0
langpacks-core-font-pl rhel9-AppStream RHEL 9.0
langpacks-core-font-pt rhel9-AppStream RHEL 9.0
langpacks-core-font-ro rhel9-AppStream RHEL 9.0
langpacks-core-font-ru rhel9-AppStream RHEL 9.0
langpacks-core-font-si rhel9-AppStream RHEL 9.0
langpacks-core-font-sk rhel9-AppStream RHEL 9.0
langpacks-core-font-sl rhel9-AppStream RHEL 9.0
langpacks-core-font-sq rhel9-AppStream RHEL 9.0
langpacks-core-font-sr rhel9-AppStream RHEL 9.0
langpacks-core-font-ss rhel9-AppStream RHEL 9.0
langpacks-core-font-sv rhel9-AppStream RHEL 9.0
langpacks-core-font-ta rhel9-AppStream RHEL 9.0
langpacks-core-font-te rhel9-AppStream RHEL 9.0
langpacks-core-font-th rhel9-AppStream RHEL 9.0
langpacks-core-font-tn rhel9-AppStream RHEL 9.0
langpacks-core-font-tr rhel9-AppStream RHEL 9.0
langpacks-core-font-ts rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
97

langpacks-core-font-uk rhel9-AppStream RHEL 9.0
langpacks-core-font-ur rhel9-AppStream RHEL 9.0
langpacks-core-font-ve rhel9-AppStream RHEL 9.0
langpacks-core-font-vi rhel9-AppStream RHEL 9.0
langpacks-core-font-xh rhel9-AppStream RHEL 9.0
langpacks-core-font-yi rhel9-AppStream RHEL 9.0
langpacks-core-font-zh_CN rhel9-AppStream RHEL 9.0
langpacks-core-font-zh_HK rhel9-AppStream RHEL 9.0
langpacks-core-font-zh_TW rhel9-AppStream RHEL 9.0
langpacks-core-font-zu rhel9-AppStream RHEL 9.0
langpacks-core-fr rhel9-AppStream RHEL 9.0
langpacks-core-ga rhel9-AppStream RHEL 9.0
langpacks-core-gl rhel9-AppStream RHEL 9.0
langpacks-core-gu rhel9-AppStream RHEL 9.0
langpacks-core-he rhel9-AppStream RHEL 9.0
langpacks-core-hi rhel9-AppStream RHEL 9.0
langpacks-core-hr rhel9-AppStream RHEL 9.0
langpacks-core-hu rhel9-AppStream RHEL 9.0
langpacks-core-ia rhel9-AppStream RHEL 9.0
langpacks-core-id rhel9-AppStream RHEL 9.0
langpacks-core-is rhel9-AppStream RHEL 9.0
langpacks-core-it rhel9-AppStream RHEL 9.0
langpacks-core-ja rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
98
langpacks-core-ka rhel9-AppStream RHEL 9.0
langpacks-core-kk rhel9-AppStream RHEL 9.0
langpacks-core-km rhel9-AppStream RHEL 9.0
langpacks-core-kn rhel9-AppStream RHEL 9.0
langpacks-core-ko rhel9-AppStream RHEL 9.0
langpacks-core-ku rhel9-AppStream RHEL 9.0
langpacks-core-lt rhel9-AppStream RHEL 9.0
langpacks-core-lv rhel9-AppStream RHEL 9.0
langpacks-core-mai rhel9-AppStream RHEL 9.0
langpacks-core-mk rhel9-AppStream RHEL 9.0
langpacks-core-ml rhel9-AppStream RHEL 9.0
langpacks-core-mr rhel9-AppStream RHEL 9.0
langpacks-core-ms rhel9-AppStream RHEL 9.0
langpacks-core-my rhel9-AppStream RHEL 9.0
langpacks-core-nb rhel9-AppStream RHEL 9.0
langpacks-core-ne rhel9-AppStream RHEL 9.0
langpacks-core-nl rhel9-AppStream RHEL 9.0
langpacks-core-nn rhel9-AppStream RHEL 9.0
langpacks-core-nr rhel9-AppStream RHEL 9.0
langpacks-core-nso rhel9-AppStream RHEL 9.0
langpacks-core-or rhel9-AppStream RHEL 9.0
langpacks-core-pa rhel9-AppStream RHEL 9.0
langpacks-core-pl rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
99

langpacks-core-pt rhel9-AppStream RHEL 9.0
langpacks-core-pt_BR rhel9-AppStream RHEL 9.0
langpacks-core-ro rhel9-AppStream RHEL 9.0
langpacks-core-ru rhel9-AppStream RHEL 9.0
langpacks-core-si rhel9-AppStream RHEL 9.0
langpacks-core-sk rhel9-AppStream RHEL 9.0
langpacks-core-sl rhel9-AppStream RHEL 9.0
langpacks-core-sq rhel9-AppStream RHEL 9.0
langpacks-core-sr rhel9-AppStream RHEL 9.0
langpacks-core-ss rhel9-AppStream RHEL 9.0
langpacks-core-sv rhel9-AppStream RHEL 9.0
langpacks-core-ta rhel9-AppStream RHEL 9.0
langpacks-core-te rhel9-AppStream RHEL 9.0
langpacks-core-th rhel9-AppStream RHEL 9.0
langpacks-core-tn rhel9-AppStream RHEL 9.0
langpacks-core-tr rhel9-AppStream RHEL 9.0
langpacks-core-ts rhel9-AppStream RHEL 9.0
langpacks-core-uk rhel9-AppStream RHEL 9.0
langpacks-core-ur rhel9-AppStream RHEL 9.0
langpacks-core-ve rhel9-AppStream RHEL 9.0
langpacks-core-vi rhel9-AppStream RHEL 9.0
langpacks-core-xh rhel9-AppStream RHEL 9.0
langpacks-core-yi rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
100

langpacks-core-zh_CN rhel9-AppStream RHEL 9.0
langpacks-core-zh_HK rhel9-AppStream RHEL 9.0
langpacks-core-zh_TW rhel9-AppStream RHEL 9.0
langpacks-core-zu rhel9-AppStream RHEL 9.0
langpacks-dz rhel9-AppStream RHEL 9.0
langpacks-eo rhel9-AppStream RHEL 9.0
langpacks-ka rhel9-AppStream RHEL 9.0
langpacks-km rhel9-AppStream RHEL 9.0
langpacks-ku rhel9-AppStream RHEL 9.0
langpacks-my rhel9-AppStream RHEL 9.0
langpacks-yi rhel9-AppStream RHEL 9.0
langpacks-zh_HK rhel9-AppStream RHEL 9.0
lapack64 rhel9-CRB RHEL 9.3
lapack64_ rhel9-CRB RHEL 9.0
ldns-doc rhel9-CRB RHEL 9.1
ldns-utils rhel9-CRB RHEL 9.1
liba52-devel rhel9-CRB RHEL 9.0
libabigail rhel9-CRB RHEL 9.2
libadwaita rhel9-AppStream RHEL 9.4
libadwaita-devel rhel9-CRB RHEL 9.4
libasan8 rhel9-AppStream RHEL 9.1
libblkio rhel9-AppStream RHEL 9.3
libblkio-devel rhel9-CRB RHEL 9.3
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
101

libblockdev-nvme rhel9-AppStream RHEL 9.2
libblockdev-tools rhel9-AppStream RHEL 9.0
libbpf-tools rhel9-AppStream RHEL 9.0
libbrotli rhel9-BaseOS RHEL 9.0
libburn-doc rhel9-AppStream RHEL 9.0
libcbor rhel9-BaseOS RHEL 9.0
libcdr-devel rhel9-CRB RHEL 9.2
libdecor rhel9-AppStream RHEL 9.0
libdecor-devel rhel9-CRB RHEL 9.0
libdhash-devel rhel9-CRB RHEL 9.1
libdnf-plugin-subscription-manager rhel9-BaseOS RHEL 9.0
libdvdnav-devel rhel9-CRB RHEL 9.2
libeconf rhel9-BaseOS RHEL 9.0
libell rhel9-AppStream RHEL 9.0
libestr-devel rhel9-CRB RHEL 9.1
libfastjson-devel rhel9-CRB RHEL 9.3
libfdt-static rhel9-CRB RHEL 9.1
libfido2 rhel9-BaseOS RHEL 9.0
libfido2-devel rhel9-CRB RHEL 9.0
libfl-static rhel9-CRB RHEL 9.0
libfreehand-devel rhel9-CRB RHEL 9.2
libgccjit rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
102

libgccjit-devel rhel9-AppStream RHEL 9.0
libgpiod rhel9-AppStream RHEL 9.1
libgpiod-c++ rhel9-AppStream RHEL 9.1
libgpiod-devel rhel9-AppStream RHEL 9.1
libgpiod-utils rhel9-AppStream RHEL 9.1
libhandy rhel9-AppStream RHEL 9.0
libi2c-devel rhel9-CRB RHEL 9.1
libi2cd rhel9-AppStream RHEL 9.1
libi2cd-devel rhel9-AppStream RHEL 9.1
libical-glib rhel9-AppStream RHEL 9.0
libical-glib-devel rhel9-AppStream RHEL 9.0
libisoburn-doc rhel9-AppStream RHEL 9.0
libisofs-doc rhel9-AppStream RHEL 9.0
libjcat rhel9-BaseOS RHEL 9.0
libjcat-devel rhel9-CRB RHEL 9.0
libkdumpfile rhel9-AppStream RHEL 9.4
libknet1-compress-zstd-plugin rhel9-HighAvailability RHEL 9.0
libldac rhel9-AppStream RHEL 9.0
liblognorm-devel rhel9-CRB RHEL 9.3
libmemcached-awesome rhel9-CRB RHEL 9.0
libmemcached-awesome-devel rhel9-CRB RHEL 9.0
libmemcached-awesome-tools rhel9-CRB RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
103

libmpeg2 rhel9-AppStream RHEL 9.0
libmpeg2-devel rhel9-CRB RHEL 9.2
libmspub-devel rhel9-CRB RHEL 9.2
libmypaint rhel9-AppStream RHEL 9.0
libnetapi rhel9-BaseOS RHEL 9.2
libnetapi-devel rhel9-CRB RHEL 9.2
libnvme rhel9-BaseOS RHEL 9.1
libnvme-devel rhel9-CRB RHEL 9.1
libotr rhel9-AppStream RHEL 9.0
libotr-devel rhel9-CRB RHEL 9.0
libpagemaker-devel rhel9-CRB RHEL 9.2
libperf rhel9-CRB RHEL 9.3
libpmem2 rhel9-AppStream RHEL 9.0
libpmem2-debug rhel9-AppStream RHEL 9.0
libpmem2-devel rhel9-AppStream RHEL 9.0
libqrtr-glib rhel9-BaseOS RHEL 9.0
libqxp-devel rhel9-CRB RHEL 9.2
librabbitmq-tools rhel9-AppStream RHEL 9.0
libradospp-devel rhel9-CRB RHEL 9.0
librelp-devel rhel9-CRB RHEL 9.3
libreoffice rhel9-AppStream RHEL 9.2
libreoffice-help-eo rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
104

libreoffice-langpack-eo rhel9-AppStream RHEL 9.0
libreoffice-langpack-fy rhel9-AppStream RHEL 9.0
libsane-airscan rhel9-AppStream RHEL 9.0
libsbc rhel9-AppStream RHEL 9.0
libsepol-utils rhel9-AppStream RHEL 9.1
libshaderc rhel9-AppStream RHEL 9.0
libshaderc-devel rhel9-CRB RHEL 9.1
libsmartcols-devel rhel9-CRB RHEL 9.2
libsndfile-utils rhel9-AppStream RHEL 9.0
libss-devel rhel9-CRB RHEL 9.4
libstoragemgmt-devel rhel9-CRB RHEL 9.1
libstoragemgmt-nfs-plugin rhel9-AppStream RHEL 9.0
libstoragemgmt-targetd-plugin rhel9-AppStream RHEL 9.0
libtimezonemap-devel rhel9-CRB RHEL 9.4
libtracecmd rhel9-BaseOS RHEL 9.0
libtracecmd-devel rhel9-CRB RHEL 9.0
libtraceevent rhel9-BaseOS RHEL 9.0
libtraceevent-devel rhel9-CRB RHEL 9.0
libtracefs rhel9-BaseOS RHEL 9.0
libtracefs-devel rhel9-CRB RHEL 9.0
libtracker-sparql rhel9-AppStream RHEL 9.0
libtsan2 rhel9-AppStream RHEL 9.1
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
105

liburing-devel rhel9-CRB RHEL 9.3
libvala rhel9-CRB RHEL 9.0
libvala-devel rhel9-CRB RHEL 9.0
libvdpau-trace rhel9-AppStream RHEL 9.0
libverto-libev rhel9-BaseOS RHEL 9.0
libvirt-client-qemu rhel9-CRB RHEL 9.2
libvirt-daemon-common rhel9-AppStream RHEL 9.3
libvirt-daemon-lock rhel9-AppStream RHEL 9.3
libvirt-daemon-log rhel9-AppStream RHEL 9.3
libvirt-daemon-plugin-lockd rhel9-AppStream RHEL 9.3
libvirt-daemon-plugin-sanlock rhel9-CRB RHEL 9.3
libvirt-daemon-proxy rhel9-AppStream RHEL 9.3
libvma-utils rhel9-AppStream RHEL 9.0
libwebp-tools rhel9-CRB RHEL 9.2
libwmf-devel rhel9-CRB RHEL 9.1
libwpe rhel9-AppStream RHEL 9.0
libwpe-devel rhel9-CRB RHEL 9.1
libxcrypt-compat rhel9-AppStream RHEL 9.0
libxcvt rhel9-AppStream RHEL 9.2
libxcvt-devel rhel9-CRB RHEL 9.2
libxdp-devel rhel9-CRB RHEL 9.1
libxdp-static rhel9-CRB RHEL 9.1
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
106

libzip-tools rhel9-AppStream RHEL 9.4
libzmf-devel rhel9-CRB RHEL 9.2
linux-firmware-whence rhel9-BaseOS RHEL 9.0
lld-test rhel9-AppStream RHEL 9.0
lmdb rhel9-CRB RHEL 9.0
lorax-docs rhel9-AppStream RHEL 9.0
low-memory-monitor rhel9-AppStream RHEL 9.0
lua-rpm-macros rhel9-AppStream RHEL 9.0
lua-srpm-macros rhel9-AppStream RHEL 9.0
man-db-cron rhel9-AppStream RHEL 9.2
mariadb-connector-c-doc rhel9-CRB RHEL 9.0
mariadb-connector-c-test rhel9-CRB RHEL 9.0
marshalparser rhel9-CRB RHEL 9.1
maven-openjdk21 rhel9-AppStream RHEL 9.4
maven-surefire-provider-junit5 rhel9-CRB RHEL 9.0
mecab-devel rhel9-CRB RHEL 9.3
memcached-selinux rhel9-AppStream RHEL 9.0
mesa-demos rhel9-AppStream RHEL 9.0
mingw-qemu-ga-win rhel9-AppStream RHEL 9.3
mingw-w64-tools rhel9-CRB RHEL 9.2
mingw32-libgcc rhel9-CRB RHEL 9.1
mingw32-libstdc++ rhel9-CRB RHEL 9.3
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
107

mingw32-pcre2 rhel9-CRB RHEL 9.4
mingw32-pcre2-static rhel9-CRB RHEL 9.4
mingw32-srvany rhel9-AppStream RHEL 9.0
mingw64-libgcc rhel9-CRB RHEL 9.1
mingw64-libstdc++ rhel9-CRB RHEL 9.3
mingw64-pcre2 rhel9-CRB RHEL 9.4
mingw64-pcre2-static rhel9-CRB RHEL 9.4
mkfontscale rhel9-AppStream RHEL 9.0
mkpasswd rhel9-AppStream RHEL 9.1
mod_jk rhel9-AppStream RHEL 9.0
mod_lua rhel9-AppStream RHEL 9.0
mod_proxy_cluster rhel9-AppStream RHEL 9.0
mpdecimal rhel9-AppStream RHEL 9.2
mpdecimal++ rhel9-CRB RHEL 9.2
mpdecimal-devel rhel9-CRB RHEL 9.2
mpdecimal-doc rhel9-CRB RHEL 9.2
mpich-autoload rhel9-AppStream RHEL 9.0
mptcpd rhel9-AppStream RHEL 9.0
mypaint-brushes rhel9-AppStream RHEL 9.0
mythes-eo rhel9-AppStream RHEL 9.0
nbdkit-srpm-macros rhel9-CRB RHEL 9.1
netronome-firmware rhel9-BaseOS RHEL 9.0
nfs-utils-coreos rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
108

nfsv4-client-utils rhel9-AppStream RHEL 9.1
nginx-core rhel9-AppStream RHEL 9.1
nmstate-devel rhel9-CRB RHEL 9.1
nmstate-static rhel9-CRB RHEL 9.1
nodejs-devel rhel9-AppStream RHEL 9.1
nodejs-libs rhel9-AppStream RHEL 9.0
nodejs-packaging rhel9-AppStream RHEL 9.1
nodejs-packaging-bundler rhel9-AppStream RHEL 9.1
npth-devel rhel9-CRB RHEL 9.0
nss_wrapper-libs rhel9-AppStream RHEL 9.1
nvme-stas rhel9-AppStream RHEL 9.1
ocaml-brlapi rhel9-CRB RHEL 9.1
ocaml-calendar rhel9-CRB RHEL 9.1
ocaml-calendar-devel rhel9-CRB RHEL 9.1
ocaml-camomile rhel9-CRB RHEL 9.1
ocaml-camomile-data rhel9-CRB RHEL 9.1
ocaml-camomile-devel rhel9-CRB RHEL 9.1
ocaml-csexp rhel9-CRB RHEL 9.1
ocaml-csexp-devel rhel9-CRB RHEL 9.1
ocaml-csv rhel9-CRB RHEL 9.1
ocaml-csv-devel rhel9-CRB RHEL 9.1
ocaml-curses rhel9-CRB RHEL 9.1
ocaml-curses-devel rhel9-CRB RHEL 9.1
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
109
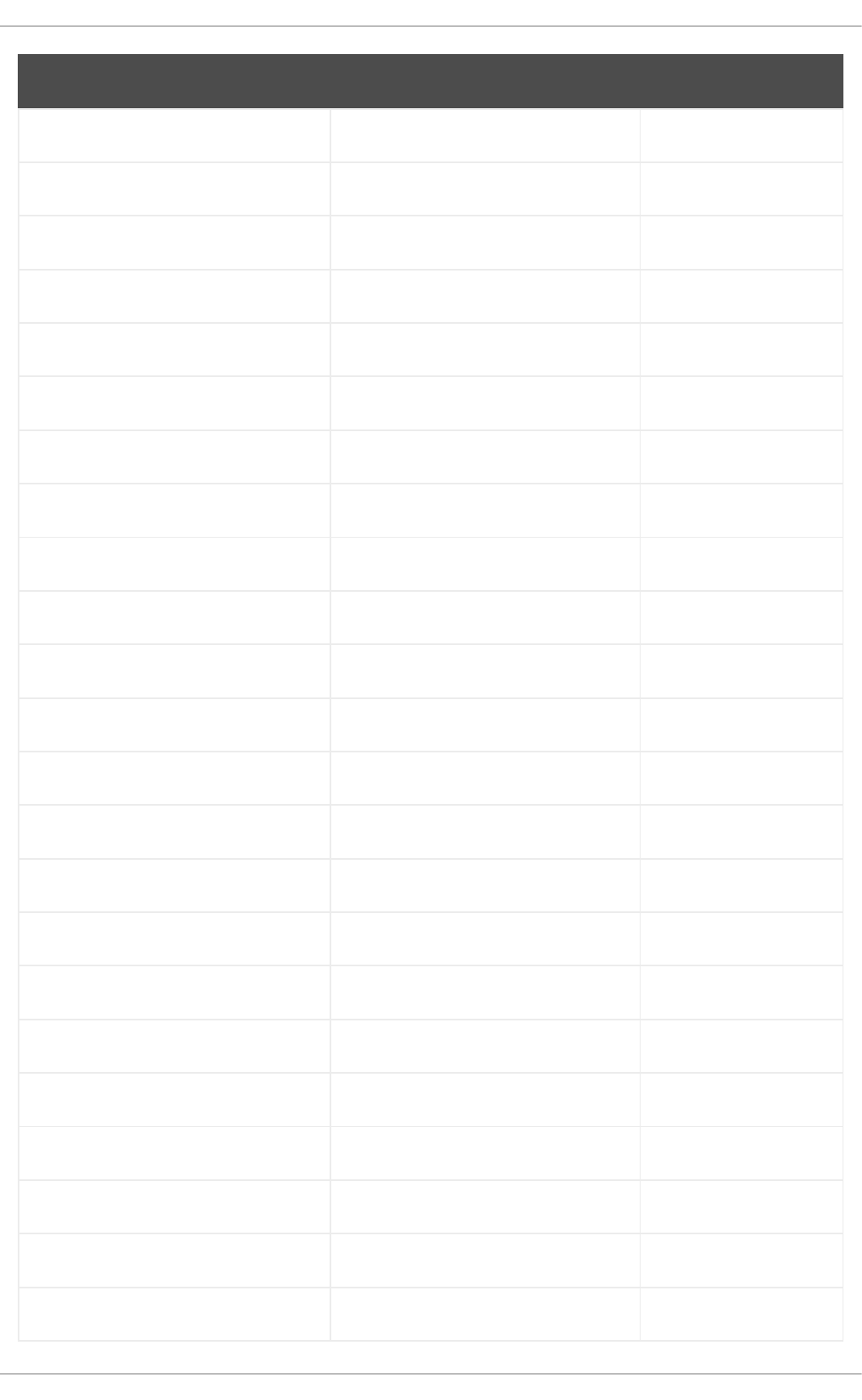
ocaml-docs rhel9-CRB RHEL 9.1
ocaml-dune rhel9-CRB RHEL 9.1
ocaml-dune-devel rhel9-CRB RHEL 9.1
ocaml-dune-doc rhel9-CRB RHEL 9.1
ocaml-dune-emacs rhel9-CRB RHEL 9.1
ocaml-fileutils rhel9-CRB RHEL 9.1
ocaml-fileutils-devel rhel9-CRB RHEL 9.1
ocaml-gettext rhel9-CRB RHEL 9.1
ocaml-gettext-devel rhel9-CRB RHEL 9.1
ocaml-libvirt rhel9-CRB RHEL 9.1
ocaml-libvirt-devel rhel9-CRB RHEL 9.1
ocaml-ocamlbuild-doc rhel9-CRB RHEL 9.1
ocaml-source rhel9-CRB RHEL 9.1
ocaml-xml-light rhel9-CRB RHEL 9.1
ocaml-xml-light-devel rhel9-CRB RHEL 9.1
open-vm-tools-salt-minion rhel9-AppStream RHEL 9.1
open-vm-tools-test rhel9-AppStream RHEL 9.0
openblas-serial rhel9-AppStream RHEL 9.0
openexr rhel9-AppStream RHEL 9.0
openexr-devel rhel9-CRB RHEL 9.0
openexr-libs rhel9-AppStream RHEL 9.0
openldap-compat rhel9-BaseOS RHEL 9.0
openmpi-java rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
110

openslp-devel rhel9-CRB RHEL 9.0
openslp-server rhel9-AppStream RHEL 9.0
openssl-fips-provider rhel9-BaseOS RHEL 9.4
osbuild-depsolve-dnf rhel9-AppStream RHEL 9.4
pam-docs rhel9-AppStream RHEL 9.0
pam_wrapper rhel9-CRB RHEL 9.1
passt rhel9-AppStream RHEL 9.2
passt-selinux rhel9-AppStream RHEL 9.2
pbzip2 rhel9-AppStream RHEL 9.0
pcp-geolocate rhel9-AppStream RHEL 9.4
pcp-pmda-bpf rhel9-AppStream RHEL 9.0
pcp-pmda-farm rhel9-AppStream RHEL 9.4
pcp-pmda-resctrl rhel9-AppStream RHEL 9.4
pcre2-syntax rhel9-BaseOS RHEL 9.0
pcre2-tools rhel9-CRB RHEL 9.4
perl-BSD-Resource rhel9-AppStream RHEL 9.0
perl-Cyrus rhel9-AppStream RHEL 9.0
perl-DBD-MariaDB rhel9-AppStream RHEL 9.0
perl-ldns rhel9-CRB RHEL 9.1
perl-Mail-AuthenticationResults rhel9-AppStream RHEL 9.0
perl-Module-Signature rhel9-AppStream RHEL 9.0
perl-Net-CIDR-Lite rhel9-AppStream RHEL 9.0
perl-Net-DNS-Nameserver rhel9-CRB RHEL 9.2
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
111

perl-XString rhel9-CRB RHEL 9.0
pf-bb-config rhel9-AppStream RHEL 9.2
php-libguestfs rhel9-CRB RHEL 9.1
pinentry-tty rhel9-AppStream RHEL 9.0
pipewire-alsa rhel9-AppStream RHEL 9.0
pipewire-gstreamer rhel9-AppStream RHEL 9.0
pipewire-jack-audio-connection-kit rhel9-AppStream RHEL 9.0
pipewire-jack-audio-connection-kit-
devel
rhel9-AppStream RHEL 9.0
pipewire-jack-audio-connection-kit-
libs
rhel9-AppStream RHEL 9.4
pipewire-module-x11 rhel9-AppStream RHEL 9.3
pipewire-pulseaudio rhel9-AppStream RHEL 9.0
pki-jackson-annotations rhel9-AppStream RHEL 9.0
pki-jackson-core rhel9-AppStream RHEL 9.0
pki-jackson-databind rhel9-AppStream RHEL 9.0
pki-jackson-jaxrs-json-provider rhel9-AppStream RHEL 9.0
pki-jackson-jaxrs-providers rhel9-AppStream RHEL 9.0
pki-jackson-module-jaxb-annotations rhel9-AppStream RHEL 9.0
pki-resteasy rhel9-AppStream RHEL 9.3
pki-resteasy-client rhel9-AppStream RHEL 9.0
pki-resteasy-core rhel9-AppStream RHEL 9.0
pki-resteasy-jackson2-provider rhel9-AppStream RHEL 9.0
pki-resteasy-servlet-initializer rhel9-AppStream RHEL 9.4
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
112
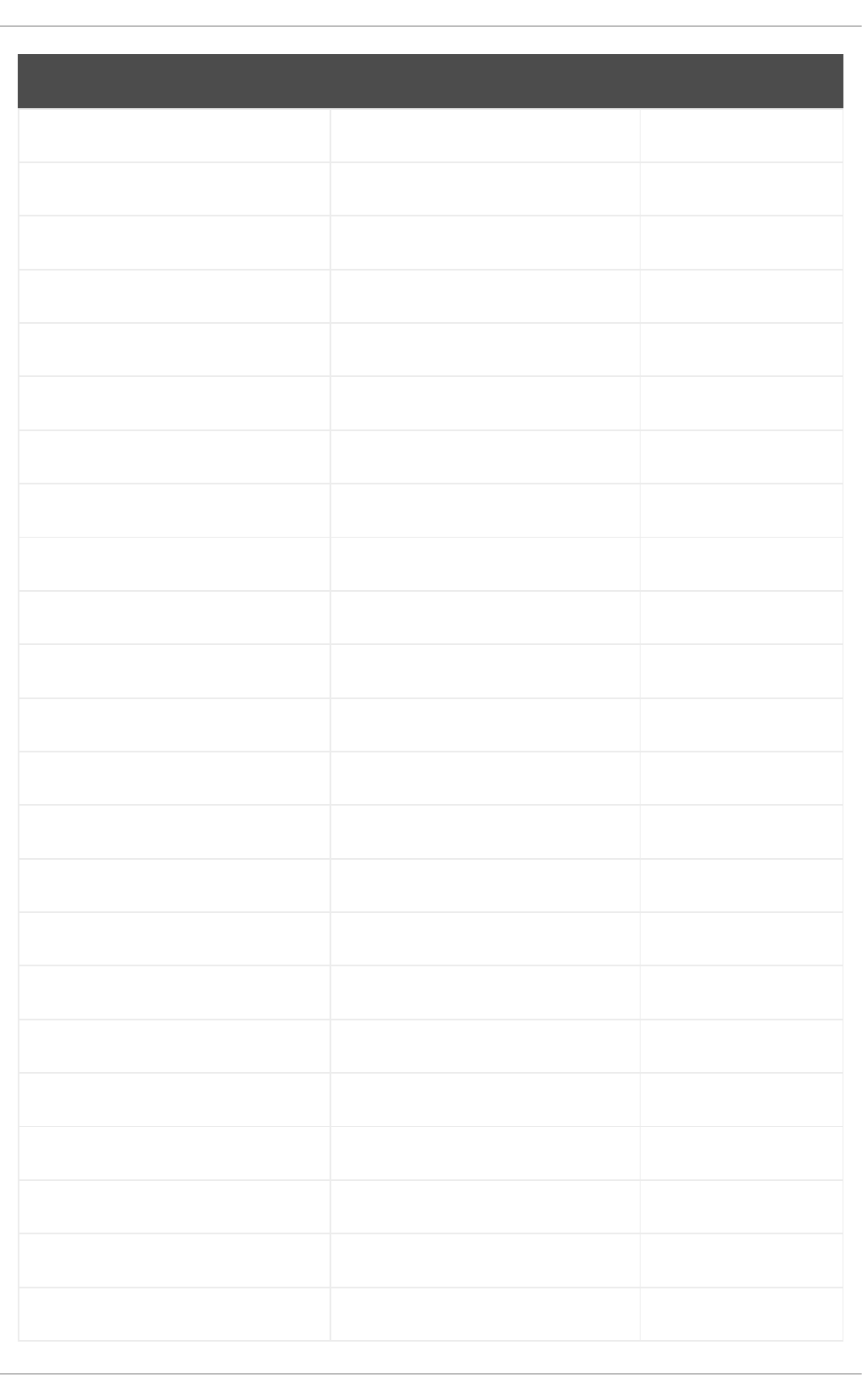
plotnetcfg rhel9-CRB RHEL 9.0
pmix-pmi rhel9-AppStream RHEL 9.0
pmix-pmi-devel rhel9-CRB RHEL 9.0
pmix-tools rhel9-AppStream RHEL 9.0
poppler-data-devel rhel9-CRB RHEL 9.2
poppler-glib-doc rhel9-CRB RHEL 9.4
postfix-lmdb rhel9-AppStream RHEL 9.3
postgresql-docs rhel9-CRB RHEL 9.1
postgresql-private-devel rhel9-CRB RHEL 9.0
postgresql-private-libs rhel9-AppStream RHEL 9.0
postgresql-static rhel9-CRB RHEL 9.1
postgresql-test-rpm-macros rhel9-AppStream RHEL 9.2
postgresql-upgrade-devel rhel9-CRB RHEL 9.1
power-profiles-daemon rhel9-AppStream RHEL 9.0
procps-ng-devel rhel9-CRB RHEL 9.2
pt-sans-fonts rhel9-AppStream RHEL 9.0
pybind11-devel rhel9-CRB RHEL 9.0
pyparsing-doc rhel9-CRB RHEL 9.0
pyproject-rpm-macros rhel9-CRB RHEL 9.0
pyproject-srpm-macros rhel9-AppStream RHEL 9.2
python-dateutil-doc rhel9-CRB RHEL 9.0
python-packaging-doc rhel9-CRB RHEL 9.0
python-sphinx-doc rhel9-CRB RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
113

python-sphinx_rtd_theme-doc rhel9-CRB RHEL 9.0
python-unversioned-command rhel9-AppStream RHEL 9.0
python3 rhel9-BaseOS RHEL 9.0
python3-alembic rhel9-AppStream RHEL 9.1
python3-appdirs rhel9-AppStream RHEL 9.0
python3-awscrt rhel9-AppStream RHEL 9.4
python3-babeltrace rhel9-CRB RHEL 9.1
python3-botocore rhel9-AppStream RHEL 9.4
python3-cairo-devel rhel9-CRB RHEL 9.1
python3-capstone rhel9-CRB RHEL 9.2
python3-cepces rhel9-AppStream RHEL 9.4
python3-debug rhel9-CRB RHEL 9.0
python3-devel rhel9-AppStream RHEL 9.0
python3-dnf-plugin-leaves rhel9-AppStream RHEL 9.3
python3-dnf-plugin-modulesync rhel9-AppStream RHEL 9.1
python3-dnf-plugin-show-leaves rhel9-AppStream RHEL 9.3
python3-file-magic rhel9-AppStream RHEL 9.0
python3-flit-core rhel9-CRB RHEL 9.4
python3-gluster rhel9-AppStream RHEL 9.0
python3-gobject-base-noarch rhel9-BaseOS RHEL 9.1
python3-gobject-devel rhel9-CRB RHEL 9.0
python3-greenlet rhel9-AppStream RHEL 9.1
python3-greenlet-devel rhel9-CRB RHEL 9.3
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
114

python3-i2c-tools rhel9-AppStream RHEL 9.1
python3-idm-pki rhel9-AppStream RHEL 9.1
python3-imath rhel9-AppStream RHEL 9.0
python3-iniconfig rhel9-CRB RHEL 9.0
python3-keylime rhel9-AppStream RHEL 9.1
python3-lark-parser rhel9-AppStream RHEL 9.1
python3-lasso rhel9-AppStream RHEL 9.2
python3-ldns rhel9-CRB RHEL 9.1
python3-libevdev rhel9-AppStream RHEL 9.0
python3-libfdt rhel9-CRB RHEL 9.1
python3-libgpiod rhel9-AppStream RHEL 9.1
python3-libnvme rhel9-AppStream RHEL 9.1
python3-net-snmp rhel9-AppStream RHEL 9.0
python3-pacemaker rhel9-HighAvailability RHEL 9.3
python3-pefile rhel9-AppStream RHEL 9.3
python3-prompt-toolkit rhel9-AppStream RHEL 9.4
python3-psutil-tests rhel9-CRB RHEL 9.0
python3-pybind11 rhel9-CRB RHEL 9.0
python3-pycdlib rhel9-AppStream RHEL 9.0
python3-pyelftools rhel9-AppStream RHEL 9.0
python3-pyrsistent rhel9-AppStream RHEL 9.0
python3-pytest-subtests rhel9-CRB RHEL 9.0
python3-pytest-timeout rhel9-CRB RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
115

python3-readthedocs-sphinx-ext rhel9-CRB RHEL 9.0
python3-requests+security rhel9-AppStream RHEL 9.0
python3-requests+socks rhel9-AppStream RHEL 9.0
python3-requests-gssapi rhel9-AppStream RHEL 9.0
python3-resolvelib rhel9-AppStream RHEL 9.0
python3-ruamel-yaml rhel9-CRB RHEL 9.0
python3-ruamel-yaml-clib rhel9-CRB RHEL 9.0
python3-samba-dc rhel9-BaseOS RHEL 9.2
python3-samba-devel rhel9-CRB RHEL 9.2
python3-samba-test rhel9-CRB RHEL 9.2
python3-scapy rhel9-AppStream RHEL 9.0
python3-scour rhel9-AppStream RHEL 9.0
python3-setuptools_scm+toml rhel9-CRB RHEL 9.0
python3-sphinx-latex rhel9-CRB RHEL 9.0
python3-sphinxcontrib-applehelp rhel9-CRB RHEL 9.0
python3-sphinxcontrib-devhelp rhel9-CRB RHEL 9.0
python3-sphinxcontrib-htmlhelp rhel9-CRB RHEL 9.0
python3-sphinxcontrib-httpdomain rhel9-CRB RHEL 9.0
python3-sphinxcontrib-jsmath rhel9-CRB RHEL 9.0
python3-sphinxcontrib-qthelp rhel9-CRB RHEL 9.0
python3-sphinxcontrib-serializinghtml rhel9-CRB RHEL 9.0
python3-sqlalchemy rhel9-AppStream RHEL 9.1
python3-toml rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
116

python3-tomli rhel9-AppStream RHEL 9.3
python3-tornado rhel9-AppStream RHEL 9.1
python3-urllib-gssapi rhel9-AppStream RHEL 9.0
python3-virt-firmware rhel9-AppStream RHEL 9.2
python3-volume_key rhel9-AppStream RHEL 9.0
python3-wcwidth rhel9-CRB RHEL 9.0
python3-websockets rhel9-AppStream RHEL 9.4
python3.11 rhel9-AppStream RHEL 9.2
python3.11-attrs rhel9-CRB RHEL 9.2
python3.11-cffi rhel9-AppStream RHEL 9.2
python3.11-charset-normalizer rhel9-AppStream RHEL 9.2
python3.11-cryptography rhel9-AppStream RHEL 9.2
python3.11-Cython rhel9-CRB RHEL 9.2
python3.11-debug rhel9-CRB RHEL 9.2
python3.11-devel rhel9-AppStream RHEL 9.2
python3.11-idle rhel9-CRB RHEL 9.2
python3.11-idna rhel9-AppStream RHEL 9.2
python3.11-iniconfig rhel9-CRB RHEL 9.2
python3.11-libs rhel9-AppStream RHEL 9.2
python3.11-lxml rhel9-AppStream RHEL 9.2
python3.11-mod_wsgi rhel9-AppStream RHEL 9.2
python3.11-numpy rhel9-AppStream RHEL 9.2
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
117

python3.11-numpy-f2py rhel9-AppStream RHEL 9.2
python3.11-packaging rhel9-CRB RHEL 9.2
python3.11-pip rhel9-AppStream RHEL 9.2
python3.11-pip-wheel rhel9-AppStream RHEL 9.2
python3.11-pluggy rhel9-CRB RHEL 9.2
python3.11-ply rhel9-AppStream RHEL 9.2
python3.11-psycopg2 rhel9-AppStream RHEL 9.2
python3.11-psycopg2-debug rhel9-CRB RHEL 9.2
python3.11-psycopg2-tests rhel9-CRB RHEL 9.2
python3.11-pybind11 rhel9-CRB RHEL 9.2
python3.11-pybind11-devel rhel9-CRB RHEL 9.2
python3.11-pycparser rhel9-AppStream RHEL 9.2
python3.11-PyMySQL rhel9-AppStream RHEL 9.2
python3.11-PyMySQL+rsa rhel9-AppStream RHEL 9.2
python3.11-pyparsing rhel9-CRB RHEL 9.2
python3.11-pysocks rhel9-AppStream RHEL 9.2
python3.11-pytest rhel9-CRB RHEL 9.2
python3.11-pyyaml rhel9-AppStream RHEL 9.2
python3.11-requests rhel9-AppStream RHEL 9.2
python3.11-requests+security rhel9-AppStream RHEL 9.2
python3.11-requests+socks rhel9-AppStream RHEL 9.2
python3.11-scipy rhel9-AppStream RHEL 9.2
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
118

python3.11-semantic_version rhel9-CRB RHEL 9.2
python3.11-setuptools rhel9-AppStream RHEL 9.2
python3.11-setuptools-rust rhel9-CRB RHEL 9.2
python3.11-setuptools-wheel rhel9-AppStream RHEL 9.2
python3.11-six rhel9-AppStream RHEL 9.2
python3.11-test rhel9-CRB RHEL 9.2
python3.11-tkinter rhel9-AppStream RHEL 9.2
python3.11-urllib3 rhel9-AppStream RHEL 9.2
python3.11-wheel rhel9-AppStream RHEL 9.2
python3.11-wheel-wheel rhel9-CRB RHEL 9.2
python3.12 rhel9-AppStream RHEL 9.4
python3.12-cffi rhel9-AppStream RHEL 9.4
python3.12-charset-normalizer rhel9-AppStream RHEL 9.4
python3.12-cryptography rhel9-AppStream RHEL 9.4
python3.12-Cython rhel9-CRB RHEL 9.4
python3.12-debug rhel9-CRB RHEL 9.4
python3.12-devel rhel9-AppStream RHEL 9.4
python3.12-flit-core rhel9-CRB RHEL 9.4
python3.12-idle rhel9-CRB RHEL 9.4
python3.12-idna rhel9-AppStream RHEL 9.4
python3.12-iniconfig rhel9-CRB RHEL 9.4
python3.12-libs rhel9-AppStream RHEL 9.4
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
119

python3.12-lxml rhel9-AppStream RHEL 9.4
python3.12-mod_wsgi rhel9-AppStream RHEL 9.4
python3.12-numpy rhel9-AppStream RHEL 9.4
python3.12-numpy-f2py rhel9-AppStream RHEL 9.4
python3.12-packaging rhel9-CRB RHEL 9.4
python3.12-pip rhel9-AppStream RHEL 9.4
python3.12-pip-wheel rhel9-AppStream RHEL 9.4
python3.12-pluggy rhel9-CRB RHEL 9.4
python3.12-ply rhel9-AppStream RHEL 9.4
python3.12-psycopg2 rhel9-AppStream RHEL 9.4
python3.12-psycopg2-debug rhel9-CRB RHEL 9.4
python3.12-psycopg2-tests rhel9-CRB RHEL 9.4
python3.12-pybind11 rhel9-CRB RHEL 9.4
python3.12-pybind11-devel rhel9-CRB RHEL 9.4
python3.12-pycparser rhel9-AppStream RHEL 9.4
python3.12-PyMySQL rhel9-AppStream RHEL 9.4
python3.12-PyMySQL+rsa rhel9-AppStream RHEL 9.4
python3.12-pytest rhel9-CRB RHEL 9.4
python3.12-pyyaml rhel9-AppStream RHEL 9.4
python3.12-requests rhel9-AppStream RHEL 9.4
python3.12-scipy rhel9-AppStream RHEL 9.4
python3.12-scipy-tests rhel9-CRB RHEL 9.4
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
120

python3.12-semantic_version rhel9-CRB RHEL 9.4
python3.12-setuptools rhel9-AppStream RHEL 9.4
python3.12-setuptools-rust rhel9-CRB RHEL 9.4
python3.12-setuptools-wheel rhel9-CRB RHEL 9.4
python3.12-test rhel9-CRB RHEL 9.4
python3.12-tkinter rhel9-AppStream RHEL 9.4
python3.12-urllib3 rhel9-AppStream RHEL 9.4
python3.12-wheel rhel9-AppStream RHEL 9.4
python3.12-wheel-wheel rhel9-CRB RHEL 9.4
qatlib-service rhel9-AppStream RHEL 9.1
qemu-ga-win rhel9-AppStream RHEL 9.0
qemu-kvm-audio-pa rhel9-AppStream RHEL 9.0
qemu-kvm-block-blkio rhel9-AppStream RHEL 9.3
qemu-kvm-device-display-virtio-gpu rhel9-AppStream RHEL 9.0
qemu-kvm-device-display-virtio-gpu-
gl
rhel9-AppStream RHEL 9.0
qemu-kvm-device-display-virtio-gpu-
pci
rhel9-AppStream RHEL 9.0
qemu-kvm-device-display-virtio-gpu-
pci-gl
rhel9-AppStream RHEL 9.0
qemu-kvm-device-display-virtio-vga rhel9-AppStream RHEL 9.0
qemu-kvm-device-display-virtio-vga-
gl
rhel9-AppStream RHEL 9.0
qemu-kvm-device-usb-host rhel9-AppStream RHEL 9.0
qemu-kvm-device-usb-redirect rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
121

qemu-kvm-tools rhel9-AppStream RHEL 9.0
qemu-kvm-ui-egl-headless rhel9-AppStream RHEL 9.0
qemu-pr-helper rhel9-AppStream RHEL 9.0
qpdf rhel9-CRB RHEL 9.1
qpdf-devel rhel9-CRB RHEL 9.2
qt5 rhel9-AppStream RHEL 9.0
qt5-doc rhel9-AppStream RHEL 9.0
qt5-qt3d-doc rhel9-AppStream RHEL 9.0
qt5-qtbase-doc rhel9-AppStream RHEL 9.0
qt5-qtcharts-doc rhel9-AppStream RHEL 9.0
qt5-qtconnectivity-doc rhel9-AppStream RHEL 9.0
qt5-qtdatavis3d-doc rhel9-AppStream RHEL 9.0
qt5-qtdeclarative-doc rhel9-AppStream RHEL 9.0
qt5-qtgamepad-doc rhel9-AppStream RHEL 9.0
qt5-qtgraphicaleffects-doc rhel9-AppStream RHEL 9.0
qt5-qtimageformats-doc rhel9-AppStream RHEL 9.0
qt5-qtlocation-doc rhel9-AppStream RHEL 9.0
qt5-qtmultimedia-doc rhel9-AppStream RHEL 9.0
qt5-qtpurchasing-doc rhel9-AppStream RHEL 9.0
qt5-qtquickcontrols-doc rhel9-AppStream RHEL 9.0
qt5-qtquickcontrols2-doc rhel9-AppStream RHEL 9.0
qt5-qtremoteobjects-doc rhel9-AppStream RHEL 9.0
qt5-qtscript-doc rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
122

qt5-qtscxml-doc rhel9-AppStream RHEL 9.0
qt5-qtsensors-doc rhel9-AppStream RHEL 9.0
qt5-qtserialbus-doc rhel9-AppStream RHEL 9.0
qt5-qtserialport-doc rhel9-AppStream RHEL 9.0
qt5-qtspeech-doc rhel9-AppStream RHEL 9.0
qt5-qtsvg-doc rhel9-AppStream RHEL 9.0
qt5-qttools-doc rhel9-AppStream RHEL 9.0
qt5-qtvirtualkeyboard-doc rhel9-AppStream RHEL 9.0
qt5-qtwayland-doc rhel9-AppStream RHEL 9.0
qt5-qtwebchannel-doc rhel9-AppStream RHEL 9.0
qt5-qtwebsockets-doc rhel9-AppStream RHEL 9.0
qt5-qtwebview-doc rhel9-AppStream RHEL 9.0
qt5-qtx11extras-doc rhel9-AppStream RHEL 9.0
qt5-qtxmlpatterns-doc rhel9-AppStream RHEL 9.0
realtime-setup rhel9-NFV RHEL 9.0
realtime-tests rhel9-AppStream RHEL 9.0
redhat-display-fonts rhel9-AppStream RHEL 9.0
redhat-cloud-client-configuration rhel9-AppStream RHEL 9.1
redhat-mono-fonts rhel9-AppStream RHEL 9.0
redhat-sb-certs rhel9-CRB RHEL 9.0
redhat-text-fonts rhel9-AppStream RHEL 9.0
resource-agents-cloud rhel9-HighAvailability RHEL 9.0
restore rhel9-BaseOS RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
123

rhc-devel rhel9-CRB RHEL 9.1
rhel-net-naming-sysattrs rhel9-BaseOS RHEL 9.4
rpm-plugin-audit rhel9-BaseOS RHEL 9.0
rpm-sign-libs rhel9-BaseOS RHEL 9.0
rsyslog-logrotate rhel9-AppStream RHEL 9.0
rtla rhel9-AppStream RHEL 9.2
ruby-bundled-gems rhel9-AppStream RHEL 9.1
rubygem-racc rhel9-AppStream RHEL 9.4
rubygem-thread_order rhel9-CRB RHEL 9.0
rust-analyzer rhel9-AppStream RHEL 9.2
rv rhel9-AppStream RHEL 9.3
s390utils rhel9-AppStream RHEL 9.4
s390utils-se-data rhel9-AppStream RHEL 9.4
s-nail rhel9-AppStream RHEL 9.0
samba-dc-libs rhel9-BaseOS RHEL 9.2
samba-dcerpc rhel9-BaseOS RHEL 9.2
samba-ldb-ldap-modules rhel9-BaseOS RHEL 9.2
samba-tools rhel9-BaseOS RHEL 9.2
samba-usershares rhel9-BaseOS RHEL 9.2
sane-airscan rhel9-AppStream RHEL 9.0
sdl12-compat rhel9-AppStream RHEL 9.0
sdl12-compat-devel rhel9-CRB RHEL 9.0
setxkbmap rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
124

sid rhel9-AppStream RHEL 9.0
sid-base-libs rhel9-AppStream RHEL 9.0
sid-iface-libs rhel9-AppStream RHEL 9.0
sid-log-libs rhel9-AppStream RHEL 9.0
sid-mod-block-blkid rhel9-AppStream RHEL 9.0
sid-mod-block-dm-mpath rhel9-AppStream RHEL 9.0
sid-mod-dummies rhel9-AppStream RHEL 9.0
sid-resource-libs rhel9-AppStream RHEL 9.0
sid-tools rhel9-AppStream RHEL 9.0
sip6 rhel9-AppStream RHEL 9.1
speech-tools-libs rhel9-AppStream RHEL 9.0
ssh-key-dir rhel9-AppStream RHEL 9.0
sssd-idp rhel9-AppStream RHEL 9.1
sssd-passkey rhel9-BaseOS RHEL 9.4
stratisd-tools rhel9-AppStream RHEL 9.3
sudo-python-plugin rhel9-AppStream RHEL 9.0
synce4l rhel9-AppStream RHEL 9.2
sysprof-capture-devel rhel9-AppStream RHEL 9.0
systemd-boot-unsigned rhel9-CRB RHEL 9.2
systemd-oomd rhel9-BaseOS RHEL 9.0
systemd-resolved rhel9-BaseOS RHEL 9.0
systemd-rpm-macros rhel9-BaseOS RHEL 9.0
tesseract-langpack-eng rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
125

tesseract-tessdata-doc rhel9-AppStream RHEL 9.0
tex-preview rhel9-AppStream RHEL 9.0
texlive-alphalph rhel9-AppStream RHEL 9.0
texlive-atbegshi rhel9-AppStream RHEL 9.0
texlive-attachfile2 rhel9-AppStream RHEL 9.0
texlive-atveryend rhel9-AppStream RHEL 9.0
texlive-auxhook rhel9-AppStream RHEL 9.0
texlive-bigintcalc rhel9-AppStream RHEL 9.0
texlive-bitset rhel9-AppStream RHEL 9.0
texlive-bookmark rhel9-AppStream RHEL 9.0
texlive-catchfile rhel9-AppStream RHEL 9.0
texlive-colorprofiles rhel9-AppStream RHEL 9.0
texlive-dehyph rhel9-AppStream RHEL 9.0
texlive-epstopdf-pkg rhel9-AppStream RHEL 9.0
texlive-etexcmds rhel9-AppStream RHEL 9.0
texlive-etoc rhel9-AppStream RHEL 9.0
texlive-footnotehyper rhel9-AppStream RHEL 9.0
texlive-gettitlestring rhel9-AppStream RHEL 9.0
texlive-gnu-freefont rhel9-CRB RHEL 9.0
texlive-grfext rhel9-AppStream RHEL 9.0
texlive-grffile rhel9-AppStream RHEL 9.0
texlive-hanging rhel9-AppStream RHEL 9.0
texlive-hobsub rhel9-AppStream RHEL 9.0
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
126

texlive-hologo rhel9-AppStream RHEL 9.0
texlive-hycolor rhel9-AppStream RHEL 9.0
texlive-hyphenex rhel9-AppStream RHEL 9.0
texlive-ifplatform rhel9-AppStream RHEL 9.0
texlive-infwarerr rhel9-AppStream RHEL 9.0
texlive-intcalc rhel9-AppStream RHEL 9.0
texlive-kvdefinekeys rhel9-AppStream RHEL 9.0
texlive-kvoptions rhel9-AppStream RHEL 9.0
texlive-kvsetkeys rhel9-AppStream RHEL 9.0
texlive-l3backend rhel9-AppStream RHEL 9.0
texlive-latexbug rhel9-AppStream RHEL 9.0
texlive-letltxmacro rhel9-AppStream RHEL 9.0
texlive-listofitems rhel9-AppStream RHEL 9.0
texlive-ltxcmds rhel9-AppStream RHEL 9.0
texlive-luahbtex rhel9-AppStream RHEL 9.0
texlive-lwarp rhel9-AppStream RHEL 9.0
texlive-minitoc rhel9-AppStream RHEL 9.0
texlive-modes rhel9-AppStream RHEL 9.0
texlive-newfloat rhel9-AppStream RHEL 9.0
texlive-newunicodechar rhel9-AppStream RHEL 9.0
texlive-notoccite rhel9-AppStream RHEL 9.0
texlive-obsolete rhel9-AppStream RHEL 9.0
texlive-pdfcolmk rhel9-AppStream RHEL 9.0
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
127

texlive-pdfescape rhel9-AppStream RHEL 9.0
texlive-pdflscape rhel9-AppStream RHEL 9.0
texlive-pdftexcmds rhel9-AppStream RHEL 9.0
texlive-ragged2e rhel9-AppStream RHEL 9.0
texlive-refcount rhel9-AppStream RHEL 9.0
texlive-rerunfilecheck rhel9-AppStream RHEL 9.0
texlive-sansmathaccent rhel9-AppStream RHEL 9.0
texlive-stackengine rhel9-AppStream RHEL 9.0
texlive-stringenc rhel9-AppStream RHEL 9.0
texlive-texlive-scripts-extra rhel9-AppStream RHEL 9.0
texlive-translator rhel9-AppStream RHEL 9.0
texlive-ucharcat rhel9-AppStream RHEL 9.0
texlive-uniquecounter rhel9-AppStream RHEL 9.0
texlive-wasy-type1 rhel9-AppStream RHEL 9.0
texlive-zref rhel9-AppStream RHEL 9.0
tomcat rhel9-AppStream RHEL 9.2
tomcat-admin-webapps rhel9-AppStream RHEL 9.2
tomcat-docs-webapp rhel9-AppStream RHEL 9.2
tomcat-el-3.0-api rhel9-AppStream RHEL 9.2
tomcat-jsp-2.3-api rhel9-AppStream RHEL 9.2
tomcat-lib rhel9-AppStream RHEL 9.2
tomcat-servlet-4.0-api rhel9-AppStream RHEL 9.2
tomcat-webapps rhel9-AppStream RHEL 9.2
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
128

totem-video-thumbnailer rhel9-AppStream RHEL 9.0
tpm2-pkcs11 rhel9-AppStream RHEL 9.0
tpm2-pkcs11-tools rhel9-AppStream RHEL 9.0
tuned-profiles-postgresql rhel9-AppStream RHEL 9.1
tuned-profiles-spectrumscale rhel9-AppStream RHEL 9.0
twolame rhel9-AppStream RHEL 9.0
uchardet rhel9-CRB RHEL 9.0
uchardet-devel rhel9-CRB RHEL 9.1
uki-direct rhel9-AppStream RHEL 9.4
unbound-devel rhel9-CRB RHEL 9.1
unifdef rhel9-CRB RHEL 9.3
uresourced rhel9-AppStream RHEL 9.0
usbredir-server rhel9-AppStream RHEL 9.2
utf8proc-devel rhel9-CRB RHEL 9.0
util-linux-core rhel9-BaseOS RHEL 9.0
uuid-c++ rhel9-AppStream RHEL 9.0
uuid-dce rhel9-AppStream RHEL 9.0
virt-p2v rhel9-AppStream RHEL 9.0
virt-win-reg rhel9-AppStream RHEL 9.0
virtiofsd rhel9-AppStream RHEL 9.0
voikko-fi rhel9-AppStream RHEL 9.0
vulkan-utility-libraries-devel rhel9-CRB RHEL 9.4
vulkan-volk-devel rhel9-AppStream RHEL 9.4
Package Repository New in
APPENDIX A. CHANGES TO PACKAGES
129

WALinuxAgent-cvm rhel9-CRB RHEL 9.3
wayland-utils rhel9-AppStream RHEL 9.0
waypipe rhel9-AppStream RHEL 9.0
wireguard-tools rhel9-AppStream RHEL 9.0
wireless-regdb rhel9-BaseOS RHEL 9.0
wireplumber rhel9-AppStream RHEL 9.0
wireplumber-libs rhel9-AppStream RHEL 9.0
wpebackend-fdo rhel9-AppStream RHEL 9.0
wpebackend-fdo-devel rhel9-CRB RHEL 9.1
xcb-util-cursor rhel9-AppStream RHEL 9.4
xcb-util-cursor-devel rhel9-AppStream RHEL 9.4
xdg-dbus-proxy rhel9-AppStream RHEL 9.0
xdg-desktop-portal-gnome rhel9-AppStream RHEL 9.1
xfsprogs-xfs_scrub rhel9-AppStream RHEL 9.0
xhtml2fo-style-xsl rhel9-AppStream RHEL 9.0
xkbcomp rhel9-AppStream RHEL 9.0
xmlstarlet rhel9-AppStream RHEL 9.1
xmlto-tex rhel9-AppStream RHEL 9.0
xmlto-xhtml rhel9-AppStream RHEL 9.0
xmvn-tools rhel9-CRB RHEL 9.0
xorg-x11-server-source rhel9-CRB RHEL 9.1
Package Repository New in
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
130

xxhash rhel9-AppStream RHEL 9.1
xxhash-devel rhel9-CRB RHEL 9.1
xxhash-doc rhel9-CRB RHEL 9.1
xxhash-libs rhel9-AppStream RHEL 9.1
yara rhel9-AppStream RHEL 9.1
yara-devel rhel9-CRB RHEL 9.1
zram-generator rhel9-AppStream RHEL 9.0
Package Repository New in
A.2. PACKAGE REPLACEMENTS
The following table lists packages that were replaced, renamed, merged, or split:
Original
package(s)
New package(s) Changed
since
Note
apache-commons-
lang (javapackages-
tools:201801),
apache-commons-
lang3
(javapackages-
tools:201801)
apache-commons-
lang3
RHEL 9.0
apache-commons-
lang (pki-deps:10.6),
apache-commons-
lang3 (maven:3.5,
maven:3.6)
apache-commons-
lang3
RHEL 9.0
bind-libs-lite bind-libs RHEL 9.0
bind-lite-devel bind-devel RHEL 9.0
binutils binutils, binutils-
gold
RHEL 9.0
clutter-gst2 clutter-gst3 RHEL 9.0
crda wireless-regdb RHEL 9.0
APPENDIX A. CHANGES TO PACKAGES
131

dnf-plugin-
subscription-
manager,
subscription-
manager
subscription-
manager
RHEL 9.0
evolution-data-
server
evolution-data-
server, evolution-
data-server-ui
RHEL 9.4
evolution-data-
server-devel
evolution-data-
server-devel,
evolution-data-
server-ui-devel
RHEL 9.4
fapolicyd-dnf-
plugin
rpm-plugin-
fapolicyd
RHEL 9.1
fio fio, fio-engine-dev-
dax, fio-engine-
http, fio-engine-
libaio, fio-engine-
libpmem, fio-
engine-nbd, fio-
engine-pmemblk,
fio-engine-rados,
fio-engine-rbd, fio-
engine-rdma
RHEL 9.0
fio fio, fio-engine-http,
fio-engine-libaio,
fio-engine-nbd, fio-
engine-rados, fio-
engine-rbd, fio-
engine-rdma
RHEL 9.0
flex-devel libfl-static RHEL 9.0
fontpackages-devel fonts-rpm-macros RHEL 9.0
fontpackages-
filesystem
fonts-filesystem RHEL 9.0
gcc-toolset-12-
binutils
gcc-toolset-13-
binutils
RHEL 9.3
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
132

genisoimage xorriso RHEL 9.0 The genisoimage package has been
replaced by the xorriso package, which now
provides the genisoimage command.
glassfish-jaxb-api
(pki-deps:10.6)
jaxb-api RHEL 9.0
glassfish-jaxb-
runtime (pki-
deps:10.6)
jaxb-impl RHEL 9.0
gnome-session-
kiosk-session
gnome-kiosk RHEL 9.0
google-crosextra-
caladea-fonts
ht-caladea-fonts RHEL 9.0
google-crosextra-
carlito-fonts
google-carlito-fonts RHEL 9.0
google-noto-mono-
fonts
google-noto-sans-
mono-fonts
RHEL 9.0
guava (maven:3.6),
guava20
(maven:3.5)
guava RHEL 9.0
guava20
(javapackages-
tools:201801)
guava RHEL 9.0
hesiod compat-hesiod RHEL 9.0
ht-caladea-fonts google-crosextra-
caladea-fonts
RHEL 9.3
httpcomponents-
client
(javapackages-
tools:201801),
jakarta-commons-
httpclient
(javapackages-
tools:201801)
httpcomponents-
client
RHEL 9.0 The jakarta-commons-httpclient package
has been replaced by the httpcomponents-
client package, which has a slightly different
API. You must port code changes from
jakarta-commons-httpclient to
httpcomponents-client.
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
133

httpcomponents-
client (maven:3.5,
maven:3.6), jakarta-
commons-httpclient
(pki-deps:10.6)
httpcomponents-
client
RHEL 9.0
ibus-kkc ibus-anthy RHEL 9.0
idm-pki-acme (pki-
core:10.6)
pki-acme RHEL 9.0
idm-pki-base (pki-
core:10.6)
pki-base RHEL 9.0
idm-pki-base-java
(pki-core:10.6)
pki-base-java RHEL 9.0
idm-pki-ca (pki-
core:10.6)
pki-ca RHEL 9.0
idm-pki-kra (pki-
core:10.6)
pki-kra RHEL 9.0
idm-pki-server (pki-
core:10.6)
pki-server RHEL 9.0
idm-pki-symkey
(pki-core:10.6)
pki-symkey RHEL 9.0
idm-pki-tools (pki-
core:10.6)
pki-tools RHEL 9.0
idm-tomcatjss idm-jss-tomcat RHEL 9.4
ilmbase imath, openexr-
devel
RHEL 9.0
initscripts initscripts,
initscripts-rename-
device, initscripts-
service
RHEL 9.0
inkscape1 inkscape RHEL 9.0
inkscape1-docs inkscape-docs RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
134

inkscape1-view inkscape-view RHEL 9.0
ipa-client
(idm:client), ipa-
client (idm:DL1)
ipa-client RHEL 9.0
ipa-client-common
(idm:client), ipa-
client-common
(idm:DL1)
ipa-client-common RHEL 9.0
ipa-client-epn
(idm:client), ipa-
client-epn (idm:DL1)
ipa-client-epn RHEL 9.0
ipa-client-samba
(idm:client), ipa-
client-samba
(idm:DL1)
ipa-client-samba RHEL 9.0
ipa-common
(idm:client), ipa-
common (idm:DL1)
ipa-common RHEL 9.0
ipa-healthcheck-
core (idm:client),
ipa-healthcheck-
core (idm:DL1)
ipa-healthcheck-
core
RHEL 9.0
ipa-selinux
(idm:client), ipa-
selinux (idm:DL1)
ipa-selinux RHEL 9.0
iptables, iptables-
arptables, iptables-
ebtables
iptables-nft RHEL 9.0
iptables-services iptables-nft-
services
RHEL 9.0
istack-commons jaxb-istack-
commons
RHEL 9.0
jackson-annotations
(pki-deps:10.6)
pki-jackson-
annotations
RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
135

jackson-core (pki-
deps:10.6)
pki-jackson-core RHEL 9.0
jackson-databind
(pki-deps:10.6)
pki-jackson-
databind
RHEL 9.0
jackson-jaxrs-json-
provider (pki-
deps:10.6)
pki-jackson-jaxrs-
json-provider
RHEL 9.0
jackson-jaxrs-
providers (pki-
deps:10.6)
pki-jackson-jaxrs-
providers
RHEL 9.0
jackson-module-
jaxb-annotations
(pki-deps:10.6)
pki-jackson-
module-jaxb-
annotations
RHEL 9.0
javamail
(javapackages-
tools:201801)
jakarta-mail RHEL 9.0 The javamail package has been replaced
with the jakarta-mail package, which is API-
compatible. Code changes might be required
to port from javamail to jakarta-mail.
jss, pki-symkey idm-jss RHEL 9.1
kernel-abi-whitelists kernel-abi-
stablelists
RHEL 9.0
khmeros-base-
fonts
khmer-os-content-
fonts, khmer-os-
system-fonts
RHEL 9.0
khmeros-
battambang-fonts
khmer-os-
battambang-fonts
RHEL 9.0
khmeros-bokor-
fonts
khmer-os-bokor-
fonts
RHEL 9.0
khmeros-
handwritten-fonts
khmer-os-fasthand-
fonts, khmer-os-
freehand-fonts
RHEL 9.0
khmeros-metal-
chrieng-fonts
khmer-os-metal-
chrieng-fonts
RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
136

khmeros-muol-
fonts
khmer-os-muol-
fonts, khmer-os-
muol-pali-fonts
RHEL 9.0
khmeros-siemreap-
fonts
khmer-os-
siemreap-fonts
RHEL 9.0
ldapjdk idm-ldapjdk RHEL 9.1
libguestfs-tools
(virt:rhel)
virt-win-reg RHEL 9.0
libguestfs-tools-c
(virt:rhel)
guestfs-tools RHEL 9.0
libmemcached libmemcached-
awesome,
libmemcached-
awesome-tools
RHEL 9.0 The libmemcached library has been
replaced by the libmemcached-awesome
fork. The package has also been moved from
the AppStream repository to the
unsupported CodeReady Linux Builder
repository.
libmemcached-
devel
libmemcached-
awesome-devel
RHEL 9.0
libmemcached-libs libmemcached-
awesome
RHEL 9.0
lorax-composer osbuild-composer RHEL 9.0
mailx s-nail RHEL 9.0 The mailx mail processing system has been
replaced by s-nail. The s-nail utility is
compatible with mailx and adds numerous
new features. The mailx package is no
longer maintained in upstream.
maven-artifact-
resolver
(javapackages-
tools:201801),
maven-artifact-
transfer
(javapackages-
tools:201801)
maven-artifact-
transfer
RHEL 9.0 The maven-artifact-resolver package has
been replaced by the maven-artifact-
transfer package, which should be API-
compatible. Code changes might be required
to port from maven-artifact-resolver to
maven-artifact-transfer.
mesa-khr-devel libglvnd-devel RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
137

mesa-libGLES libglvnd-gles RHEL 9.0
mesa-vulkan-devel mesa-vulkan-drivers RHEL 9.0
metacity gnome-kiosk RHEL 9.0 The metacity package has been replaced
with the gnome-kiosk package, which has
similar functionality.
OpenEXR-libs openexr RHEL 9.0
openssl-libs openssl-fips-
provider, openssl-
libs
RHEL 9.4
pacemaker pacemaker,
python3-pacemaker
RHEL 9.3
paratype-pt-sans-
fonts
pt-sans-fonts RHEL 9.0
perl (perl:5.24) perl-AutoLoader,
perl-AutoSplit, perl-
autouse, perl-B,
perl-base, perl-
Benchmark, perl-
blib, perl-Class-
Struct, perl-Config-
Extensions, perl-
DBM_Filter, perl-
debugger, perl-
deprecate, perl-
diagnostics, perl-
DirHandle, perl-doc,
perl-Dumpvalue,
perl-DynaLoader,
perl-encoding-
warnings, perl-
English, perl-
ExtUtils-Constant,
perl-Fcntl, perl-
fields, perl-File-
Basename, perl-
File-Compare, perl-
File-Copy, perl-
File-DosGlob, perl-
File-Find, perl-File-
stat, perl-FileCache,
perl-FileHandle,
perl-filetest, perl-
FindBin, perl-
RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
138

GDBM_File, perl-
Getopt-Std, perl-
Hash-Util, perl-
Hash-Util-
FieldHash, perl-
I18N-Collate, perl-
I18N-Langinfo, perl-
I18N-LangTags,
perl-if, perl-
interpreter, perl-
IPC-Open3, perl-
less, perl-lib, perl-
libs, perl-locale,
perl-meta-notation,
perl-mro, perl-
NDBM_File, perl-
Net, perl-NEXT,
perl-ODBM_File,
perl-Opcode, perl-
overload, perl-
overloading, perl-
ph, perl-Pod-
Functions, perl-
POSIX, perl-Safe,
perl-Search-Dict,
perl-SelectSaver,
perl-sigtrap, perl-
sort, perl-subs, perl-
Symbol, perl-Sys-
Hostname, perl-
Term-Complete,
perl-Term-
ReadLine, perl-
Text-Abbrev, perl-
Thread, perl-
Thread-Semaphore,
perl-Tie, perl-Tie-
File, perl-Tie-
Memoize, perl-Tie-
RefHash, perl-Time,
perl-Unicode-UCD,
perl-User-pwent,
perl-vars, perl-
vmsish
perl-core (perl:5.24) perl RHEL 9.0
perl-interpreter perl-AutoLoader,
perl-AutoSplit, perl-
autouse, perl-B,
perl-base, perl-
Benchmark, perl-
blib, perl-Class-
RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
139

Struct, perl-Config-
Extensions, perl-
DBM_Filter, perl-
debugger, perl-
deprecate, perl-
diagnostics, perl-
DirHandle, perl-doc,
perl-Dumpvalue,
perl-DynaLoader,
perl-encoding-
warnings, perl-
English, perl-
ExtUtils-Constant,
perl-Fcntl, perl-
fields, perl-File-
Basename, perl-
File-Compare, perl-
File-Copy, perl-
File-DosGlob, perl-
File-Find, perl-File-
stat, perl-FileCache,
perl-FileHandle,
perl-filetest, perl-
FindBin, perl-
GDBM_File, perl-
Getopt-Std, perl-
Hash-Util, perl-
Hash-Util-
FieldHash, perl-
I18N-Collate, perl-
I18N-Langinfo, perl-
I18N-LangTags,
perl-if, perl-
interpreter, perl-
IPC-Open3, perl-
less, perl-lib, perl-
locale, perl-meta-
notation, perl-mro,
perl-NDBM_File,
perl-Net, perl-
NEXT, perl-
ODBM_File, perl-
Opcode, perl-
overload, perl-
overloading, perl-
ph, perl-Pod-
Functions, perl-
POSIX, perl-Safe,
perl-Search-Dict,
perl-SelectSaver,
perl-sigtrap, perl-
sort, perl-subs, perl-
Symbol, perl-Sys-
Hostname, perl-
Term-Complete,
perl-Term-
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
140

ReadLine, perl-
Text-Abbrev, perl-
Thread, perl-
Thread-Semaphore,
perl-Tie, perl-Tie-
File, perl-Tie-
Memoize, perl-Tie-
RefHash, perl-Time,
perl-Unicode-UCD,
perl-User-pwent,
perl-vars, perl-
vmsish
php-pecl-xdebug php-pecl-xdebug3 RHEL 9.0
pipewire-jack-
audio-connection-
kit
pipewire-jack-
audio-connection-
kit, pipewire-jack-
audio-connection-
kit-libs
RHEL 9.4
pki-acme idm-pki-acme RHEL 9.1
pki-base idm-pki-base RHEL 9.1
pki-base-java idm-pki-java RHEL 9.1
pki-ca idm-pki-ca RHEL 9.1
pki-kra idm-pki-kra RHEL 9.1
pki-server idm-pki-server RHEL 9.1
pki-tools idm-pki-tools RHEL 9.1
platform-python,
python2
(python27:2.7),
python36
(python36:3.6),
python38
(python38:3.8),
python39
(python39:3.9)
python3 RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
141

platform-python-
debug, python2-
debug
(python27:2.7),
python36-debug
(python36:3.6),
python38-debug
(python38:3.8),
python39-debug
(python39-
devel:3.9)
python3-debug RHEL 9.0
platform-python-
devel, python2-
devel
(python27:2.7),
python36-devel
(python36:3.6),
python38-devel
(python38:3.8),
python39-devel
(python39:3.9)
python3-devel RHEL 9.0
platform-python-
pip, python2-pip
(python27:2.7),
python3-pip,
python38-pip
(python38:3.8),
python39-pip
(python39:3.9)
python3-pip RHEL 9.0
platform-python-
setuptools,
python2-setuptools
(python27:2.7),
python3-setuptools,
python38-
setuptools
(python38:3.8),
python39-
setuptools
(python39:3.9)
python3-setuptools RHEL 9.0
podman (container-
tools:rhel8),
podman-manpages
(container-
tools:rhel8)
podman RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
142

podman-catatonit podman RHEL 9.2 The podman-catatonit package has been
replaced by functionality within the podman
package directly. Note that no additional
subpackage is required.
podman-manpages
(container-
tools:rhel8)
podman RHEL 9.0
postgresql-
upgrade-devel
(postgresql:12),
postgresql-
upgrade-devel
(postgresql:13)
postgresql-
upgrade-devel
RHEL 9.0
pulseaudio pipewire-pulseaudio RHEL 9.0 The pulseaudio server implementation has
been replaced by the pipewire-pulseaudio
implementation. Note that only the server
implementation has been switched. The
pulseaudio client libraries are still in use.
pygobject2
(gimp:2.8)
python3-gobject RHEL 9.0
pygobject2-
codegen (gimp:2.8)
python3-gobject-
base
RHEL 9.0
pygobject2-devel
(gimp:2.8)
python3-gobject-
devel
RHEL 9.0
pygobject3-devel python3-gobject-
devel
RHEL 9.0
python2-attrs
(python27:2.7),
python3-attrs,
python38-attrs
(python38-
devel:3.8),
python39-attrs
(python39-
devel:3.9)
python3-attrs RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
143

python2-babel
(python27:2.7),
python3-babel,
python38-babel
(python38:3.8)
python3-babel RHEL 9.0
python2-chardet
(python27:2.7),
python3-chardet,
python38-chardet
(python38:3.8),
python39-chardet
(python39:3.9)
python3-chardet RHEL 9.0
python2-Cython
(python27:2.7),
python3-Cython,
python38-Cython
(python38:3.8),
python39-Cython
(python39-
devel:3.9)
python3-Cython RHEL 9.0
python2-dns
(python27:2.7),
python3-dns
python3-dns RHEL 9.0
python2-docutils
(python27:2.7),
python3-docutils
python3-docutils
(python36:3.6)
RHEL 9.0
python2-idna
(python27:2.7),
python38-idna
(python38:3.8),
python39-idna
(python39:3.9)
python3-idna RHEL 9.0
python2-jinja2
(python27:2.7),
python3-jinja2,
python38-jinja2
(python38:3.8)
python3-jinja2 RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
144

python2-libs
(python27:2.7),
python3-libs,
python38-libs
(python38:3.8),
python39-libs
(python39:3.9)
python3-libs RHEL 9.0
python2-lxml
(python27:2.7),
python3-lxml,
python38-lxml
(python38:3.8),
python39-lxml
(python39:3.9)
python3-lxml RHEL 9.0
python2-
markupsafe
(python27:2.7),
python3-
markupsafe,
python38-
markupsafe
(python38:3.8)
python3-
markupsafe
RHEL 9.0
python2-numpy
(python27:2.7),
python38-numpy
(python38:3.8),
python39-numpy
(python39:3.9)
python3-numpy RHEL 9.0
python2-numpy-
f2py (python27:2.7),
python38-numpy-
f2py
(python38:3.8),
python39-numpy-
f2py (python39:3.9)
python3-numpy-
f2py
RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
145

python2-pip-wheel
(python27:2.7),
python3-pip-wheel,
python38-pip-
wheel
(python38:3.8),
python39-pip-
wheel
(python39:3.9)
python3-pip-wheel RHEL 9.0
python2-pluggy
(python27:2.7),
python3-pluggy,
python38-pluggy
(python38-
devel:3.8),
python39-pluggy
(python39-
devel:3.9)
python3-pluggy RHEL 9.0
python2-psycopg2
(python27:2.7),
python38-psycopg2
(python38:3.8),
python39-psycopg2
(python39:3.9)
python3-psycopg2 RHEL 9.0
python2-py
(python27:2.7),
python3-py,
python38-py
(python38-
devel:3.8),
python39-py
(python39-
devel:3.9)
python3-py RHEL 9.0
python2-pygments
(python27:2.7),
python3-pygments
(python36:3.6)
python3-pygments RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
146
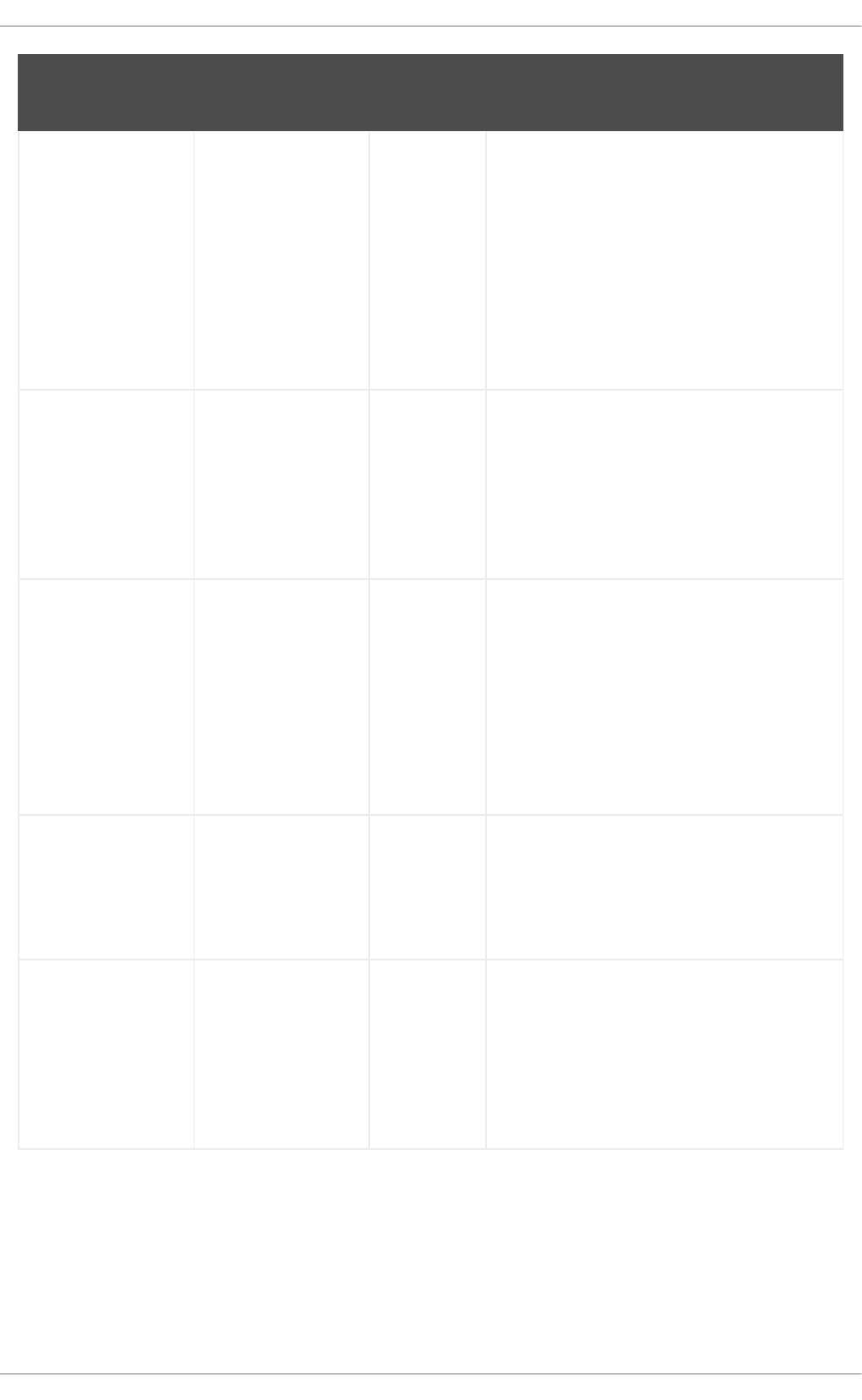
python2-PyMySQL
(python27:2.7),
python3-PyMySQL
(python36:3.6),
python38-
PyMySQL
(python38:3.8),
python39-
PyMySQL
(python39:3.9)
python3-PyMySQL RHEL 9.0
python2-pysocks
(python27:2.7),
python3-pysocks,
python38-pysocks
(python38:3.8),
python39-pysocks
(python39:3.9)
python3-pysocks RHEL 9.0
python2-pytest
(python27:2.7),
python3-pytest,
python38-pytest
(python38-
devel:3.8),
python39-pytest
(python39-
devel:3.9)
python3-pytest RHEL 9.0
python2-pytz
(python27:2.7),
python3-pytz,
python38-pytz
(python38:3.8)
python3-pytz RHEL 9.0
python2-pyyaml
(python27:2.7),
python3-pyyaml,
python38-pyyaml
(python38:3.8),
python39-pyyaml
(python39:3.9)
python3-pyyaml RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
147

python2-requests
(python27:2.7),
python3-requests,
python38-requests
(python38:3.8),
python39-requests
(python39:3.9)
python3-requests RHEL 9.0
python2-rpm-
macros
(python27:2.7),
python3-rpm-
macros, python36-
rpm-macros
(python36:3.6),
python38-rpm-
macros
(python38:3.8),
python39-rpm-
macros
(python39:3.9)
python3-rpm-
macros
RHEL 9.0
python2-scipy
(python27:2.7),
python3-scipy
(python36:3.6),
python38-scipy
(python38:3.8),
python39-scipy
(python39:3.9)
python3-scipy RHEL 9.0
python2-
setuptools-wheel
(python27:2.7),
python3-
setuptools-wheel,
python38-
setuptools-wheel
(python38:3.8),
python39-
setuptools-wheel
(python39:3.9)
python3-
setuptools-wheel
RHEL 9.0
python2-
setuptools_scm
(python27:2.7),
python3-
setuptools_scm
python3-
setuptools_scm
RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
148

python2-six
(python27:2.7),
python3-six,
python38-six
(python38:3.8),
python39-six
(python39:3.9)
python3-six RHEL 9.0
python2-test
(python27:2.7),
python3-test,
python38-test
(python38:3.8),
python39-test
(python39:3.9)
python3-test RHEL 9.0
python2-tkinter
(python27:2.7),
python3-tkinter,
python38-tkinter
(python38:3.8),
python39-tkinter
(python39:3.9)
python3-tkinter RHEL 9.0
python2-urllib3
(python27:2.7),
python3-urllib3,
python38-urllib3
(python38:3.8),
python39-urllib3
(python39:3.9)
python3-urllib3 RHEL 9.0
python2-wheel
(python27:2.7),
python3-wheel
(python36:3.6),
python38-wheel
(python38:3.8),
python39-wheel
(python39:3.9)
python3-wheel RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
149

python2-wheel-
wheel
(python27:2.7),
python3-wheel-
wheel
(python36:3.6),
python38-wheel-
wheel
(python38:3.8),
python39-wheel-
wheel
(python39:3.9)
python3-wheel-
wheel
RHEL 9.0
python3-idle,
python38-idle
(python38:3.8),
python39-idle
(python39:3.9)
python3-idle RHEL 9.0
python3-idm-pki
(pki-core:10.6)
python3-pki RHEL 9.0
python3-ipaclient
(idm:client),
python3-ipaclient
(idm:DL1)
python3-ipaclient RHEL 9.0
python3-ipalib
(idm:client),
python3-ipalib
(idm:DL1)
python3-ipalib RHEL 9.0
python3-jwcrypto
(idm:client),
python3-jwcrypto
(idm:DL1)
python3-jwcrypto RHEL 9.0
python3-magic python3-file-magic RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
150

python3-packaging,
python38-
packaging
(python38-
devel:3.8),
python39-
packaging
(python39-
devel:3.9)
python3-packaging RHEL 9.0
python3-pki python3-idm-pki RHEL 9.1
python3-pyparsing,
python38-pyparsing
(python38-
devel:3.8),
python39-pyparsing
(python39-
devel:3.9)
python3-pyparsing RHEL 9.0
python3-pyusb
(idm:client),
python3-pyusb
(idm:DL1)
python3-pyusb RHEL 9.0
python3-qrcode
(idm:DL1, idm:client)
python3-qrcode-
core
RHEL 9.0
python3-yubico
(idm:client),
python3-yubico
(idm:DL1)
python3-yubico RHEL 9.0
python38-cffi
(python38:3.8),
python39-cffi
(python39:3.9)
python3-cffi RHEL 9.0
python38-
cryptography
(python38:3.8),
python39-
cryptography
(python39:3.9)
python3-
cryptography
RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
151

python38-
mod_wsgi
(python38:3.8),
python39-
mod_wsgi
(python39:3.9)
python3-mod_wsgi RHEL 9.0
python38-ply
(python38:3.8),
python39-ply
(python39:3.9)
python3-ply RHEL 9.0
python38-psutil
(python38:3.8),
python39-psutil
(python39:3.9)
python3-psutil RHEL 9.0
python38-
pycparser
(python38:3.8),
python39-
pycparser
(python39:3.9)
python3-pycparser RHEL 9.0
python38-wcwidth
(python38-
devel:3.8),
python39-wcwidth
(python39-
devel:3.9)
python3-wcwidth RHEL 9.0
python39-iniconfig
(python39-
devel:3.9)
python3-iniconfig RHEL 9.0
python39-toml
(python39:3.9)
python3-toml RHEL 9.0
qatlib qatlib, qatlib-service RHEL 9.1
qemu-kvm ksmtuned, qemu-
kvm
RHEL 9.0
qemu-kvm-
common (virt:rhel)
qemu-kvm-
common, virtiofsd
RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
152

resource-agents-
aliyun, resource-
agents-gcp
resource-agents-
cloud
RHEL 9.0
resteasy (pki-
deps:10.6)
pki-resteasy-client,
pki-resteasy-core,
pki-resteasy-
jackson2-provider,
pki-resteasy-jaxb-
provider
RHEL 9.0
rng-tools jitterentropy,
jitterentropy-devel,
rng-tools
RHEL 9.0
rpm rpm, rpm-plugin-
audit
RHEL 9.0
rpm-build-libs rpm-build-libs, rpm-
sign-libs
RHEL 9.0
rsyslog rsyslog, rsyslog-
logrotate
RHEL 9.0
rt-setup realtime-setup RHEL 9.0
rt-setup realtime-setup RHEL 9.0
rt-tests realtime-tests RHEL 9.0
ruby-irb (ruby:2.5) rubygem-irb RHEL 9.0
rubygem-
did_you_mean
(ruby:2.5, ruby:2.6)
ruby-default-gems RHEL 9.0
rubygem-openssl
(ruby:2.5, ruby:2.6,
ruby:2.7)
ruby-default-gems RHEL 9.0
s390utils-base s390utils-base,
s390utils-se-data
RHEL 9.4
SDL sdl12-compat RHEL 9.0
SDL-devel sdl12-compat-devel RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
APPENDIX A. CHANGES TO PACKAGES
153

texlive-ifetex,
texlive-ifluatex,
texlive-ifxetex
texlive-iftex RHEL 9.0
texlive-tetex texlive-texlive-
scripts
RHEL 9.0
tomcatjss idm-tomcatjss RHEL 9.1
trace-cmd libtracecmd,
libtracecmd-devel,
trace-cmd
RHEL 9.0
vala-devel libvala-devel RHEL 9.0
wodim cdrskin RHEL 9.0 The wodim package has been replaced by
the cdrskin package. The cdrecord
executable provided by cdrskin is
compatible with cdrecord provided by
wodim.
xfsprogs xfsprogs, xfsprogs-
xfs_scrub
RHEL 9.0
xinetd systemd RHEL 9.0 The xinetd package is not available in RHEL
9. Its functionality is now provided by
systemd. For further details, see How to
convert xinetd service to systemd.
xorg-x11-font-utils mkfontscale RHEL 9.0
xorg-x11-xkb-utils setxkbmap,
xkbcomp
RHEL 9.0
Original
package(s)
New package(s) Changed
since
Note
A.3. MOVED PACKAGES
The following packages were moved between repositories within RHEL 9:
Package Original repository* Current repository* Changed since
aajohan-comfortaa-fonts rhel8-BaseOS rhel9-AppStream RHEL 9.0
adobe-source-code-pro-fonts rhel9-AppStream rhel9-BaseOS RHEL 9.2
alsa-sof-firmware rhel8-BaseOS rhel9-AppStream RHEL 9.0
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
154

ant rhel8-CRB rhel9-AppStream RHEL 9.0
ant-antlr rhel8-CRB rhel9-AppStream RHEL 9.0
ant-apache-bcel rhel8-CRB rhel9-AppStream RHEL 9.0
ant-apache-bsf rhel8-CRB rhel9-AppStream RHEL 9.0
ant-apache-oro rhel8-CRB rhel9-AppStream RHEL 9.0
ant-apache-regexp rhel8-CRB rhel9-AppStream RHEL 9.0
ant-apache-resolver rhel8-CRB rhel9-AppStream RHEL 9.0
ant-apache-xalan2 rhel8-CRB rhel9-AppStream RHEL 9.0
ant-commons-logging rhel8-CRB rhel9-AppStream RHEL 9.0
ant-commons-net rhel8-CRB rhel9-AppStream RHEL 9.0
ant-javamail rhel8-CRB rhel9-AppStream RHEL 9.0
ant-jdepend rhel8-CRB rhel9-AppStream RHEL 9.0
ant-jmf rhel8-CRB rhel9-AppStream RHEL 9.0
ant-jsch rhel8-CRB rhel9-AppStream RHEL 9.0
ant-junit rhel8-CRB rhel9-AppStream RHEL 9.0
ant-lib rhel8-CRB rhel9-AppStream RHEL 9.0
ant-swing rhel8-CRB rhel9-AppStream RHEL 9.0
ant-testutil rhel8-CRB rhel9-AppStream RHEL 9.0
ant-xz rhel8-CRB rhel9-AppStream RHEL 9.0
antlr-tool rhel8-CRB rhel9-AppStream RHEL 9.0
apache-commons-cli rhel8-CRB rhel9-AppStream RHEL 9.0
apache-commons-codec rhel8-CRB rhel9-AppStream RHEL 9.0
apache-commons-collections rhel8-AppStream rhel9-CRB RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
155

apache-commons-compress rhel8-AppStream rhel9-CRB RHEL 9.0
apache-commons-io rhel8-CRB rhel9-AppStream RHEL 9.0
apache-commons-lang3 rhel8-CRB rhel9-AppStream RHEL 9.0
apache-commons-logging rhel8-CRB rhel9-AppStream RHEL 9.0
apache-commons-net rhel8-CRB rhel9-AppStream RHEL 9.0
aspell rhel8-AppStream rhel9-CRB RHEL 9.0
assertj-core rhel8-CRB rhel9-AppStream RHEL 9.0
atinject rhel8-CRB rhel9-AppStream RHEL 9.0
atlas-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
atlas-z14 rhel8-BaseOS rhel9-AppStream RHEL 9.0
audit-libs-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
augeas rhel8-BaseOS rhel9-AppStream RHEL 9.0
augeas-libs rhel8-BaseOS rhel9-AppStream RHEL 9.0
autoconf-archive rhel8-CRB rhel9-AppStream RHEL 9.0
avahi-glib rhel8-BaseOS rhel9-AppStream RHEL 9.0
bcel rhel8-CRB rhel9-AppStream RHEL 9.0
bind-devel rhel8-AppStream rhel9-CRB RHEL 9.0
blktrace rhel8-BaseOS rhel9-AppStream RHEL 9.0
bluez-obexd rhel8-BaseOS rhel9-AppStream RHEL 9.0
boom-boot rhel8-BaseOS rhel9-AppStream RHEL 9.0
boom-boot-conf rhel8-BaseOS rhel9-AppStream RHEL 9.0
boom-boot-grub2 rhel8-BaseOS rhel9-AppStream RHEL 9.0
boost-numpy3 rhel8-CRB rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
156

boost-python3 rhel8-CRB rhel9-AppStream RHEL 9.0
brotli rhel8-BaseOS rhel9-AppStream RHEL 9.0
bsdtar rhel8-BaseOS rhel9-AppStream RHEL 9.0
bsf rhel8-CRB rhel9-AppStream RHEL 9.0
bzip2-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
c-ares-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
cdi-api rhel8-CRB rhel9-AppStream RHEL 9.0
checkpolicy rhel8-BaseOS rhel9-AppStream RHEL 9.0
conntrack-tools rhel8-BaseOS rhel9-AppStream RHEL 9.0
createrepo_c-devel rhel8-AppStream rhel9-CRB RHEL 9.0
criu-devel rhel8-AppStream rhel9-CRB RHEL 9.0
criu-devel rhel8-AppStream rhel9-CRB RHEL 9.0
cryptsetup-devel rhel8-AppStream rhel9-CRB RHEL 9.0
ctdb rhel8-BaseOS rhel9-
ResilientStorage
RHEL 9.0
cyrus-sasl-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
cyrus-sasl-gs2 rhel8-BaseOS rhel9-AppStream RHEL 9.0
cyrus-sasl-ldap rhel8-BaseOS rhel9-AppStream RHEL 9.0
cyrus-sasl-md5 rhel8-BaseOS rhel9-AppStream RHEL 9.0
cyrus-sasl-ntlm rhel8-BaseOS rhel9-AppStream RHEL 9.0
daxctl rhel8-BaseOS rhel9-AppStream RHEL 9.0
dbus-daemon rhel8-BaseOS rhel9-AppStream RHEL 9.0
dbus-glib rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
157

dlm-lib rhel8-BaseOS rhel9-AppStream RHEL 9.0
dracut-caps rhel8-BaseOS rhel9-AppStream RHEL 9.0
dracut-live rhel8-BaseOS rhel9-AppStream RHEL 9.0
dtc rhel8-CRB rhel9-AppStream RHEL 9.0
dwarves rhel8-CRB rhel9-AppStream RHEL 9.0
e2fsprogs-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
efivar rhel8-BaseOS rhel9-AppStream RHEL 9.0
elfutils-debuginfod rhel8-BaseOS rhel9-AppStream RHEL 9.0
elfutils-debuginfod-client-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
elfutils-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
elfutils-libelf-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
emacs-filesystem rhel8-BaseOS rhel9-AppStream RHEL 9.0
evolution-data-server-doc rhel8-CRB rhel9-AppStream RHEL 9.0
evolution-data-server-perl rhel8-CRB rhel9-AppStream RHEL 9.0
evolution-data-server-tests rhel8-CRB rhel9-AppStream RHEL 9.0
expat-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
expect rhel8-BaseOS rhel9-AppStream RHEL 9.0
fence-agents-all rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-all rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-amt-ws rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-amt-ws rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
158

fence-agents-apc rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-apc rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-apc-snmp rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-apc-snmp rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-bladecenter rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-bladecenter rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-brocade rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-brocade rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-cisco-mds rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-cisco-mds rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-cisco-ucs rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-cisco-ucs rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-drac5 rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-drac5 rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-eaton-snmp rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
159

fence-agents-eaton-snmp rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-emerson rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-emerson rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-eps rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-eps rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-heuristics-ping rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-heuristics-ping rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-hpblade rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-hpblade rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-ibmblade rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-ibmblade rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-ifmib rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-ifmib rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-ilo-moonshot rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-ilo-moonshot rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
160

fence-agents-ilo-mp rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-ilo-mp rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-ilo-ssh rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-ilo-ssh rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-ilo2 rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-ilo2 rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-intelmodular rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-intelmodular rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-ipdu rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-ipdu rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-ipmilan rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-ipmilan rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-kdump rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-kdump rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-lpar rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
161

fence-agents-lpar rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-mpath rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-mpath rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-redfish rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-redfish rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-rhevm rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-rhevm rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-rsa rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-rsa rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-rsb rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-rsb rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-sbd rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-sbd rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-scsi rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-scsi rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
162

fence-agents-vmware-rest rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-vmware-rest rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-vmware-soap rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-vmware-soap rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-wti rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-wti rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
fence-agents-zvm rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
fence-agents-zvm rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
flite rhel8-CRB rhel9-AppStream RHEL 9.0
fontconfig rhel8-BaseOS rhel9-AppStream RHEL 9.0
fontconfig-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
freeipmi rhel8-BaseOS rhel9-AppStream RHEL 9.0
freeipmi-bmc-watchdog rhel8-BaseOS rhel9-AppStream RHEL 9.0
freeipmi-ipmidetectd rhel8-BaseOS rhel9-AppStream RHEL 9.0
freeipmi-ipmiseld rhel8-BaseOS rhel9-AppStream RHEL 9.0
freetype-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
fstrm-devel rhel8-AppStream rhel9-CRB RHEL 9.0
fuse-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
fuse3 rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
163
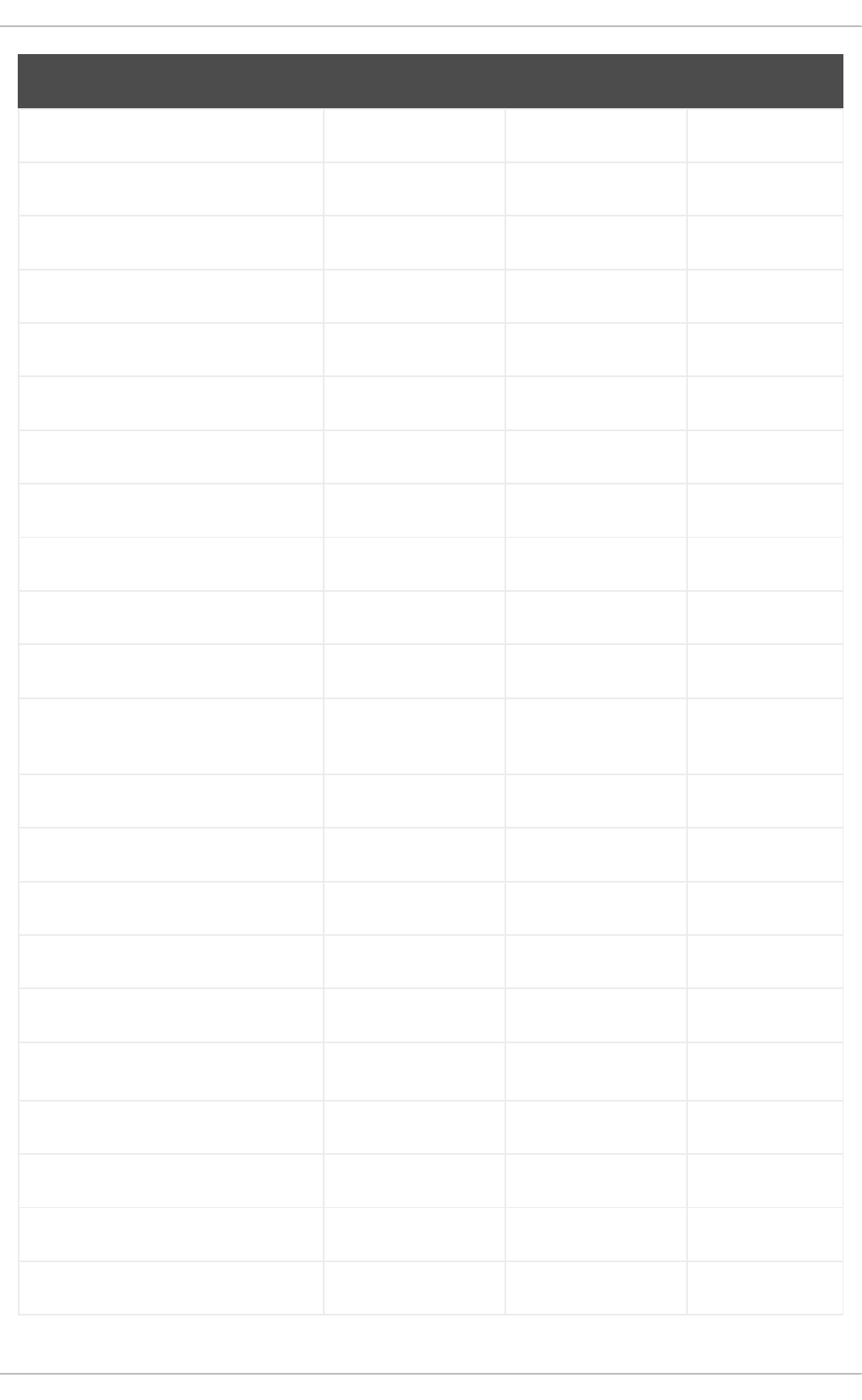
fuse3-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
fuse3-libs rhel8-BaseOS rhel9-AppStream RHEL 9.0
fxload rhel8-BaseOS rhel9-AppStream RHEL 9.0
galera rhel8-CRB rhel9-AppStream RHEL 9.0
gdbm rhel8-BaseOS rhel9-CRB RHEL 9.0
gdbm-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
gdisk rhel8-BaseOS rhel9-AppStream RHEL 9.0
gdk-pixbuf2 rhel8-BaseOS rhel9-AppStream RHEL 9.0
geoclue2-demos rhel8-AppStream rhel9-CRB RHEL 9.0
gettext-common-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
gettext-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
gfs2-utils rhel8-BaseOS rhel9-
ResilientStorage
RHEL 9.0
ghostscript-doc rhel8-CRB rhel9-AppStream RHEL 9.0
ghostscript-tools-dvipdf rhel8-CRB rhel9-AppStream RHEL 9.0
glib2-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
glib2-doc rhel8-CRB rhel9-AppStream RHEL 9.0
glib2-tests rhel8-BaseOS rhel9-AppStream RHEL 9.0
glibc-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
glibc-gconv-extra rhel8-AppStream rhel9-BaseOS RHEL 9.0
glibc-headers rhel8-BaseOS rhel9-AppStream RHEL 9.0
glibc-locale-source rhel8-BaseOS rhel9-AppStream RHEL 9.0
glusterfs rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
164

glusterfs-client-xlators rhel8-BaseOS rhel9-AppStream RHEL 9.0
glusterfs-fuse rhel8-BaseOS rhel9-AppStream RHEL 9.0
glusterfs-libs rhel8-BaseOS rhel9-AppStream RHEL 9.0
glusterfs-rdma rhel8-BaseOS rhel9-AppStream RHEL 9.0
gmp-c++ rhel8-BaseOS rhel9-AppStream RHEL 9.0
gmp-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
gnome-common rhel8-CRB rhel9-AppStream RHEL 9.0
gnu-efi rhel8-CRB rhel9-AppStream RHEL 9.0
gnupg2-smime rhel8-BaseOS rhel9-AppStream RHEL 9.0
gobject-introspection-devel rhel8-AppStream rhel9-CRB RHEL 9.0
google-guice rhel8-CRB rhel9-AppStream RHEL 9.0
google-roboto-slab-fonts rhel8-CRB rhel9-AppStream RHEL 9.0
gperf rhel8-CRB rhel9-AppStream RHEL 9.0
gpgmepp rhel8-BaseOS rhel9-AppStream RHEL 9.0
graphviz-doc rhel8-CRB rhel9-AppStream RHEL 9.0
graphviz-python3 rhel8-CRB rhel9-AppStream RHEL 9.0
groff rhel8-CRB rhel9-AppStream RHEL 9.0
gsl-devel rhel8-AppStream rhel9-CRB RHEL 9.0
gsl-devel rhel9-CRB rhel9-AppStream RHEL 9.1
gtkspell3 rhel8-AppStream rhel9-CRB RHEL 9.0
hamcrest rhel8-CRB rhel9-AppStream RHEL 9.0
hivex rhel8-CRB rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
165

hivex-devel rhel8-AppStream rhel9-CRB RHEL 9.0
httpcomponents-client rhel8-CRB rhel9-AppStream RHEL 9.0
httpcomponents-core rhel8-CRB rhel9-AppStream RHEL 9.0
hwloc-devel rhel8-CRB rhel9-AppStream RHEL 9.0
hyphen-devel rhel8-CRB rhel9-AppStream RHEL 9.0
icu rhel8-BaseOS rhel9-AppStream RHEL 9.0
infiniband-diags rhel8-BaseOS rhel9-AppStream RHEL 9.0
ipset-service rhel8-BaseOS rhel9-AppStream RHEL 9.0
iptables-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
iputils-ninfod rhel8-BaseOS rhel9-AppStream RHEL 9.0
jakarta-oro rhel8-CRB rhel9-AppStream RHEL 9.0
jansi rhel8-CRB rhel9-AppStream RHEL 9.0
jansson-devel rhel8-AppStream rhel9-CRB RHEL 9.0
javapackages-filesystem rhel8-CRB rhel9-AppStream RHEL 9.0
javapackages-tools rhel8-CRB rhel9-AppStream RHEL 9.0
jcl-over-slf4j rhel8-CRB rhel9-AppStream RHEL 9.0
jdepend rhel8-CRB rhel9-AppStream RHEL 9.0
jmc-core rhel9-AppStream rhel9-CRB RHEL 9.2
jq rhel9-AppStream rhel9-BaseOS RHEL 9.4
jsch rhel8-CRB rhel9-AppStream RHEL 9.0
json-c-devel rhel8-AppStream rhel9-CRB RHEL 9.0
jsoup rhel8-CRB rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
166

jsr-305 rhel8-CRB rhel9-AppStream RHEL 9.0
Judy rhel8-CRB rhel9-AppStream RHEL 9.0
junit rhel8-CRB rhel9-AppStream RHEL 9.0
jzlib rhel8-CRB rhel9-AppStream RHEL 9.0
kabi-dw rhel8-BaseOS rhel9-AppStream RHEL 9.0
kbd-legacy rhel8-BaseOS rhel9-AppStream RHEL 9.0
kbd-legacy rhel9-AppStream rhel9-BaseOS RHEL 9.3
kernel-cross-headers rhel8-BaseOS rhel9-CRB RHEL 9.0
kernel-debug-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
kernel-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
kernel-doc rhel8-BaseOS rhel9-AppStream RHEL 9.0
kernel-headers rhel8-BaseOS rhel9-AppStream RHEL 9.0
kernel-zfcpdump-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
keyutils-libs-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
krb5-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
ksc rhel8-BaseOS rhel9-CRB RHEL 9.0
lcms2-devel rhel8-CRB rhel9-AppStream RHEL 9.0
libacl-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libaio-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libappstream-glib rhel8-BaseOS rhel9-AppStream RHEL 9.0
libasan rhel8-BaseOS rhel9-AppStream RHEL 9.0
libatomic_ops rhel8-AppStream rhel9-CRB RHEL 9.0
libattr-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
167
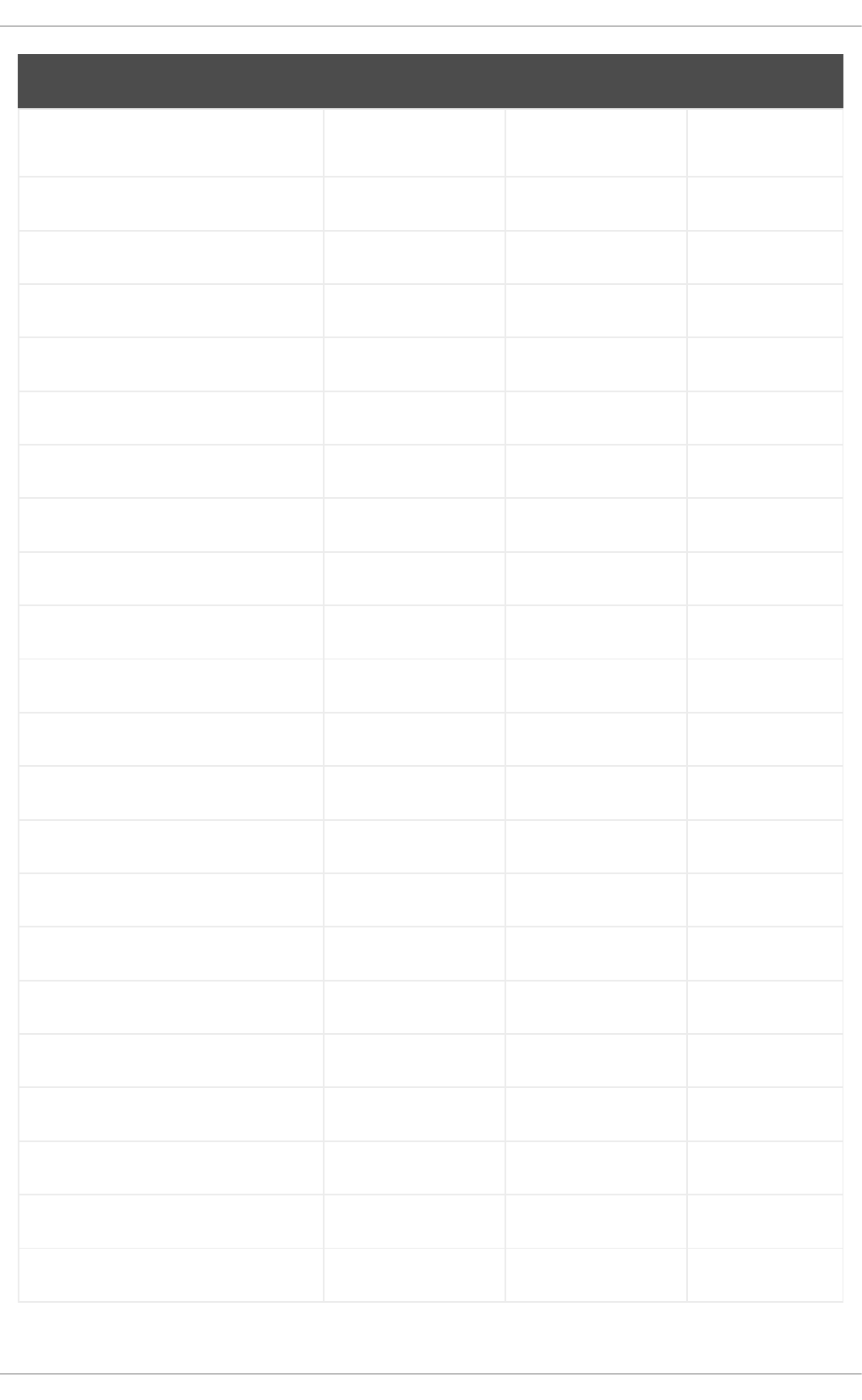
libbabeltrace rhel8-BaseOS rhel9-AppStream RHEL 9.0
libblkid-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libcap-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libcap-ng-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libcap-ng-python3 rhel8-BaseOS rhel9-AppStream RHEL 9.0
libcom_err-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libcurl-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libdatrie-devel rhel8-CRB rhel9-AppStream RHEL 9.0
libdb-utils rhel8-BaseOS rhel9-AppStream RHEL 9.0
libdwarves1 rhel8-CRB rhel9-AppStream RHEL 9.0
libedit-devel rhel8-CRB rhel9-AppStream RHEL 9.0
liberation-fonts rhel8-BaseOS rhel9-AppStream RHEL 9.0
liberation-fonts-common rhel8-BaseOS rhel9-AppStream RHEL 9.0
liberation-mono-fonts rhel8-BaseOS rhel9-AppStream RHEL 9.0
liberation-narrow-fonts rhel8-BaseOS rhel9-AppStream RHEL 9.0
liberation-sans-fonts rhel8-BaseOS rhel9-AppStream RHEL 9.0
liberation-serif-fonts rhel8-BaseOS rhel9-AppStream RHEL 9.0
libev rhel8-AppStream rhel9-BaseOS RHEL 9.0
libevent-doc rhel8-BaseOS rhel9-AppStream RHEL 9.0
libfabric rhel8-BaseOS rhel9-AppStream RHEL 9.0
libfdisk-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
libffi-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
168

libgcrypt-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libgomp-offload-nvptx rhel8-BaseOS rhel9-AppStream RHEL 9.0
libgpg-error-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libgudev-devel rhel9-CRB rhel9-AppStream RHEL 9.3
libguestfs-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libguestfs-gobject rhel8-AppStream rhel9-CRB RHEL 9.0
libguestfs-gobject-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libguestfs-man-pages-ja rhel8-AppStream rhel9-CRB RHEL 9.0
libguestfs-man-pages-uk rhel8-AppStream rhel9-CRB RHEL 9.0
libguestfs-winsupport rhel8-CRB rhel9-AppStream RHEL 9.0
libica-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
libical rhel8-BaseOS rhel9-AppStream RHEL 9.0
libicu-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libiscsi rhel8-CRB rhel9-AppStream RHEL 9.0
libiscsi-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libiscsi-utils rhel8-CRB rhel9-AppStream RHEL 9.0
libitm rhel8-BaseOS rhel9-AppStream RHEL 9.0
libjose-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libkeepalive rhel8-BaseOS rhel9-AppStream RHEL 9.0
libldb-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
liblockfile rhel9-AppStream rhel9-BaseOS RHEL 9.1
liblsan rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
169

libluksmeta-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libmaxminddb-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libmicrohttpd rhel8-BaseOS rhel9-AppStream RHEL 9.0
libmng-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libmount-devel rhel8-CRB rhel9-AppStream RHEL 9.0
libnbd rhel8-CRB rhel9-AppStream RHEL 9.0
libnbd-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libnetfilter_cthelper rhel8-BaseOS rhel9-AppStream RHEL 9.0
libnetfilter_cttimeout rhel8-BaseOS rhel9-AppStream RHEL 9.0
libnetfilter_queue rhel8-BaseOS rhel9-AppStream RHEL 9.0
libnl3-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libnsl2 rhel8-BaseOS rhel9-AppStream RHEL 9.0
libocxl rhel8-BaseOS rhel9-AppStream RHEL 9.0
libogg-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libpmem-debug rhel8-CRB rhel9-AppStream RHEL 9.0
libpmemblk-debug rhel8-CRB rhel9-AppStream RHEL 9.0
libpmemlog-debug rhel8-CRB rhel9-AppStream RHEL 9.0
libpmemobj-debug rhel8-CRB rhel9-AppStream RHEL 9.0
libpmempool-debug rhel8-CRB rhel9-AppStream RHEL 9.0
libpng-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libpsl-devel rhel8-CRB rhel9-AppStream RHEL 9.0
libpsm2 rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
170

libqb rhel8-BaseOS rhel9-AppStream RHEL 9.0
libqb-devel rhel8-BaseOS rhel9-
ResilientStorage
RHEL 9.0
libqb-devel rhel8-BaseOS rhel9-
HighAvailability
RHEL 9.0
librabbitmq rhel8-BaseOS rhel9-AppStream RHEL 9.0
librtas-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
libsecret rhel8-BaseOS rhel9-AppStream RHEL 9.0
libsecret-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libselinux-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libsepol-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libservicelog-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
libslirp-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libslirp-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libslirp-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libsoup rhel8-BaseOS rhel9-AppStream RHEL 9.0
libstemmer rhel8-BaseOS rhel9-AppStream RHEL 9.0
libstoragemgmt rhel8-BaseOS rhel9-AppStream RHEL 9.0
libstoragemgmt-arcconf-plugin rhel8-BaseOS rhel9-AppStream RHEL 9.0
libstoragemgmt-hpsa-plugin rhel8-BaseOS rhel9-AppStream RHEL 9.0
libstoragemgmt-local-plugin rhel8-BaseOS rhel9-AppStream RHEL 9.0
libstoragemgmt-megaraid-plugin rhel8-BaseOS rhel9-AppStream RHEL 9.0
libstoragemgmt-smis-plugin rhel8-BaseOS rhel9-AppStream RHEL 9.0
libstoragemgmt-udev rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
171

libtalloc-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
libtdb-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
libtevent-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
libthai-devel rhel8-CRB rhel9-AppStream RHEL 9.0
libtirpc-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
libtool-ltdl rhel8-BaseOS rhel9-AppStream RHEL 9.0
libtool-ltdl-devel rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
libtool-ltdl-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libtool-ltdl-devel rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
libtsan rhel8-BaseOS rhel9-AppStream RHEL 9.0
libubsan rhel8-BaseOS rhel9-AppStream RHEL 9.0
liburing rhel8-BaseOS rhel9-AppStream RHEL 9.0
libusb rhel8-BaseOS rhel9-AppStream RHEL 9.0
libusbx-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libuuid-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libverto-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libvirt rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-client rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-client-qemu rhel9-CRB rhel9-AppStream RHEL 9.4
libvirt-daemon rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-config-network rhel8-CRB rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
172

libvirt-daemon-config-nwfilter rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-interface rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-network rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-nodedev rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-nwfilter rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-secret rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-storage rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-storage-core rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-storage-disk rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-storage-iscsi rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-storage-logical rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-storage-mpath rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-daemon-driver-storage-scsi rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-dbus rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libvirt-docs rhel8-AppStream rhel9-CRB RHEL 9.0
libvirt-libs rhel8-CRB rhel9-AppStream RHEL 9.0
libvirt-lock-sanlock rhel8-AppStream rhel9-CRB RHEL 9.0
libvirt-nss rhel8-CRB rhel9-AppStream RHEL 9.0
libwinpr-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libxcrypt-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
libxslt rhel8-BaseOS rhel9-AppStream RHEL 9.0
libXxf86vm-devel rhel8-AppStream rhel9-CRB RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
173

libzfcphbaapi-docs rhel8-BaseOS rhel9-AppStream RHEL 9.0
libzip-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libzip-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libzip-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libzip-devel rhel8-AppStream rhel9-CRB RHEL 9.0
libzstd-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
lksctp-tools-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
lksctp-tools-doc rhel8-BaseOS rhel9-AppStream RHEL 9.0
lm_sensors rhel8-BaseOS rhel9-AppStream RHEL 9.0
lm_sensors-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
lm_sensors-libs rhel8-BaseOS rhel9-AppStream RHEL 9.0
logwatch rhel8-BaseOS rhel9-AppStream RHEL 9.0
lua-guestfs rhel8-AppStream rhel9-CRB RHEL 9.0
lua-posix rhel8-CRB rhel9-AppStream RHEL 9.0
lvm2-dbusd rhel8-BaseOS rhel9-AppStream RHEL 9.0
lvm2-lockd rhel8-BaseOS rhel9-AppStream RHEL 9.0
lynx rhel8-CRB rhel9-AppStream RHEL 9.0
lz4-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
lzo-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
lzo-minilzo rhel8-BaseOS rhel9-AppStream RHEL 9.0
m4 rhel8-BaseOS rhel9-AppStream RHEL 9.0
mariadb rhel8-CRB rhel9-AppStream RHEL 9.0
mariadb-backup rhel8-CRB rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
174

mariadb-common rhel8-CRB rhel9-AppStream RHEL 9.0
mariadb-devel rhel8-AppStream rhel9-CRB RHEL 9.0
mariadb-devel rhel8-AppStream rhel9-CRB RHEL 9.0
mariadb-embedded rhel8-CRB rhel9-AppStream RHEL 9.0
mariadb-embedded-devel rhel8-AppStream rhel9-CRB RHEL 9.0
mariadb-embedded-devel rhel8-AppStream rhel9-CRB RHEL 9.0
mariadb-errmsg rhel8-CRB rhel9-AppStream RHEL 9.0
mariadb-gssapi-server rhel8-CRB rhel9-AppStream RHEL 9.0
mariadb-oqgraph-engine rhel8-CRB rhel9-AppStream RHEL 9.0
mariadb-server rhel8-CRB rhel9-AppStream RHEL 9.0
mariadb-server-galera rhel8-CRB rhel9-AppStream RHEL 9.0
mariadb-server-utils rhel8-CRB rhel9-AppStream RHEL 9.0
mariadb-test rhel8-AppStream rhel9-CRB RHEL 9.0
mariadb-test rhel8-AppStream rhel9-CRB RHEL 9.0
maven rhel8-CRB rhel9-AppStream RHEL 9.0
maven-lib rhel8-CRB rhel9-AppStream RHEL 9.0
maven-resolver rhel8-CRB rhel9-AppStream RHEL 9.0
maven-shared-utils rhel8-CRB rhel9-AppStream RHEL 9.0
maven-wagon rhel8-CRB rhel9-AppStream RHEL 9.0
memstrack rhel8-BaseOS rhel9-AppStream RHEL 9.0
memtest86+ rhel8-BaseOS rhel9-AppStream RHEL 9.0
mesa-libgbm-devel rhel9-CRB rhel9-AppStream RHEL 9.3
mesa-libOSMesa rhel8-AppStream rhel9-CRB RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
175

mobile-broadband-provider-info rhel8-BaseOS rhel9-AppStream RHEL 9.0
multilib-rpm-config rhel8-AppStream rhel9-CRB RHEL 9.0
mvapich2-psm2-devel rhel8-AppStream rhel9-CRB RHEL 9.0
mysql-devel rhel8-AppStream rhel9-CRB RHEL 9.0
mysql-libs rhel8-AppStream rhel9-CRB RHEL 9.0
mysql-test rhel8-AppStream rhel9-CRB RHEL 9.0
nbdfuse rhel8-CRB rhel9-AppStream RHEL 9.0
nbdkit-devel rhel8-AppStream rhel9-CRB RHEL 9.0
nbdkit-example-plugins rhel8-AppStream rhel9-CRB RHEL 9.0
ncurses-c++-libs rhel8-BaseOS rhel9-AppStream RHEL 9.0
ncurses-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
ncurses-term rhel8-BaseOS rhel9-AppStream RHEL 9.0
net-snmp-libs rhel8-BaseOS rhel9-AppStream RHEL 9.0
NetworkManager-config-
connectivity-redhat
rhel8-BaseOS rhel9-AppStream RHEL 9.0
NetworkManager-dispatcher-routing-
rules
rhel8-BaseOS rhel9-AppStream RHEL 9.0
NetworkManager-ovs rhel8-BaseOS rhel9-AppStream RHEL 9.0
NetworkManager-ppp rhel8-BaseOS rhel9-AppStream RHEL 9.0
nginx-mod-devel rhel8-AppStream rhel9-CRB RHEL 9.0
nispor-devel rhel8-AppStream rhel9-CRB RHEL 9.0
nss_db rhel8-BaseOS rhel9-CRB RHEL 9.0
ntsysv rhel8-BaseOS rhel9-AppStream RHEL 9.0
numactl-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
176

oniguruma rhel9-AppStream rhel9-BaseOS RHEL 9.4
objectweb-asm rhel8-CRB rhel9-AppStream RHEL 9.0
opa-address-resolution rhel8-BaseOS rhel9-AppStream RHEL 9.0
opa-basic-tools rhel8-BaseOS rhel9-AppStream RHEL 9.0
opa-fastfabric rhel8-BaseOS rhel9-AppStream RHEL 9.0
opa-fm rhel8-BaseOS rhel9-AppStream RHEL 9.0
opa-libopamgt rhel8-BaseOS rhel9-AppStream RHEL 9.0
opal-firmware rhel8-BaseOS rhel9-AppStream RHEL 9.0
opal-utils rhel8-BaseOS rhel9-AppStream RHEL 9.0
openblas-openmp rhel8-CRB rhel9-AppStream RHEL 9.0
openblas-threads rhel8-AppStream rhel9-CRB RHEL 9.0
opencl-headers rhel8-CRB rhel9-AppStream RHEL 9.0
opencsd rhel8-BaseOS rhel9-AppStream RHEL 9.0
OpenIPMI rhel8-BaseOS rhel9-AppStream RHEL 9.0
OpenIPMI-lanserv rhel8-BaseOS rhel9-AppStream RHEL 9.0
OpenIPMI-libs rhel8-BaseOS rhel9-AppStream RHEL 9.0
openldap-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
openssl-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
openssl-perl rhel8-BaseOS rhel9-AppStream RHEL 9.0
openwsman-client rhel8-AppStream rhel9-CRB RHEL 9.0
openwsman-python3 rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
177

openwsman-python3 rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
opus-devel rhel8-AppStream rhel9-CRB RHEL 9.0
ostree-devel rhel8-AppStream rhel9-CRB RHEL 9.0
owasp-java-encoder rhel9-AppStream rhel9-CRB RHEL 9.2
p11-kit-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
p11-kit-server rhel8-BaseOS rhel9-AppStream RHEL 9.0
pacemaker-cluster-libs rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
pacemaker-cluster-libs rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
pacemaker-libs rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
pacemaker-libs rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
pacemaker-schemas rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
pacemaker-schemas rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
pam-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
pam_cifscreds rhel8-BaseOS rhel9-AppStream RHEL 9.0
pam_ssh_agent_auth rhel8-BaseOS rhel9-AppStream RHEL 9.0
patch rhel8-BaseOS rhel9-AppStream RHEL 9.0
pciutils-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
pcre-cpp rhel8-BaseOS rhel9-AppStream RHEL 9.0
pcre-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
pcre-utf16 rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
178

pcre-utf32 rhel8-BaseOS rhel9-AppStream RHEL 9.0
pcre2-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
pcre2-utf16 rhel8-BaseOS rhel9-AppStream RHEL 9.0
pcre2-utf32 rhel8-BaseOS rhel9-AppStream RHEL 9.0
perf rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Algorithm-Diff rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Archive-Tar rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Carp rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Clone rhel8-CRB rhel9-AppStream RHEL 9.0
perl-Compress-Raw-Bzip2 rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Compress-Raw-Zlib rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-constant rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Data-Dumper rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Date-Manip rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-DBD-SQLite rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-DBI rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Digest-SHA1 rhel8-CRB rhel9-AppStream RHEL 9.0
perl-Errno rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Exporter rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Exporter-Tiny rhel8-CRB rhel9-AppStream RHEL 9.0
perl-File-Path rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-File-Temp rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Getopt-Long rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
179

perl-hivex rhel8-CRB rhel9-AppStream RHEL 9.0
perl-HTTP-Tiny rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Importer rhel8-CRB rhel9-AppStream RHEL 9.0
perl-interpreter rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-IO rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-IO-Compress rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-IO-String rhel8-AppStream rhel9-CRB RHEL 9.0
perl-IO-Zlib rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-libs rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-List-MoreUtils rhel8-CRB rhel9-AppStream RHEL 9.0
perl-List-MoreUtils-XS rhel8-CRB rhel9-AppStream RHEL 9.0
perl-macros rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Math-Complex rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-MIME-Base64 rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-MIME-Charset rhel8-CRB rhel9-AppStream RHEL 9.0
perl-Module-Pluggable rhel8-AppStream rhel9-CRB RHEL 9.0
perl-Module-Runtime rhel8-AppStream rhel9-CRB RHEL 9.0
perl-parent rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Parse-Yapp rhel8-BaseOS rhel9-CRB RHEL 9.0
perl-PathTools rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Pod-Escapes rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Pod-Parser rhel8-AppStream rhel9-CRB RHEL 9.0
perl-Pod-Parser rhel8-AppStream rhel9-CRB RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
180
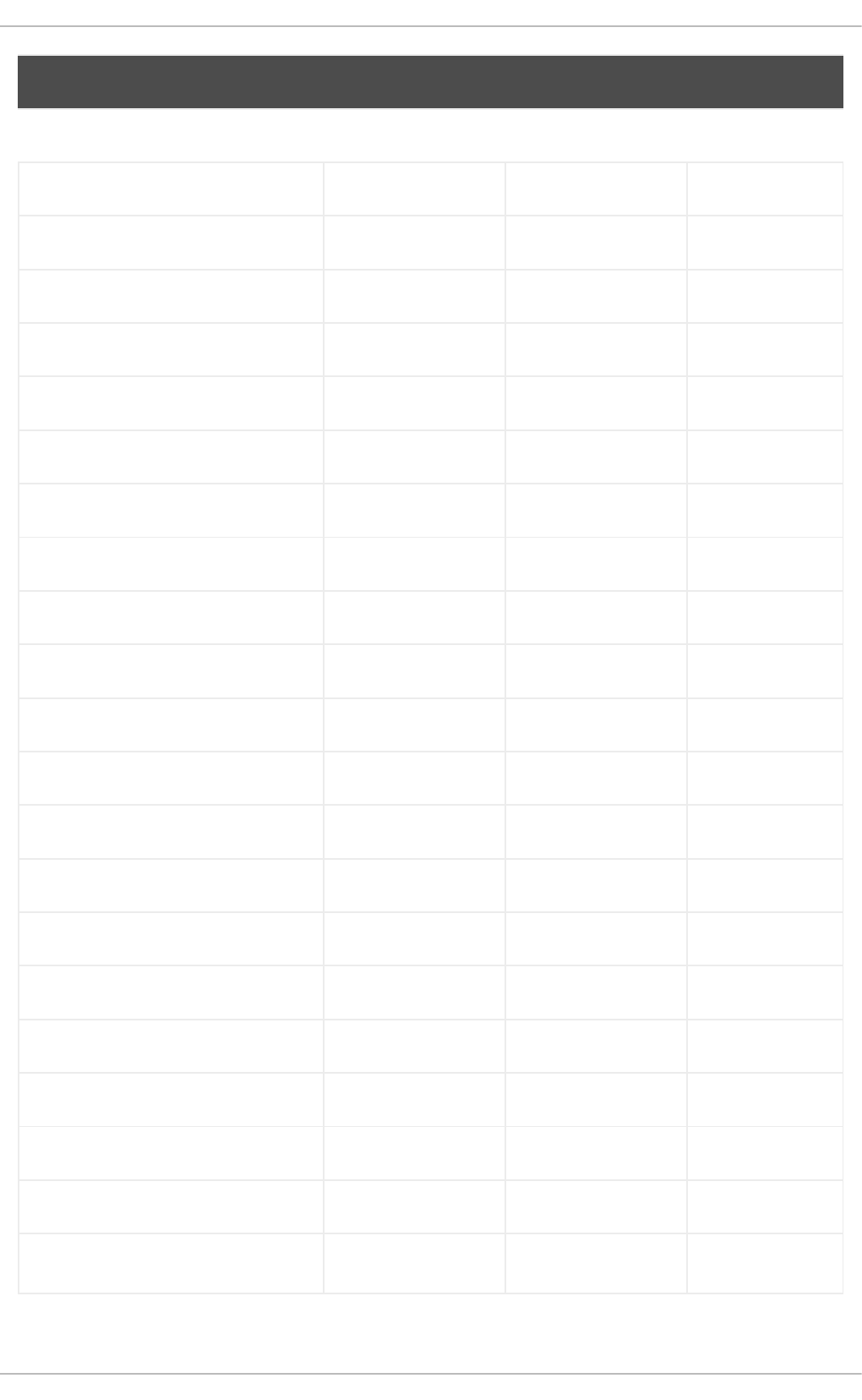
perl-Pod-Parser rhel8-AppStream rhel9-CRB RHEL 9.0
perl-Pod-Parser rhel8-AppStream rhel9-CRB RHEL 9.0
perl-Pod-Perldoc rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Pod-Simple rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Pod-Usage rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-podlators rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Scalar-List-Utils rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Socket rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Storable rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Sys-CPU rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Sys-MemInfo rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Term-ANSIColor rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Term-Cap rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Term-Size-Any rhel8-CRB rhel9-AppStream RHEL 9.0
perl-Term-Size-Perl rhel8-CRB rhel9-AppStream RHEL 9.0
perl-Term-Table rhel8-CRB rhel9-AppStream RHEL 9.0
perl-Text-Diff rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Text-ParseWords rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Text-Tabs+Wrap rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-threads rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-threads-shared rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
181

perl-Time-Local rhel8-BaseOS rhel9-AppStream RHEL 9.0
perl-Unicode-LineBreak rhel8-CRB rhel9-AppStream RHEL 9.0
perl-Unicode-Normalize rhel8-BaseOS rhel9-AppStream RHEL 9.0
plexus-cipher rhel8-CRB rhel9-AppStream RHEL 9.0
plexus-classworlds rhel8-CRB rhel9-AppStream RHEL 9.0
plexus-containers-component-
annotations
rhel8-CRB rhel9-AppStream RHEL 9.0
plexus-interpolation rhel8-CRB rhel9-AppStream RHEL 9.0
plexus-sec-dispatcher rhel8-CRB rhel9-AppStream RHEL 9.0
plexus-utils rhel8-CRB rhel9-AppStream RHEL 9.0
plotutils rhel8-CRB rhel9-AppStream RHEL 9.0
pmix-devel rhel8-CRB rhel9-AppStream RHEL 9.0
policycoreutils-dbus rhel8-BaseOS rhel9-AppStream RHEL 9.0
policycoreutils-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
policycoreutils-python-utils rhel8-BaseOS rhel9-AppStream RHEL 9.0
polkit-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
polkit-docs rhel8-BaseOS rhel9-AppStream RHEL 9.0
poppler-cpp rhel8-CRB rhel9-AppStream RHEL 9.0
poppler-qt5 rhel9-CRB rhel9-AppStream RHEL 9.1
popt-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
postfix rhel8-BaseOS rhel9-AppStream RHEL 9.0
postgresql-server-devel rhel8-AppStream rhel9-CRB RHEL 9.0
postgresql-server-devel rhel8-AppStream rhel9-CRB RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
182

postgresql-server-devel rhel8-AppStream rhel9-CRB RHEL 9.0
postgresql-server-devel rhel8-AppStream rhel9-CRB RHEL 9.0
postgresql-test rhel8-AppStream rhel9-CRB RHEL 9.0
postgresql-test rhel8-AppStream rhel9-CRB RHEL 9.0
postgresql-test rhel8-AppStream rhel9-CRB RHEL 9.0
postgresql-test rhel8-AppStream rhel9-CRB RHEL 9.0
powerpc-utils rhel8-BaseOS rhel9-AppStream RHEL 9.0
ppc64-diag rhel8-BaseOS rhel9-AppStream RHEL 9.0
protobuf-c rhel8-AppStream rhel9-BaseOS RHEL 9.0
protobuf-c-compiler rhel8-AppStream rhel9-CRB RHEL 9.0
protobuf-c-devel rhel8-AppStream rhel9-CRB RHEL 9.0
protobuf-compiler rhel8-AppStream rhel9-CRB RHEL 9.0
ps_mem rhel8-BaseOS rhel9-AppStream RHEL 9.0
publicsuffix-list rhel8-BaseOS rhel9-AppStream RHEL 9.0
python-cups-doc rhel8-CRB rhel9-AppStream RHEL 9.0
python3-audit rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-boom rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-cffi rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-cffi rhel9-AppStream rhel9-BaseOS RHEL 9.2
python3-configobj rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-cryptography rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-cryptography rhel9-AppStream rhel9-BaseOS RHEL 9.2
python3-docutils rhel8-AppStream rhel9-CRB RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
183

python3-gobject-base rhel8-AppStream rhel9-CRB RHEL 9.0
python3-hivex rhel8-AppStream rhel9-CRB RHEL 9.0
python3-idle rhel8-AppStream rhel9-CRB RHEL 9.0
python3-iniconfig rhel9-CRB rhel9-AppStream RHEL 9.2
python3-ipatests rhel8-AppStream rhel9-CRB RHEL 9.0
python3-iscsi-initiator-utils rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-libnbd rhel8-CRB rhel9-AppStream RHEL 9.0
python3-libproxy rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-libselinux rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-libsemanage rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-libstoragemgmt rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-libvirt rhel8-CRB rhel9-AppStream RHEL 9.0
python3-markdown rhel9-CRB rhel9-BaseOS RHEL 9.4
python3-oauthlib rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-packaging rhel8-CRB rhel9-AppStream RHEL 9.0
python3-pexpect rhel8-AppStream rhel9-BaseOS RHEL 9.0
python3-pluggy rhel8-AppStream rhel9-CRB RHEL 9.0
python3-pluggy rhel9-CRB rhel9-AppStream RHEL 9.2
python3-ply rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-ply rhel9-AppStream rhel9-BaseOS RHEL 9.2
python3-policycoreutils rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-ptyprocess rhel8-AppStream rhel9-BaseOS RHEL 9.0
python3-pwquality rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
184

python3-py rhel8-AppStream rhel9-CRB RHEL 9.0
python3-py rhel9-CRB rhel9-AppStream RHEL 9.2
python3-pycparser rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-pycparser rhel9-AppStream rhel9-BaseOS RHEL 9.2
python3-pygments rhel8-AppStream rhel9-CRB RHEL 9.0
python3-pytest rhel8-AppStream rhel9-CRB RHEL 9.0
python3-pytest rhel9-CRB rhel9-AppStream RHEL 9.2
python3-pyverbs rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-pywbem rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-requests-oauthlib rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-rtslib rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-ruamel-yaml rhel9-CRB rhel9-AppStream RHEL 9.4
python3-ruamel-yaml-clib rhel9-CRB rhel9-AppStream RHEL 9.4
python3-solv rhel8-BaseOS rhel9-AppStream RHEL 9.0
python3-test rhel8-BaseOS rhel9-CRB RHEL 9.0
python3-test rhel8-AppStream rhel9-CRB RHEL 9.0
python3-wcwidth rhel9-CRB rhel9-AppStream RHEL 9.1
python3-wheel rhel8-AppStream rhel9-CRB RHEL 9.0
python3-wheel-wheel rhel8-AppStream rhel9-CRB RHEL 9.0
qclib rhel8-BaseOS rhel9-AppStream RHEL 9.0
qclib-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
qgpgme rhel8-AppStream rhel9-CRB RHEL 9.0
qt5-qtquickcontrols2-devel rhel8-CRB rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
185

qt5-qtserialbus-devel rhel8-CRB rhel9-AppStream RHEL 9.0
qt5-qtwayland-devel rhel8-CRB rhel9-AppStream RHEL 9.0
quota-doc rhel8-BaseOS rhel9-AppStream RHEL 9.0
quota-nld rhel8-BaseOS rhel9-AppStream RHEL 9.0
quota-rpc rhel8-BaseOS rhel9-AppStream RHEL 9.0
quota-warnquota rhel8-BaseOS rhel9-AppStream RHEL 9.0
rasdaemon rhel8-BaseOS rhel9-AppStream RHEL 9.0
rdma-core-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
readline-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
redhat-indexhtml rhel8-BaseOS rhel9-AppStream RHEL 9.0
redhat-logos rhel8-BaseOS rhel9-AppStream RHEL 9.0
redhat-logos-httpd rhel8-BaseOS rhel9-AppStream RHEL 9.0
regexp rhel8-CRB rhel9-AppStream RHEL 9.0
rpcgen rhel8-CRB rhel9-AppStream RHEL 9.0
rpm-apidocs rhel8-BaseOS rhel9-AppStream RHEL 9.0
rpm-cron rhel8-BaseOS rhel9-AppStream RHEL 9.0
rpm-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
rpm-plugin-ima rhel8-BaseOS rhel9-AppStream RHEL 9.0
rpm-plugin-syslog rhel8-BaseOS rhel9-AppStream RHEL 9.0
rpm-plugin-systemd-inhibit rhel8-BaseOS rhel9-AppStream RHEL 9.0
rsync-daemon rhel8-BaseOS rhel9-AppStream RHEL 9.0
ruby-doc rhel8-AppStream rhel9-CRB RHEL 9.0
ruby-doc rhel8-AppStream rhel9-CRB RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
186

ruby-doc rhel8-AppStream rhel9-CRB RHEL 9.0
ruby-doc rhel8-AppStream rhel9-CRB RHEL 9.0
ruby-hivex rhel8-AppStream rhel9-CRB RHEL 9.0
ruby-libguestfs rhel8-AppStream rhel9-CRB RHEL 9.0
rubygem-mysql2-doc rhel8-AppStream rhel9-CRB RHEL 9.0
rubygem-mysql2-doc rhel8-AppStream rhel9-CRB RHEL 9.0
rubygem-mysql2-doc rhel8-AppStream rhel9-CRB RHEL 9.0
rubygem-mysql2-doc rhel8-AppStream rhel9-CRB RHEL 9.0
rubygem-pg-doc rhel8-AppStream rhel9-CRB RHEL 9.0
rubygem-pg-doc rhel8-AppStream rhel9-CRB RHEL 9.0
rubygem-pg-doc rhel8-AppStream rhel9-CRB RHEL 9.0
rubygem-pg-doc rhel8-AppStream rhel9-CRB RHEL 9.0
s390utils-base rhel8-BaseOS rhel9-AppStream RHEL 9.0
samba-client rhel8-BaseOS rhel9-AppStream RHEL 9.0
samba-krb5-printing rhel8-BaseOS rhel9-AppStream RHEL 9.0
samba-pidl rhel8-BaseOS rhel9-CRB RHEL 9.0
samba-test rhel8-BaseOS rhel9-CRB RHEL 9.0
samba-test-libs rhel8-BaseOS rhel9-CRB RHEL 9.0
samba-winbind-clients rhel8-BaseOS rhel9-AppStream RHEL 9.0
samba-winbind-krb5-locator rhel8-BaseOS rhel9-AppStream RHEL 9.0
samba-winexe rhel8-BaseOS rhel9-AppStream RHEL 9.0
sbd rhel8-AppStream rhel9-
ResilientStorage
RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
187

sbd rhel8-AppStream rhel9-
HighAvailability
RHEL 9.0
SDL2 rhel8-CRB rhel9-AppStream RHEL 9.0
SDL2-devel rhel8-CRB rhel9-AppStream RHEL 9.0
selinux-policy-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
sendmail-milter rhel8-AppStream rhel9-CRB RHEL 9.0
sgabios rhel8-CRB rhel9-AppStream RHEL 9.0
sgml-common rhel8-BaseOS rhel9-AppStream RHEL 9.0
sgpio rhel8-BaseOS rhel9-AppStream RHEL 9.0
shim-unsigned-aarch64 rhel8-CRB rhel9-AppStream RHEL 9.0
slf4j rhel8-CRB rhel9-AppStream RHEL 9.0
slf4j-jdk14 rhel8-CRB rhel9-AppStream RHEL 9.0
smc-tools rhel8-BaseOS rhel9-AppStream RHEL 9.0
sombok rhel8-CRB rhel9-AppStream RHEL 9.0
speech-dispatcher-doc rhel8-CRB rhel9-AppStream RHEL 9.0
spice-protocol rhel8-AppStream rhel9-CRB RHEL 9.0
sqlite rhel8-BaseOS rhel9-AppStream RHEL 9.0
sqlite-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
supermin-devel rhel8-AppStream rhel9-CRB RHEL 9.0
swig rhel8-AppStream rhel9-CRB RHEL 9.0
swig rhel8-AppStream rhel9-CRB RHEL 9.0
swig-doc rhel8-AppStream rhel9-CRB RHEL 9.0
swig-doc rhel8-AppStream rhel9-CRB RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
188

swig-gdb rhel8-AppStream rhel9-CRB RHEL 9.0
swig-gdb rhel8-AppStream rhel9-CRB RHEL 9.0
syslinux-tftpboot rhel8-BaseOS rhel9-AppStream RHEL 9.0
systemd-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
systemd-journal-remote rhel8-BaseOS rhel9-AppStream RHEL 9.0
target-restore rhel8-BaseOS rhel9-AppStream RHEL 9.0
tcl rhel8-AppStream rhel9-CRB RHEL 9.0
tcl-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
tcl-doc rhel8-BaseOS rhel9-AppStream RHEL 9.0
tix rhel8-AppStream rhel9-CRB RHEL 9.0
tmpwatch rhel8-BaseOS rhel9-AppStream RHEL 9.0
tpm2-abrmd rhel8-BaseOS rhel9-AppStream RHEL 9.0
tpm2-abrmd-selinux rhel8-BaseOS rhel9-AppStream RHEL 9.0
tpm2-tss-devel rhel8-BaseOS rhel9-CRB RHEL 9.0
tuned-profiles-atomic rhel8-BaseOS rhel9-AppStream RHEL 9.0
tuned-profiles-mssql rhel8-BaseOS rhel9-AppStream RHEL 9.0
tuned-profiles-oracle rhel8-BaseOS rhel9-AppStream RHEL 9.0
turbojpeg rhel8-AppStream rhel9-CRB RHEL 9.0
unixODBC-devel rhel8-AppStream rhel9-CRB RHEL 9.0
usbredir-devel rhel8-AppStream rhel9-CRB RHEL 9.0
uuidd rhel8-BaseOS rhel9-AppStream RHEL 9.0
varnish-devel rhel8-AppStream rhel9-CRB RHEL 9.0
Package Original repository* Current repository* Changed since
APPENDIX A. CHANGES TO PACKAGES
189

velocity rhel8-AppStream rhel9-CRB RHEL 9.0
vhostmd rhel8-AppStream rhel9-SAP-Solutions RHEL 9.0
vhostmd rhel8-AppStream rhel9-SAP-
NetWeaver
RHEL 9.0
vim-filesystem rhel8-AppStream rhel9-BaseOS RHEL 9.0
virt-v2v-man-pages-ja rhel8-AppStream rhel9-CRB RHEL 9.0
virt-v2v-man-pages-uk rhel8-AppStream rhel9-CRB RHEL 9.0
vm-dump-metrics rhel8-BaseOS rhel9-SAP-Solutions RHEL 9.0
vm-dump-metrics rhel8-BaseOS rhel9-SAP-
NetWeaver
RHEL 9.0
volume_key-devel rhel8-AppStream rhel9-CRB RHEL 9.0
watchdog rhel8-BaseOS rhel9-AppStream RHEL 9.0
web-assets-filesystem rhel8-CRB rhel9-AppStream RHEL 9.0
xalan-j2 rhel8-CRB rhel9-AppStream RHEL 9.0
xcb-util-image-devel rhel9-CRB rhel9-AppStream RHEL 9.4
xcb-util-renderutil-devel rhel9-CRB rhel9-AppStream RHEL 9.4
xerces-j2 rhel8-CRB rhel9-AppStream RHEL 9.0
xfsprogs-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
xhtml1-dtds rhel8-CRB rhel9-AppStream RHEL 9.0
xml-common rhel8-BaseOS rhel9-AppStream RHEL 9.0
xml-commons-apis rhel8-CRB rhel9-AppStream RHEL 9.0
xml-commons-resolver rhel8-CRB rhel9-AppStream RHEL 9.0
xmlrpc-c rhel8-BaseOS rhel9-AppStream RHEL 9.0
xmlrpc-c-client rhel8-BaseOS rhel9-AppStream RHEL 9.0
Package Original repository* Current repository* Changed since
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
190

xorg-x11-drv-evdev-devel rhel8-AppStream rhel9-CRB RHEL 9.0
xz-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
xz-java rhel8-CRB rhel9-AppStream RHEL 9.0
xz-lzma-compat rhel8-CRB rhel9-AppStream RHEL 9.0
zlib-devel rhel8-BaseOS rhel9-AppStream RHEL 9.0
zstd rhel8-AppStream rhel9-BaseOS RHEL 9.0
Package Original repository* Current repository* Changed since
*This table uses abbreviated names for the repository ID. Use the following examples to help identify
the full repository ID, where <arch> is the specific architecture:
rhel9-BaseOS: rhel-9-for-<arch>-baseos-rpms, rhel-9-for-<arch>-baseos-eus-rpms, rhel-9-
for-<arch>-baseos-e4s-rpms.
rhel9-AppStream: rhel-9-for-<arch>-appstream-rpms, rhel-9-for-<arch>-appstream-eus-
rpms, rhel-9-for-<arch>-appstream-e4s-rpms.
rhel9-CRB: codeready-builder-for-rhel-9-<arch>-rpms, codeready-builder-for-rhel-9-<arch>-
eus-rpms.
rhel9-SAP-Solutions: rhel-9-for-<arch>-sap-solutions-rpms, rhel-9-for-<arch>-sap-solutions-
eus-rpms, rhel-9-for-<arch>-sap-solutions-e4s-rpms.
rhel9-SAP-NetWeaver: rhel-9-for-<arch>-sap-netweaver-rpms, rhel-9-for-<arch>-sap-
netweaver-eus-rpms, rhel-9-for-<arch>-sap-netweaver-e4s-rpms.
A.4. REMOVED PACKAGES
The following packages are part of RHEL 8 but are not distributed with RHEL 9:
Package Note
abrt
abrt-addon-ccpp
abrt-addon-kerneloops
abrt-addon-pstoreoops
abrt-addon-vmcore
abrt-addon-xorg
APPENDIX A. CHANGES TO PACKAGES
191
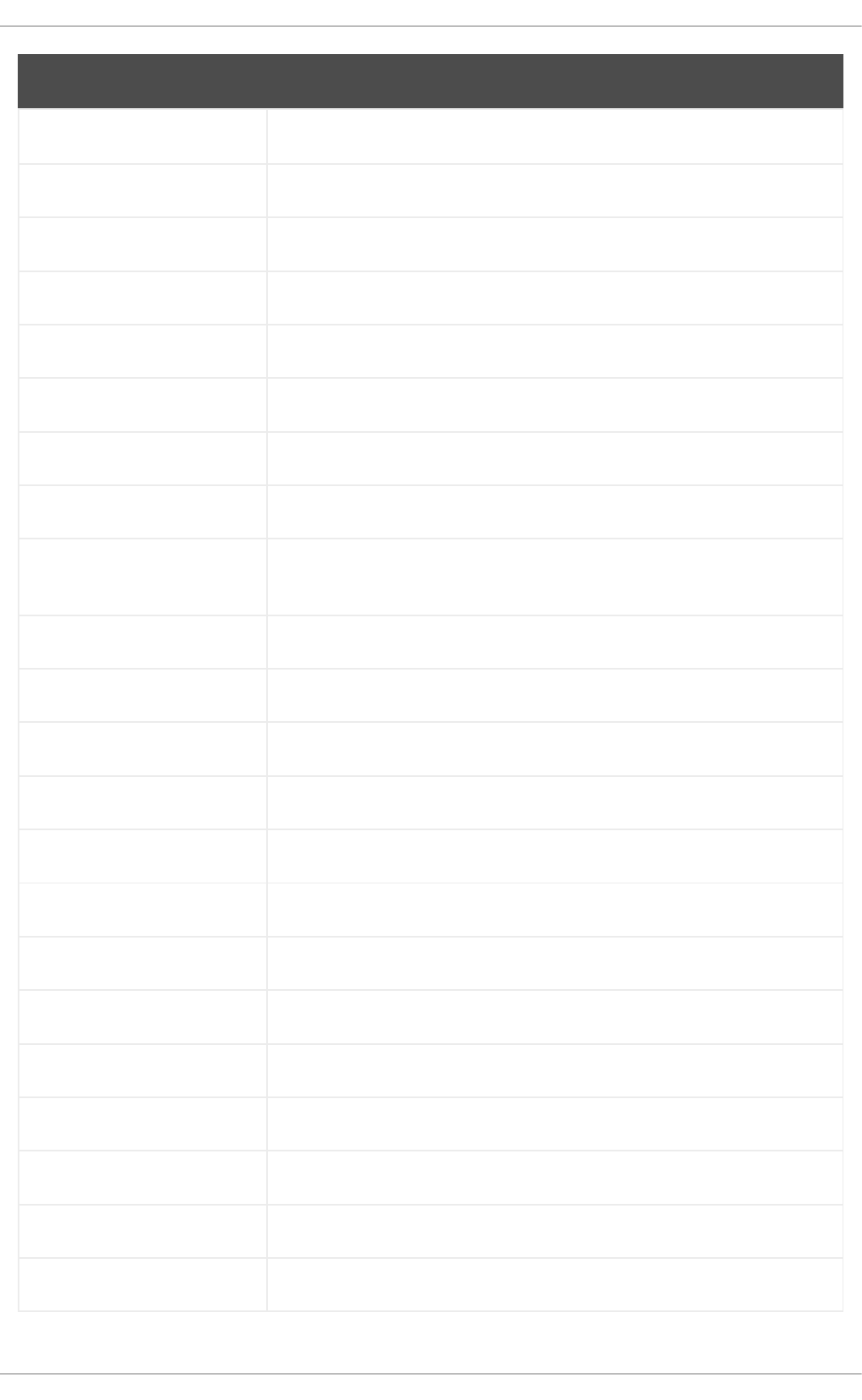
abrt-cli
abrt-console-notification
abrt-dbus
abrt-desktop
abrt-gui
abrt-gui-libs
abrt-libs
abrt-tui
adobe-source-sans-pro-
fonts-3.02803.el9.noarch.rpm
alsa-plugins-pulseaudio
alsa-sof-firmware-debug
amanda
amanda-client
amanda-libs
amanda-server
ant-apache-log4j
ant-contrib
ant-contrib-javadoc
ant-javadoc
ant-manual
antlr-C++
antlr-javadoc
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
192

antlr-manual
antlr3
antlr32
aopalliance
aopalliance
aopalliance-javadoc
apache-commons-beanutils-
javadoc
apache-commons-cli-javadoc
apache-commons-codec-
javadoc
apache-commons-
collections-javadoc
apache-commons-
collections-testframework
apache-commons-compress-
javadoc
apache-commons-exec
apache-commons-exec-
javadoc
apache-commons-io-javadoc
apache-commons-jxpath
apache-commons-jxpath
apache-commons-jxpath-
javadoc
apache-commons-lang-
javadoc
Package Note
APPENDIX A. CHANGES TO PACKAGES
193

apache-commons-lang3-
javadoc
apache-commons-logging-
javadoc
apache-commons-net-
javadoc
apache-commons-parent
apache-ivy
apache-ivy-javadoc
apache-parent
apache-resource-bundles
apache-sshd
apiguardian
aqute-bnd-javadoc
arpwatch
aspnetcore-runtime-3.0
aspnetcore-runtime-3.1
aspnetcore-runtime-5.0
aspnetcore-targeting-pack-
3.0
aspnetcore-targeting-pack-
3.1
aspnetcore-targeting-pack-
5.0
assertj-core-javadoc
atinject-javadoc
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
194

atinject-tck
authd
auto
autoconf213
autogen
autogen-libopts
autogen-libopts-devel
awscli
base64coder
bash-doc
batik
batik-css
batik-util
bcel-javadoc
bea-stax
bea-stax-api
beust-jcommander-javadoc
bind-export-devel
bind-export-libs
bind-pkcs11 Instead of the named-pkcs11 service, append -E pkcs11 to
named.service. Use pkcs11-tool from the opensc package to manage
pkcs11 tokens or stored keys.
bind-pkcs11-devel
bind-pkcs11-libs
Package Note
APPENDIX A. CHANGES TO PACKAGES
195

bind-pkcs11-utils
bind-sdb
bind-sdb-chroot
bitmap-console-fonts
bitmap-fixed-fonts
bitmap-fonts-compat
bitmap-lucida-typewriter-
fonts
bluez-hid2hci
bnd-maven-plugin
boost-jam
boost-signals
bouncycastle
bpg-algeti-fonts
bpg-chveulebrivi-fonts
bpg-classic-fonts
bpg-courier-fonts
bpg-courier-s-fonts
bpg-dedaena-block-fonts
bpg-dejavu-sans-fonts
bpg-elite-fonts
bpg-excelsior-caps-fonts
bpg-excelsior-condenced-
fonts
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
196

bpg-excelsior-fonts
bpg-fonts-common
bpg-glaho-fonts
bpg-gorda-fonts
bpg-ingiri-fonts
bpg-irubaqidze-fonts
bpg-mikhail-stephan-fonts
bpg-mrgvlovani-caps-fonts
bpg-mrgvlovani-fonts
bpg-nateli-caps-fonts
bpg-nateli-condenced-fonts
bpg-nateli-fonts
bpg-nino-medium-cond-
fonts
bpg-nino-medium-fonts
bpg-sans-fonts
bpg-sans-medium-fonts
bpg-sans-modern-fonts
bpg-sans-regular-fonts
bpg-serif-fonts
bpg-serif-modern-fonts
bpg-ucnobi-fonts
brlapi-java
Package Note
APPENDIX A. CHANGES TO PACKAGES
197

bsf-javadoc
bsh
bsh-javadoc
bsh-manual
buildnumber-maven-plugin
byaccj
byaccj-debuginfo
byaccj-debugsource
cal10n
cal10n-javadoc
cbi-plugins
cdi-api-javadoc
cdparanoia
cdparanoia-devel
cdparanoia-libs
cdrdao
celt051
celt051-devel
cgdcbxd
cglib-javadoc
clutter-devel
clutter-doc
clutter-gst3-devel
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
198

clutter-gtk-devel
cmirror
codehaus-parent
codemodel
cogl-devel
cogl-doc
compat-exiv2-026
compat-guile18
compat-guile18-devel
compat-hwloc1
compat-libpthread-nonshared
compat-libtiff3
compat-openssl10
compat-sap-c++-10
compat-sap-c++-11
compat-sap-c++-9
crash-ptdump-command
ctags
ctags-etags
culmus-keteryg-fonts
culmus-shofar-fonts
custodia
cyrus-imapd-vzic
Package Note
APPENDIX A. CHANGES TO PACKAGES
199

dbus-c++
dbus-c++-devel
dbus-c++-glib
dbxtool
dejavu-fonts-common
dhcp-libs
directory-maven-plugin
directory-maven-plugin-
javadoc
dirsplit
dleyna-connector-dbus
dleyna-core
dleyna-renderer
dleyna-server
dnf-plugin-spacewalk
dnssec-trigger
dnssec-trigger-panel
dotnet
dotnet-apphost-pack-3.0
dotnet-apphost-pack-3.1
dotnet-apphost-pack-5.0
dotnet-build-reference-
packages
dotnet-host-fxr-2.1
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
200

dotnet-hostfxr-3.0
dotnet-hostfxr-3.1
dotnet-hostfxr-5.0
dotnet-runtime-2.1
dotnet-runtime-3.0
dotnet-runtime-3.1
dotnet-runtime-5.0
dotnet-sdk-2.1
dotnet-sdk-2.1.5xx
dotnet-sdk-3.0
dotnet-sdk-3.1
dotnet-sdk-3.1-source-built-
artifacts
dotnet-sdk-5.0
dotnet-sdk-5.0-source-built-
artifacts
dotnet-targeting-pack-3.0
dotnet-targeting-pack-3.1
dotnet-targeting-pack-5.0
dotnet-templates-3.0
dotnet-templates-3.1
dotnet-templates-5.0
dotnet5.0-build-reference-
packages
Package Note
APPENDIX A. CHANGES TO PACKAGES
201

dptfxtract
drpm
drpm-devel
dump The dump package providing the dump utility has been removed. You can
use the tar, dd, or bacula backup utility instead.
dvd+rw-tools
dyninst-static
easymock-javadoc
eclipse-ecf
eclipse-ecf-core
eclipse-ecf-runtime
eclipse-emf
eclipse-emf-core
eclipse-emf-runtime
eclipse-emf-xsd
eclipse-equinox-osgi
eclipse-jdt
eclipse-license
eclipse-p2-discovery
eclipse-pde
eclipse-platform
eclipse-swt
ed25519-java
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
202

ee4j-parent
elfutils-devel-static
elfutils-libelf-devel-static
elinks
emacs-terminal
emoji-picker
enca
enca-devel
environment-modules-
compat
evemu
evemu-libs
evince-browser-plugin
exec-maven-plugin
exec-maven-plugin-javadoc
farstream02
felix-gogo-command
felix-gogo-runtime
felix-gogo-shell
felix-osgi-compendium
felix-osgi-compendium-
javadoc
felix-osgi-core
Package Note
APPENDIX A. CHANGES TO PACKAGES
203

felix-osgi-core-javadoc
felix-osgi-foundation
felix-osgi-foundation-javadoc
felix-parent
felix-scr
felix-utils-javadoc
file-roller
fipscheck
fipscheck-devel
fipscheck-lib
fonts-tweak-tool
forge-parent
freeradius-mysql
freeradius-perl
freeradius-postgresql
freeradius-sqlite
freeradius-unixODBC
frei0r-devel
frei0r-plugins
frei0r-plugins-opencv
fuse-sshfs
fusesource-pom
future
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
204

gamin
gamin-devel
gavl
gcc-toolset-10
gcc-toolset-10-annobin
gcc-toolset-10-binutils
gcc-toolset-10-binutils-devel
gcc-toolset-10-build
gcc-toolset-10-dwz
gcc-toolset-10-dyninst
gcc-toolset-10-dyninst-devel
gcc-toolset-10-elfutils
gcc-toolset-10-elfutils-
debuginfod-client
gcc-toolset-10-elfutils-
debuginfod-client-devel
gcc-toolset-10-elfutils-devel
gcc-toolset-10-elfutils-libelf
gcc-toolset-10-elfutils-libelf-
devel
gcc-toolset-10-elfutils-libs
gcc-toolset-10-gcc
gcc-toolset-10-gcc-c++
gcc-toolset-10-gcc-gdb-
plugin
Package Note
APPENDIX A. CHANGES TO PACKAGES
205

gcc-toolset-10-gcc-gfortran
gcc-toolset-10-gcc-plugin-
devel
gcc-toolset-10-gdb
gcc-toolset-10-gdb-doc
gcc-toolset-10-gdb-
gdbserver
gcc-toolset-10-libasan-devel
gcc-toolset-10-libatomic-
devel
gcc-toolset-10-libitm-devel
gcc-toolset-10-liblsan-devel
gcc-toolset-10-libquadmath-
devel
gcc-toolset-10-libstdc++-
devel
gcc-toolset-10-libstdc++-
docs
gcc-toolset-10-libtsan-devel
gcc-toolset-10-libubsan-devel
gcc-toolset-10-ltrace
gcc-toolset-10-make
gcc-toolset-10-make-devel
gcc-toolset-10-perftools
gcc-toolset-10-runtime
gcc-toolset-10-strace
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
206

gcc-toolset-10-systemtap
gcc-toolset-10-systemtap-
client
gcc-toolset-10-systemtap-
devel
gcc-toolset-10-systemtap-
initscript
gcc-toolset-10-systemtap-
runtime
gcc-toolset-10-systemtap-
sdt-devel
gcc-toolset-10-systemtap-
server
gcc-toolset-10-toolchain
gcc-toolset-10-valgrind
gcc-toolset-10-valgrind-devel
gcc-toolset-11
gcc-toolset-11-annobin-
annocheck
gcc-toolset-11-annobin-docs
gcc-toolset-11-annobin-
plugin-gcc
gcc-toolset-11-binutils
gcc-toolset-11-binutils-devel
gcc-toolset-11-build
gcc-toolset-11-dwz
gcc-toolset-11-dyninst
Package Note
APPENDIX A. CHANGES TO PACKAGES
207
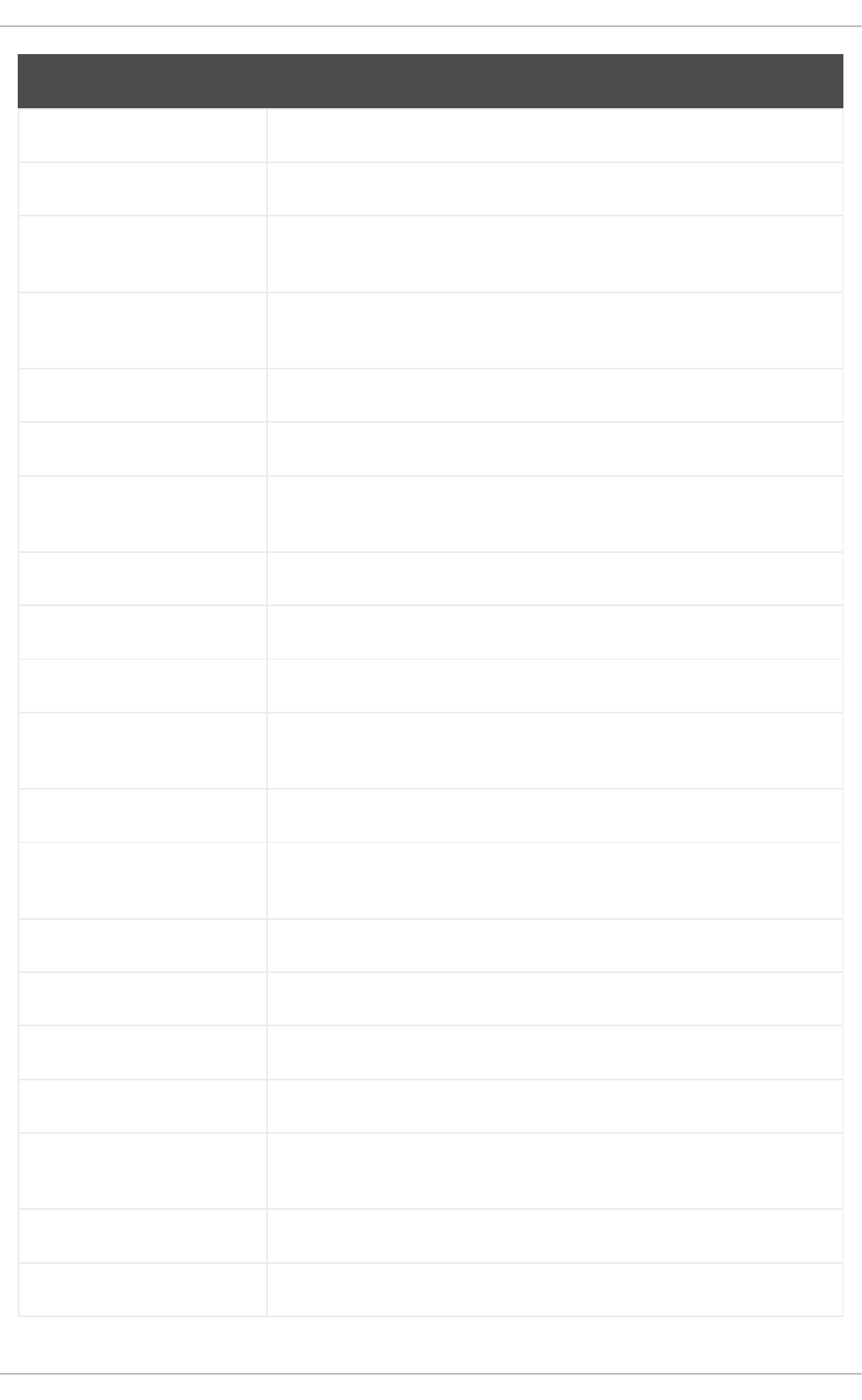
gcc-toolset-11-dyninst-devel
gcc-toolset-11-elfutils
gcc-toolset-11-elfutils-
debuginfod-client
gcc-toolset-11-elfutils-
debuginfod-client-devel
gcc-toolset-11-elfutils-devel
gcc-toolset-11-elfutils-libelf
gcc-toolset-11-elfutils-libelf-
devel
gcc-toolset-11-elfutils-libs
gcc-toolset-11-gcc
gcc-toolset-11-gcc-c++
gcc-toolset-11-gcc-gdb-
plugin
gcc-toolset-11-gcc-gfortran
gcc-toolset-11-gcc-plugin-
devel
gcc-toolset-11-gdb
gcc-toolset-11-gdb-doc
gcc-toolset-11-gdb-gdbserver
gcc-toolset-11-libasan-devel
gcc-toolset-11-libatomic-
devel
gcc-toolset-11-libgccjit
gcc-toolset-11-libgccjit-devel
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
208

gcc-toolset-11-libgccjit-docs
gcc-toolset-11-libitm-devel
gcc-toolset-11-liblsan-devel
gcc-toolset-11-libquadmath-
devel
gcc-toolset-11-libstdc++-
devel
gcc-toolset-11-libstdc++-docs
gcc-toolset-11-libtsan-devel
gcc-toolset-11-libubsan-devel
gcc-toolset-11-ltrace
gcc-toolset-11-make
gcc-toolset-11-make-devel
gcc-toolset-11-perftools
gcc-toolset-11-runtime
gcc-toolset-11-strace
gcc-toolset-11-systemtap
gcc-toolset-11-systemtap-
client
gcc-toolset-11-systemtap-
devel
gcc-toolset-11-systemtap-
initscript
gcc-toolset-11-systemtap-
runtime
gcc-toolset-11-systemtap-
sdt-devel
Package Note
APPENDIX A. CHANGES TO PACKAGES
209

gcc-toolset-11-systemtap-
server
gcc-toolset-11-toolchain
gcc-toolset-11-valgrind
gcc-toolset-11-valgrind-devel
gcc-toolset-12-annobin-
annocheck
gcc-toolset-12-annobin-docs
gcc-toolset-12-annobin-
plugin-gcc
gcc-toolset-12-binutils-devel
gcc-toolset-12-binutils-gold
gcc-toolset-9
gcc-toolset-9-annobin
gcc-toolset-9-binutils
gcc-toolset-9-binutils-devel
gcc-toolset-9-build
gcc-toolset-9-dwz
gcc-toolset-9-dyninst
gcc-toolset-9-dyninst-devel
gcc-toolset-9-dyninst-doc
gcc-toolset-9-dyninst-static
gcc-toolset-9-dyninst-
testsuite
gcc-toolset-9-elfutils
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
210

gcc-toolset-9-elfutils-devel
gcc-toolset-9-elfutils-libelf
gcc-toolset-9-elfutils-libelf-
devel
gcc-toolset-9-elfutils-libs
gcc-toolset-9-gcc
gcc-toolset-9-gcc-c++
gcc-toolset-9-gcc-gdb-
plugin
gcc-toolset-9-gcc-gfortran
gcc-toolset-9-gcc-plugin-
devel
gcc-toolset-9-gdb
gcc-toolset-9-gdb-doc
gcc-toolset-9-gdb-gdbserver
gcc-toolset-9-libasan-devel
gcc-toolset-9-libatomic-
devel
gcc-toolset-9-libitm-devel
gcc-toolset-9-liblsan-devel
gcc-toolset-9-libquadmath-
devel
gcc-toolset-9-libstdc++-
devel
gcc-toolset-9-libstdc++-docs
gcc-toolset-9-libtsan-devel
Package Note
APPENDIX A. CHANGES TO PACKAGES
211

gcc-toolset-9-libubsan-devel
gcc-toolset-9-ltrace
gcc-toolset-9-make
gcc-toolset-9-make-devel
gcc-toolset-9-perftools
gcc-toolset-9-runtime
gcc-toolset-9-strace
gcc-toolset-9-systemtap
gcc-toolset-9-systemtap-
client
gcc-toolset-9-systemtap-
devel
gcc-toolset-9-systemtap-
initscript
gcc-toolset-9-systemtap-
runtime
gcc-toolset-9-systemtap-
sdt-devel
gcc-toolset-9-systemtap-
server
gcc-toolset-9-toolchain
gcc-toolset-9-valgrind
gcc-toolset-9-valgrind-devel
GConf2
GConf2-devel
gegl
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
212

genwqe-tools
genwqe-vpd
genwqe-zlib
genwqe-zlib-devel
geoipupdate
geronimo-annotation
geronimo-annotation
geronimo-annotation-javadoc
geronimo-jms
geronimo-jms-javadoc
geronimo-jpa
geronimo-jpa-javadoc
geronimo-parent-poms
gfbgraph
gflags
gflags-devel
glassfish-annotation-api
glassfish-annotation-api
glassfish-annotation-api-
javadoc
glassfish-el
glassfish-fastinfoset
glassfish-jaxb-core
Package Note
APPENDIX A. CHANGES TO PACKAGES
213
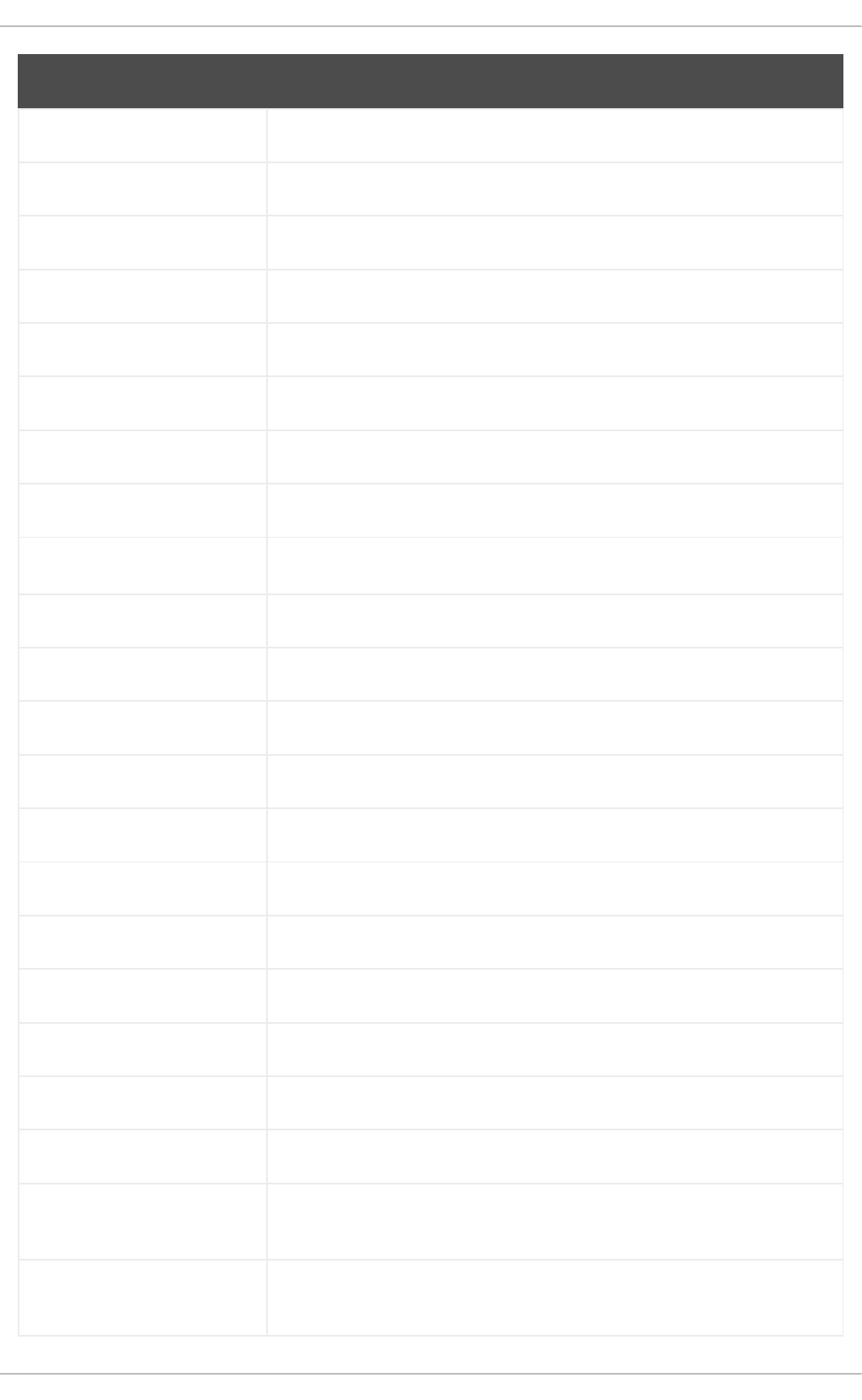
glassfish-jaxb-txw2
glassfish-jsp
glassfish-jsp-api
glassfish-jsp-api
glassfish-jsp-api-javadoc
glassfish-legal
glassfish-master-pom
glassfish-servlet-api
glassfish-servlet-api
glassfish-servlet-api-javadoc
glew-devel
glib2-fam
glog
glog-devel
gmock
gmock-devel
gnome-abrt
gnome-boxes
gnome-menus-devel
gnome-online-miners
gnome-shell-extension-dash-
to-panel
gnome-shell-extension-
disable-screenshield
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
214

gnome-shell-extension-
horizontal-workspaces
gnome-shell-extension-no-
hot-corner
gnome-shell-extension-
window-grouper
gnome-themes-standard
gnu-free-fonts-common
gnu-free-mono-fonts
gnu-free-sans-fonts
gnu-free-serif-fonts
gnuplot
gnuplot-common
gnuplot-doc
google-droid-kufi-fonts
google-gson
google-guice-javadoc
google-noto-kufi-arabic-
fonts
google-noto-naskh-arabic-
fonts
google-noto-naskh-arabic-ui-
fonts
google-noto-nastaliq-urdu-
fonts
google-noto-sans-balinese-
fonts
Package Note
APPENDIX A. CHANGES TO PACKAGES
215

google-noto-sans-bamum-
fonts
google-noto-sans-batak-
fonts
google-noto-sans-buginese-
fonts
google-noto-sans-buhid-
fonts
google-noto-sans-canadian-
aboriginal-fonts
google-noto-sans-cham-
fonts
google-noto-sans-cuneiform-
fonts
google-noto-sans-cypriot-
fonts
google-noto-sans-gothic-
fonts
google-noto-sans-gurmukhi-
ui-fonts
google-noto-sans-hanunoo-
fonts
google-noto-sans-
inscriptional-pahlavi-fonts
google-noto-sans-
inscriptional-parthian-fonts
google-noto-sans-javanese-
fonts
google-noto-sans-lepcha-
fonts
google-noto-sans-limbu-
fonts
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
216

google-noto-sans-linear-b-
fonts
google-noto-sans-lisu-fonts
google-noto-sans-mandaic-
fonts
google-noto-sans-meetei-
mayek-fonts
google-noto-sans-mongolian-
fonts
google-noto-sans-myanmar-
fonts
google-noto-sans-myanmar-
ui-fonts
google-noto-sans-new-tai-
lue-fonts
google-noto-sans-ogham-
fonts
google-noto-sans-ol-chiki-
fonts
google-noto-sans-old-italic-
fonts
google-noto-sans-old-
persian-fonts
google-noto-sans-oriya-fonts
google-noto-sans-oriya-ui-
fonts
google-noto-sans-phags-pa-
fonts
google-noto-sans-rejang-
fonts
google-noto-sans-runic-fonts
Package Note
APPENDIX A. CHANGES TO PACKAGES
217

google-noto-sans-samaritan-
fonts
google-noto-sans-saurashtra-
fonts
google-noto-sans-
sundanese-fonts
google-noto-sans-syloti-
nagri-fonts
google-noto-sans-syriac-
eastern-fonts
google-noto-sans-syriac-
estrangela-fonts
google-noto-sans-syriac-
western-fonts
google-noto-sans-tagalog-
fonts
google-noto-sans-tagbanwa-
fonts
google-noto-sans-tai-le-fonts
google-noto-sans-tai-tham-
fonts
google-noto-sans-tai-viet-
fonts
google-noto-sans-tibetan-
fonts
google-noto-sans-tifinagh-
fonts
google-noto-sans-ui-fonts
google-noto-sans-yi-fonts
google-noto-serif-bengali-
fonts
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
218

google-noto-serif-
devanagari-fonts
google-noto-serif-gujarati-
fonts
google-noto-serif-kannada-
fonts
google-noto-serif-
malayalam-fonts
google-noto-serif-tamil-fonts
google-noto-serif-telugu-
fonts
gphoto2
gsl-devel
gssntlmssp
gtest
gtest-devel
gtkmm24
gtkmm24-devel
gtkmm24-docs
gtksourceview3
gtksourceview3-devel
gtkspell
gtkspell-devel
guava20-javadoc
guava20-testlib
Package Note
APPENDIX A. CHANGES TO PACKAGES
219

guice-assistedinject
guice-bom
guice-extensions
guice-grapher
guice-jmx
guice-jndi
guice-multibindings
guice-parent
guice-servlet
guice-testlib
guice-throwingproviders
guile
guile-devel
gutenprint-libs-ui
gutenprint-plugin
gvfs-afc
gvfs-afp
gvfs-archive
hamcrest-core
hamcrest-core
hamcrest-demo
hamcrest-javadoc
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
220

hawtjni
hawtjni
hawtjni
hawtjni-javadoc
hawtjni-runtime
hawtjni-runtime
HdrHistogram
HdrHistogram-javadoc
highlight-gui
hplip-gui
hspell
httpcomponents-client-cache
httpcomponents-client-
javadoc
httpcomponents-core-
javadoc
httpcomponents-project
hwloc-plugins
hyphen-fo
hyphen-grc
hyphen-hsb
hyphen-ia
hyphen-is
hyphen-ku
Package Note
APPENDIX A. CHANGES TO PACKAGES
221

hyphen-mi
hyphen-mn
hyphen-sa
hyphen-tk
ibus-sayura
ibus-table-devel
ibus-table-tests
ibus-typing-booster-tests
icedax
icu4j
idm-console-framework
ilmbase-devel
ima-evm-utils0
imake
intel-gpu-tools
ipython
isl
isl-devel
isorelax
isorelax-javadoc
istack-commons-runtime
istack-commons-tools
ivy-local
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
222

iwl3945-firmware
iwl4965-firmware
iwl6000-firmware
jacoco
jaf
jaf-javadoc
jakarta-commons-httpclient-
demo
jakarta-commons-httpclient-
javadoc
jakarta-commons-httpclient-
manual
jakarta-oro-javadoc
janino
jansi-javadoc
jansi-native
jansi-native
jansi-native-javadoc
jarjar
java-1.8.0-ibm
java-1.8.0-ibm-demo
java-1.8.0-ibm-devel
java-1.8.0-ibm-headless
java-1.8.0-ibm-jdbc
Package Note
APPENDIX A. CHANGES TO PACKAGES
223

java-1.8.0-ibm-plugin
java-1.8.0-ibm-src
java-1.8.0-ibm-webstart
java-1.8.0-openjdk-
accessibility
java-1.8.0-openjdk-
accessibility-fastdebug
java-1.8.0-openjdk-
accessibility-slowdebug
java-atk-wrapper
java_cup
java_cup-javadoc
java_cup-manual
javacc
javacc-demo
javacc-javadoc
javacc-manual
javacc-maven-plugin
javacc-maven-plugin-javadoc
javaewah
javamail-javadoc
javapackages-local
javaparser
javapoet
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
224

javassist
javassist
javassist-javadoc
javassist-javadoc
jaxen
jaxen-demo
jaxen-javadoc
jboss-annotations-1.2-api
jboss-interceptors-1.2-api
jboss-interceptors-1.2-api
jboss-interceptors-1.2-api-
javadoc
jboss-logmanager
jboss-parent
jctools
jdepend-demo
jdepend-javadoc
jdependency
jdependency-javadoc
jdom
jdom-demo
jdom-javadoc
jdom2
Package Note
APPENDIX A. CHANGES TO PACKAGES
225

jdom2-javadoc
jetty
jetty-continuation
jetty-http
jetty-io
jetty-security
jetty-server
jetty-servlet
jetty-util
jffi
jflex
jflex-javadoc
jgit
jline
jline
jline-javadoc
jmc
jmc-core-javadoc
jnr-netdb
jolokia-jvm-agent
js-uglify
jsch-javadoc
json_simple
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
226

jsoup-javadoc
jsr-305-javadoc
jss-javadoc
jtidy
jul-to-slf4j
junit-javadoc
junit-manual
jvnet-parent
jzlib-demo
jzlib-javadoc
khmeros-fonts-common
kmod-redhat-oracleasm
kurdit-unikurd-web-fonts
kyotocabinet-libs
ldapjdk-javadoc
lensfun
lensfun-devel
lftp-scripts
libaec
libaec-devel
libappindicator-gtk3
libappindicator-gtk3-devel
libasan6
Package Note
APPENDIX A. CHANGES TO PACKAGES
227
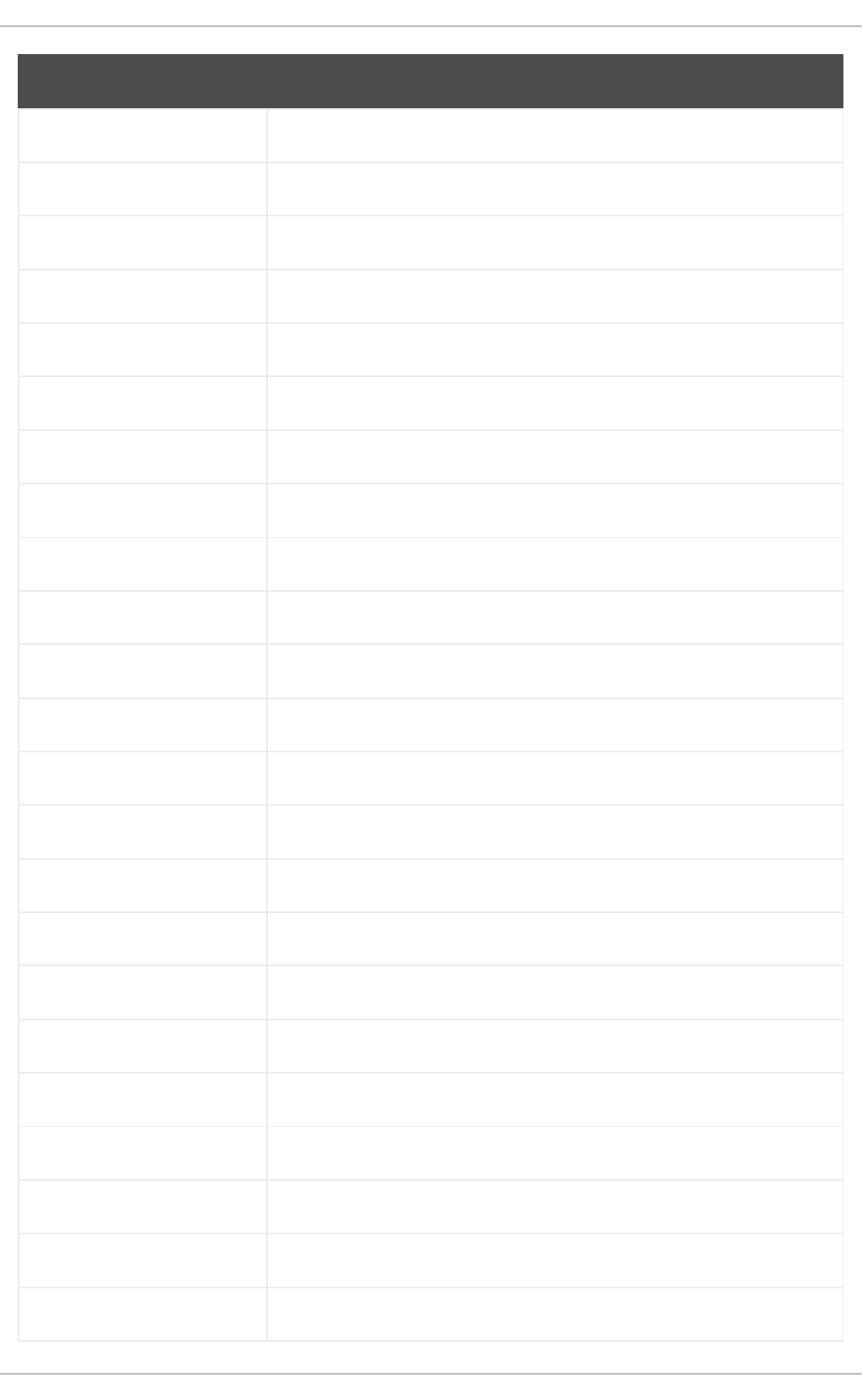
libatomic-static
libavc1394
libblocksruntime
libcacard
libcacard-devel
libcgroup
libcgroup-pam
libcgroup-tools
libchamplain
libchamplain-devel
libchamplain-gtk
libcroco
libcroco-devel
libcxl
libcxl-devel
libdap
libdap-devel
libdazzle-devel
libdbusmenu
libdbusmenu-devel
libdbusmenu-doc
libdbusmenu-gtk3
libdbusmenu-gtk3-devel
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
228

libdnet
libdnet-devel
libdv
libdv-devel
libdwarf The libdwarf package is not included in RHEL 9. The elfutils package
provides similar functionality.
libdwarf-devel
libdwarf-static
libdwarf-tools
libeasyfc
libeasyfc-gobject
libepubgen-devel
libertas-sd8686-firmware
libertas-usb8388-firmware
libertas-usb8388-olpc-
firmware
libgdither
libGLEW
libgovirt
libguestfs-benchmarking
libguestfs-gfs2
libguestfs-java
libguestfs-java-devel
libguestfs-javadoc
Package Note
APPENDIX A. CHANGES TO PACKAGES
229

libguestfs-tools
libguestfs-tools-c
libhugetlbfs
libhugetlbfs-devel
libhugetlbfs-utils
libicu-doc
libIDL
libIDL-devel
libidn The libidn package (which implements the IDNA 2003 standard) is not
included in RHEL 9. You can migrate applications to libidn2, which
implements the IDNA 2008 standard and has a different feature set to
libidn.
libidn-devel
libiec61883
libiec61883-devel
libindicator-gtk3
libindicator-gtk3-devel
libiscsi-devel
libkkc
libkkc-common
libkkc-data
liblogging
libmalaga
libmcpp
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
230

libmetalink
libmodulemd1 The libmodulemd1 package has been removed and is replaced by the
libmodulemd package.
libmongocrypt
libmpcdec
libmpcdec-devel
libmtp-devel
libmusicbrainz5
libmusicbrainz5-devel
libnice
libnice-devel
libnice-gstreamer1
liboauth
liboauth-devel
libocxl-docs
libpfm-static
libpng12
libpsm2-compat
libpurple
libpurple-devel
libraw1394
libraw1394-devel
libreport-plugin-mailx
Package Note
APPENDIX A. CHANGES TO PACKAGES
231

libreport-plugin-rhtsupport
libreport-plugin-ureport
libreport-rhel
libreport-rhel-bugzilla
librpmem The librpmem package has been removed. Use the librpma package
instead.
librpmem-debug
librpmem-devel
libsass
libsass-devel
libselinux-python
libslirp-devel
libsqlite3x
libssh2-docs
libtar
libtpms-devel
libunwind
libusal
libvarlink
libverto-libevent
libvirt-admin
libvirt-bash-completion
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
232

libvirt-daemon-driver-
storage-gluster
libvirt-daemon-driver-
storage-iscsi-direct
libvirt-gconfig
libvirt-gobject
libvirt-wireshark
libvmem
libvmem-debug
libvmem-devel
libvmmalloc
libvmmalloc-debug
libvmmalloc-devel
libvncserver
libwmf
libwmf-devel
libwmf-lite
libXNVCtrl
libXNVCtrl-devel
libXvMC
libXvMC-devel
libXxf86misc
libXxf86misc-devel
libyami
Package Note
APPENDIX A. CHANGES TO PACKAGES
233

log4j-over-slf4j
log4j12
log4j12
log4j12-javadoc
log4j12-javadoc
lohit-malayalam-fonts
lohit-nepali-fonts
lucene
lucene-analysis
lucene-analyzers-smartcn
lucene-queries
lucene-queryparser
lucene-sandbox
lz4-java
lz4-java-javadoc
mailman
make-devel
malaga
malaga-suomi-voikko
marisa
marisa-devel
maven-antrun-plugin
maven-antrun-plugin-javadoc
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
234

maven-archiver-javadoc
maven-artifact
maven-artifact-manager
maven-artifact-resolver-
javadoc
maven-artifact-transfer-
javadoc
maven-assembly-plugin
maven-assembly-plugin-
javadoc
maven-cal10n-plugin
maven-clean-plugin
maven-clean-plugin-javadoc
maven-common-artifact-
filters-javadoc
maven-compiler-plugin-
javadoc
maven-dependency-analyzer
maven-dependency-analyzer-
javadoc
maven-dependency-plugin
maven-dependency-plugin-
javadoc
maven-dependency-tree-
javadoc
maven-doxia
maven-doxia-core
Package Note
APPENDIX A. CHANGES TO PACKAGES
235

maven-doxia-javadoc
maven-doxia-logging-api
maven-doxia-module-apt
maven-doxia-module-
confluence
maven-doxia-module-
docbook-simple
maven-doxia-module-fml
maven-doxia-module-latex
maven-doxia-module-rtf
maven-doxia-module-twiki
maven-doxia-module-xdoc
maven-doxia-module-xhtml
maven-doxia-modules
maven-doxia-sink-api
maven-doxia-sitetools
maven-doxia-sitetools-
javadoc
maven-doxia-test-docs
maven-doxia-tests
maven-enforcer-javadoc
maven-failsafe-plugin
maven-file-management-
javadoc
maven-filtering-javadoc
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
236

maven-hawtjni-plugin
maven-install-plugin
maven-install-plugin-javadoc
maven-invoker
maven-invoker-javadoc
maven-invoker-plugin
maven-invoker-plugin-
javadoc
maven-jar-plugin-javadoc
maven-javadoc
maven-local
maven-model
maven-monitor
maven-parent
maven-plugin-build-helper-
javadoc
maven-plugin-bundle-javadoc
maven-plugin-descriptor
maven-plugin-registry
maven-plugin-testing-javadoc
maven-plugin-testing-tools
maven-plugin-tools-ant
maven-plugin-tools-beanshell
maven-plugin-tools-javadoc
Package Note
APPENDIX A. CHANGES TO PACKAGES
237
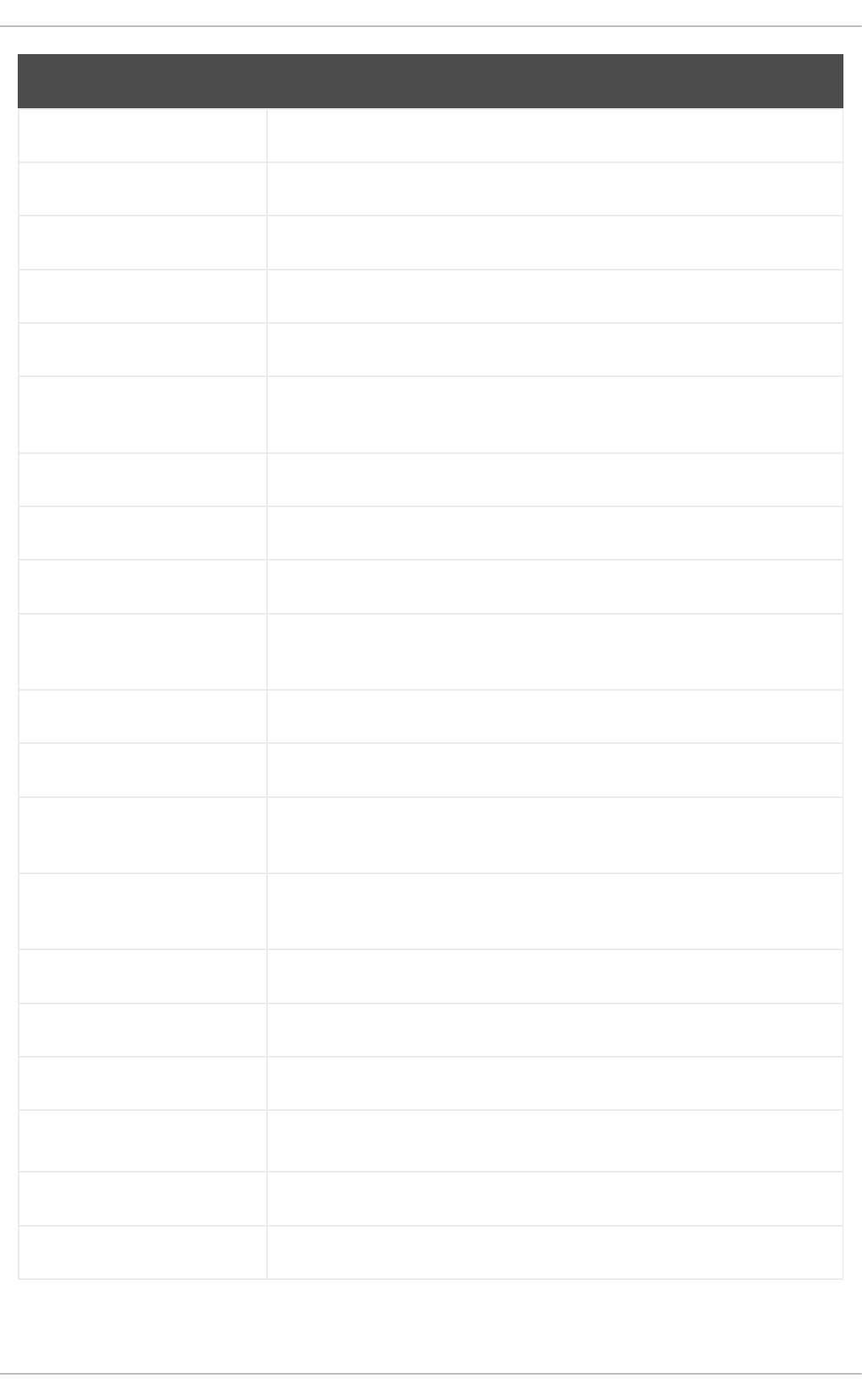
maven-plugin-tools-javadocs
maven-plugin-tools-model
maven-plugins-pom
maven-profile
maven-project
maven-remote-resources-
plugin-javadoc
maven-reporting-api
maven-reporting-api-javadoc
maven-reporting-impl
maven-reporting-impl-
javadoc
maven-resolver-api
maven-resolver-api
maven-resolver-connector-
basic
maven-resolver-connector-
basic
maven-resolver-impl
maven-resolver-impl
maven-resolver-javadoc
maven-resolver-spi
maven-resolver-spi
maven-resolver-test-util
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
238

maven-resolver-transport-
classpath
maven-resolver-transport-file
maven-resolver-transport-
http
maven-resolver-transport-
wagon
maven-resolver-transport-
wagon
maven-resolver-util
maven-resolver-util
maven-resources-plugin-
javadoc
maven-scm
maven-script
maven-script-ant
maven-script-beanshell
maven-script-interpreter
maven-script-interpreter-
javadoc
maven-settings
maven-shade-plugin
maven-shade-plugin-javadoc
maven-shared
maven-shared-incremental-
javadoc
Package Note
APPENDIX A. CHANGES TO PACKAGES
239

maven-shared-io-javadoc
maven-shared-utils-javadoc
maven-source-plugin-javadoc
maven-surefire-javadoc
maven-surefire-report-parser
maven-surefire-report-plugin
maven-test-tools
maven-toolchain
maven-verifier-javadoc
maven-wagon-file
maven-wagon-file
maven-wagon-ftp
maven-wagon-http
maven-wagon-http
maven-wagon-http-
lightweight
maven-wagon-http-shared
maven-wagon-http-shared
maven-wagon-javadoc
maven-wagon-provider-api
maven-wagon-provider-api
maven-wagon-providers
maven2
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
240

maven2
maven2-javadoc
meanwhile
mercurial
mercurial-hgk
mesa-libGLES-devel
mesa-vdpau-drivers
metis
metis-devel
mingw32-bzip2
mingw32-bzip2-static
mingw32-cairo
mingw32-expat
mingw32-fontconfig
mingw32-freetype
mingw32-freetype-static
mingw32-gstreamer1
mingw32-harfbuzz
mingw32-harfbuzz-static
mingw32-icu
mingw32-libjpeg-turbo
mingw32-libjpeg-turbo-static
mingw32-libpng
Package Note
APPENDIX A. CHANGES TO PACKAGES
241

mingw32-libpng-static
mingw32-libtiff
mingw32-libtiff-static
mingw32-openssl
mingw32-readline
mingw32-spice-vdagent
mingw32-sqlite
mingw32-sqlite-static
mingw64-adwaita-icon-
theme
mingw64-bzip2
mingw64-bzip2-static
mingw64-cairo
mingw64-expat
mingw64-fontconfig
mingw64-freetype
mingw64-freetype-static
mingw64-gstreamer1
mingw64-harfbuzz
mingw64-harfbuzz-static
mingw64-icu
mingw64-libjpeg-turbo
mingw64-libjpeg-turbo-static
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
242
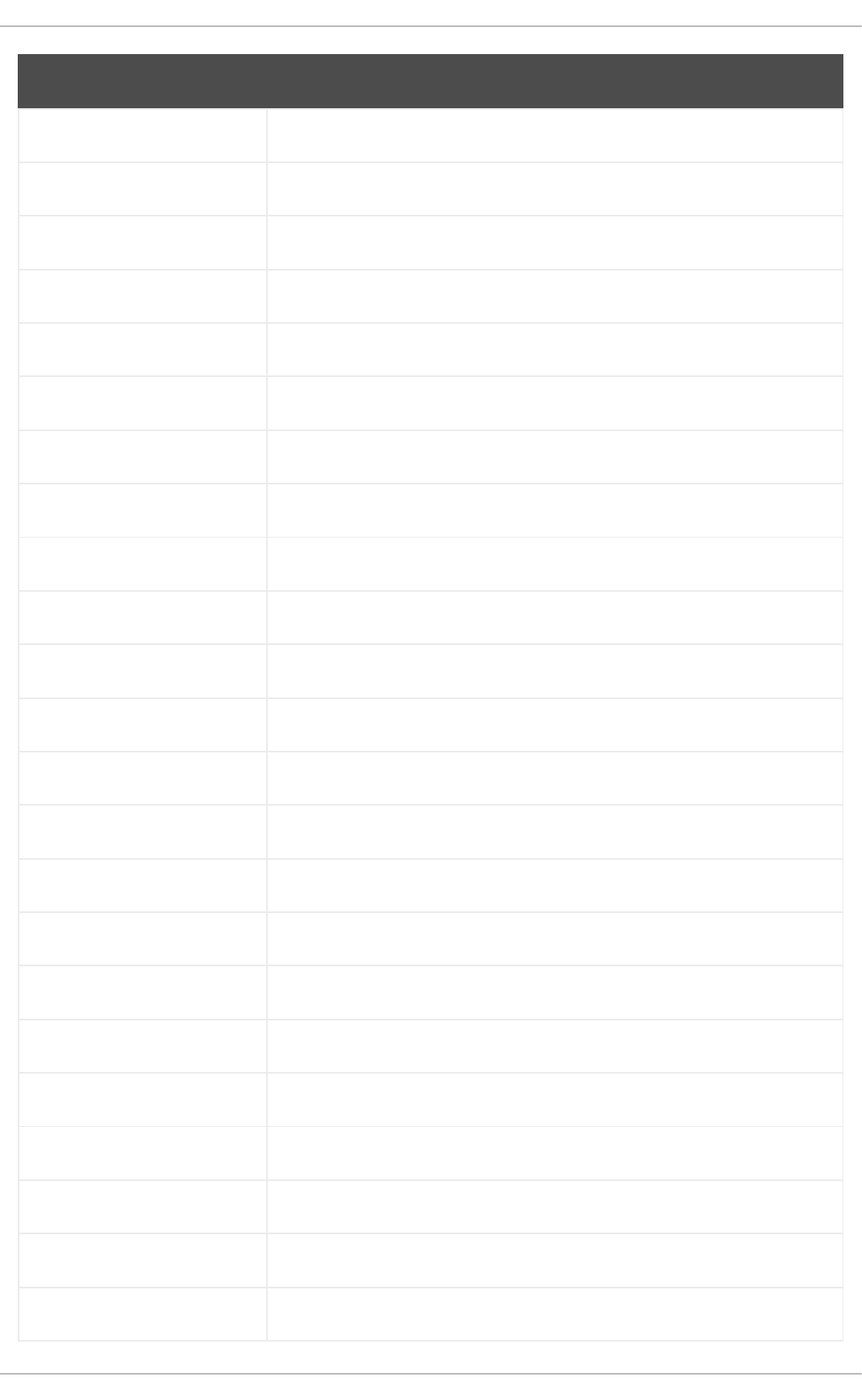
mingw64-libpng
mingw64-libpng-static
mingw64-libtiff
mingw64-libtiff-static
mingw64-nettle
mingw64-openssl
mingw64-readline
mingw64-spice-vdagent
mingw64-sqlite
mingw64-sqlite-static
mockito-javadoc
modello
modello-javadoc
mojo-parent
mongo-c-driver
motif-static
mousetweaks
mozjs52
mozjs52-devel
mozjs60
mozjs60-devel
mozvoikko
msv-javadoc
Package Note
APPENDIX A. CHANGES TO PACKAGES
243

msv-manual
munge-maven-plugin
munge-maven-plugin-javadoc
mythes-lb
mythes-mi
mythes-ne
nafees-web-naskh-fonts
nbd-3.21-2.el9
nbdkit-gzip-plugin
nbdkit-plugin-python-
common
nbdkit-plugin-vddk
nbdkit-tar-plugin
ncompress The ncompress package has been removed. You can use a different
compressing tool, such as gzip, zlib, or zstd.
ncurses-compat-libs
netcf
netcf-devel
netcf-libs
network-scripts
network-scripts-ppp
nkf
nodejs-devel
nodejs-packaging
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
244

nss-pam-ldapd The nss-pam-ldapd package has been removed. You can use SSSD
instead.
nss_nis
objectweb-asm-javadoc
objectweb-pom
objenesis-javadoc
ocaml-bisect-ppx
ocaml-camlp4
ocaml-camlp4-devel
ocaml-lwt-5.3.0-7.el9
ocaml-mmap-1.1.0-16.el9
ocaml-ocplib-endian-1.1-5.el9
ocaml-ounit-2.2.2-15.el9
ocaml-result-1.5-7.el9
ocaml-seq-0.2.2-4.el9
opencryptoki-tpmtok
opencv-contrib
opencv-core
opencv-devel
OpenEXR-devel
openhpi
openhpi-libs
OpenIPMI-perl
Package Note
APPENDIX A. CHANGES TO PACKAGES
245

openssh-cavs
openssh-ldap
openssl-ibmpkcs11
os-maven-plugin
os-maven-plugin-javadoc
osgi-annotation-javadoc
osgi-compendium-javadoc
osgi-core-javadoc
overpass-mono-fonts
owasp-java-encoder-javadoc
pakchois
pandoc
pandoc-common
paps-libs
paranamer
paratype-pt-sans-caption-
fonts
parfait
parfait-examples
parfait-javadoc
pcp-parfait-agent
pcsc-lite-doc
perl-B-Debug
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
246

perl-B-Lint
perl-Class-Factory-Util
perl-Class-ISA
perl-DateTime-Format-HTTP
perl-DateTime-Format-Mail
perl-File-CheckTree
perl-homedir
perl-libxml-perl
perl-Locale-Codes
perl-Mozilla-LDAP
perl-NKF
perl-Object-HashBase-tools
perl-Package-
DeprecationManager
perl-Pod-LaTeX
perl-Pod-Plainer
perl-prefork
perl-String-CRC32
perl-SUPER
perl-Sys-Virt
perl-tests
perl-YAML-Syck
phodav-2.5-4.el9
Package Note
APPENDIX A. CHANGES TO PACKAGES
247

php-recode
php-xmlrpc
pidgin
pidgin-devel
pidgin-sipe
pinentry-emacs
pinentry-gtk
pipewire0.2-devel
pipewire0.2-libs
platform-python-coverage
plexus-ant-factory
plexus-ant-factory-javadoc
plexus-archiver-javadoc
plexus-bsh-factory
plexus-bsh-factory-javadoc
plexus-build-api-javadoc
plexus-cipher-javadoc
plexus-classworlds-javadoc
plexus-cli
plexus-cli-javadoc
plexus-compiler-extras
plexus-compiler-javadoc
plexus-compiler-pom
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
248

plexus-component-api
plexus-component-api-
javadoc
plexus-component-factories-
pom
plexus-components-pom
plexus-containers-
component-javadoc
plexus-containers-
component-metadata
plexus-containers-container-
default
plexus-containers-javadoc
plexus-i18n
plexus-i18n-javadoc
plexus-interactivity
plexus-interactivity-api
plexus-interactivity-javadoc
plexus-interactivity-jline
plexus-interpolation-javadoc
plexus-io-javadoc
plexus-languages-javadoc
plexus-pom
plexus-resources-javadoc
plexus-sec-dispatcher-
javadoc
Package Note
APPENDIX A. CHANGES TO PACKAGES
249

plexus-utils-javadoc
plexus-velocity
plexus-velocity-javadoc
plymouth-plugin-throbgress
pmreorder
postgresql-test-rpm-macros
powermock
powermock-api-easymock
powermock-api-mockito
powermock-api-support
powermock-common
powermock-core
powermock-javadoc
powermock-junit4
powermock-reflect
powermock-testng
prometheus-jmx-exporter
prometheus-jmx-exporter-
openjdk11
ptscotch-mpich
ptscotch-mpich-devel
ptscotch-mpich-devel-
parmetis
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
250

ptscotch-openmpi
ptscotch-openmpi-devel
purple-sipe
pygobject2-doc
pygtk2
pygtk2-codegen
pygtk2-devel
pygtk2-doc
python-nose-docs
python-nss-doc
python-podman-api
python-psycopg2-doc
python-pymongo-doc
python-redis
python-schedutils
python-slip
python-sphinx-locale
python-sqlalchemy-doc
python-varlink
python-virtualenv-doc
python2-backports
python2-backports-
ssl_match_hostname
Package Note
APPENDIX A. CHANGES TO PACKAGES
251

python2-bson
python2-coverage
python2-docs
python2-docs-info
python2-funcsigs
python2-gluster
python2-ipaddress
python2-iso8601
python2-mock
python2-nose
python2-numpy-doc
python2-psycopg2-debug
python2-psycopg2-tests
python2-pymongo
python2-pymongo-gridfs
python2-pytest-mock
python2-sqlalchemy
python2-tools
python2-virtualenv
python3-bson
python3-click
python3-coverage
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
252

python3-cpio
python3-custodia
python3-docs
python3-evdev
python3-flask
python3-gevent
python3-html5lib
python3-hypothesis
python3-iso8601
python3-itsdangerous
python3-javapackages
python3-jwt
python3-mock
python3-networkx-core
python3-nose
python3-nss
python3-openipmi The python3-openipmi package is no longer provided. python3-
pyghmi has been introduced in order to provide a simpler Python API for
the IPMI protocol, but the API is not compatible with the one of python3-
openipmi.
python3-pexpect
python3-pillow
python3-pillow-devel
python3-pillow-doc
Package Note
APPENDIX A. CHANGES TO PACKAGES
253

python3-pillow-tk
python3-ptyprocess
python3-pydbus
python3-pymongo
python3-pymongo-gridfs
python3-pyOpenSSL
python3-reportlab
python3-schedutils
python3-scons
python3-semantic_version
python3-slip
python3-slip-dbus
python3-sqlalchemy The python3-sqlalchemy package has been removed. Customers must
use Python connectors for MySQL or PostgreSQL directly. Python 3
database connector for MySQL is available in the python3-PyMySQL
package. Python 3 database connector for PostgreSQL is available in the
python3-psycopg2 package.
python3-sure
python3-syspurpose
python3-unittest2
python3-virtualenv Use the venv module in Python 3 instead.
python3-webencodings
python3-werkzeug
python3-whoosh
python38-asn1crypto
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
254

python38-atomicwrites
python38-more-itertools
python38-numpy-doc
python38-psycopg2-doc
python38-psycopg2-tests
python39-more-itertools
python39-numpy-doc
python39-psycopg2-doc
python39-psycopg2-tests
python39-pybind11
python39-pybind11-devel
qdox-javadoc
qemu-kvm-block-gluster
qemu-kvm-block-iscsi
qemu-kvm-block-ssh
qemu-kvm-device-display-
virtio-gpu-gl
qemu-kvm-device-display-
virtio-gpu-pci-gl
qemu-kvm-device-display-
virtio-vga-gl
qemu-kvm-hw-usbredir
qemu-kvm-tests
qemu-kvm-ui-spice
Package Note
APPENDIX A. CHANGES TO PACKAGES
255

qpdf
qpdf-doc
qperf The qperf package has been removed. You can use the perftest or iperf3
package instead.
qpid-proton
qrencode
qrencode-devel
qrencode-libs
qt5-qtcanvas3d
qt5-qtcanvas3d-examples
rarian
rarian-compat
re2c
recode
redhat-lsb
redhat-lsb-core
redhat-lsb-cxx
redhat-lsb-desktop
redhat-lsb-languages
redhat-lsb-printing
redhat-lsb-submod-
multimedia
redhat-lsb-submod-security
redhat-menus
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
256

redhat-support-lib-python
redhat-support-tool
reflections
regexp-javadoc
relaxngDatatype
resteasy-javadoc
rhsm-gtk
rpm-plugin-prioreset
rpmemd
rubygem-abrt
rubygem-abrt-doc
rubygem-bson
rubygem-bson-doc
rubygem-bundler-doc
rubygem-mongo
rubygem-mongo-doc
rubygem-net-telnet
rubygem-xmlrpc
s390utils-cmsfs The s390utils-cmsfs package has been removed and is replaced by the
s390utils-cmsfs-fuse package.
samyak-devanagari-fonts
samyak-fonts-common
samyak-gujarati-fonts
Package Note
APPENDIX A. CHANGES TO PACKAGES
257

samyak-malayalam-fonts
samyak-odia-fonts
samyak-tamil-fonts
sane-frontends The sane-frontends package has been removed. Its functionality is
covered by the scanimage or xsane package.
sanlk-reset
sat4j
scala
scotch
scotch-devel
SDL_sound
selinux-policy-minimum
shim-ia32
shrinkwrap
sil-padauk-book-fonts
sisu-inject
sisu-inject
sisu-javadoc
sisu-mojos
sisu-mojos-javadoc
sisu-plexus
sisu-plexus
skkdic
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
258

slf4j-ext
slf4j-javadoc
slf4j-jcl
slf4j-log4j12
slf4j-manual
slf4j-sources
SLOF
smc-anjalioldlipi-fonts
smc-dyuthi-fonts
smc-fonts-common
smc-kalyani-fonts
smc-raghumalayalam-fonts
smc-suruma-fonts
softhsm-devel
sonatype-oss-parent
sonatype-plugins-parent
sos-collector
sparsehash-devel
spax The spax package has been removed. You can use the tar and cpio
commands instead.
spec-version-maven-plugin
spec-version-maven-plugin-
javadoc
spice-0.14.3-4.el9
Package Note
APPENDIX A. CHANGES TO PACKAGES
259

spice-client-win-x64
spice-client-win-x86
spice-glib
spice-glib-devel
spice-gtk
spice-gtk-tools
spice-gtk3
spice-gtk3-devel
spice-gtk3-vala
spice-parent
spice-qxl-wddm-dod
spice-qxl-xddm
spice-server
spice-server-devel
spice-streaming-agent
spice-vdagent-win-x64
spice-vdagent-win-x86
star
stax-ex
stax2-api
stringtemplate
stringtemplate4
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
260

subscription-manager-initial-
setup-addon
subscription-manager-
migration
subscription-manager-
migration-data
subversion-javahl
SuperLU
SuperLU-devel
swtpm-devel
swtpm-tools-pkcs11
system-storage-manager
systemd-tests
tcl-brlapi
testng
testng-javadoc
thai-scalable-laksaman-fonts
tibetan-machine-uni-fonts
timedatex The timedatex package has been removed. The systemd package
provides the systemd-timedated service, which replaces timedatex.
torque
torque-devel
torque-libs
tpm-quote-tools
tpm-tools
Package Note
APPENDIX A. CHANGES TO PACKAGES
261

tpm-tools-pkcs11
treelayout
trousers
trousers-devel
trousers-lib
tuned-profiles-compat
tuned-profiles-nfv-host-bin
tuned-utils-systemtap
tycho
uglify-js
unbound-devel
univocity-output-tester
usbguard-notifier
utf8cpp
uthash
uthash-devel
velocity-demo
velocity-javadoc
velocity-manual
vinagre
vino
virt-dib
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
262

virt-p2v-maker
vm-dump-metrics-devel
voikko-tools
vorbis-tools
weld-parent
woodstox-core
wqy-microhei-fonts
wqy-unibit-fonts
xalan-j2-demo
xalan-j2-javadoc
xalan-j2-manual
xalan-j2-xsltc
xbean-javadoc
xdelta
xerces-j2-demo
xerces-j2-javadoc
xinetd
xml-commons-apis-javadoc
xml-commons-apis-manual
xml-commons-resolver-
javadoc
xmlgraphics-commons
xmlstreambuffer
Package Note
APPENDIX A. CHANGES TO PACKAGES
263

xmlunit-javadoc
xmvn-api
xmvn-bisect
xmvn-connector-aether
xmvn-connector-ivy
xmvn-install
xmvn-javadoc
xmvn-parent-pom
xmvn-resolve
xmvn-subst
xmvn-tools-pom
xorg-sgml-doctools
xorg-x11-apps
xorg-x11-docs
xorg-x11-drv-ati
xorg-x11-drv-intel
xorg-x11-drv-nouveau
xorg-x11-drv-qxl
xorg-x11-drv-vesa
xorg-x11-server-Xspice
xorg-x11-xkb-utils-devel
xpp3
xsane-gimp
Package Note
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
264

xsom
xz-java-javadoc
yajl-devel
yp-tools
ypbind
ypserv
yum-rhn-plugin
zsh-html
Package Note
A.5. PACKAGES WITH REMOVED SUPPORT
Certain packages in RHEL 9 are distributed through the CodeReady Linux Builder repository, which
contains unsupported packages for use by developers.
The following packages are distributed in a supported repository in RHEL 8 and in the CodeReady Linux
Builder repository RHEL 9:
NOTE
This list covers only packages that are supported in RHEL 8 but not in RHEL 9.
Package RHEL 8 repository
apache-commons-collections rhel8-AppStream
apache-commons-compress rhel8-AppStream
aspell rhel8-AppStream
bind-devel rhel8-AppStream
createrepo_c-devel rhel8-AppStream
fstrm-devel rhel8-AppStream
gdbm rhel8-BaseOS
APPENDIX A. CHANGES TO PACKAGES
265

gdbm-devel rhel8-BaseOS
geoclue2-demos rhel8-AppStream
gobject-introspection-devel rhel8-AppStream
gtkspell3 rhel8-AppStream
hivex-devel rhel8-AppStream
kernel-cross-headers rhel8-BaseOS
ksc rhel8-BaseOS
libatomic_ops rhel8-AppStream
libestr-devel rhel8-AppStream
libfdisk-devel rhel8-BaseOS
libguestfs-devel rhel8-AppStream
libguestfs-gobject rhel8-AppStream
libguestfs-gobject-devel rhel8-AppStream
libguestfs-man-pages-ja rhel8-AppStream
libguestfs-man-pages-uk rhel8-AppStream
libica-devel rhel8-BaseOS
libiscsi-devel rhel8-AppStream
libjose-devel rhel8-AppStream
libldb-devel rhel8-BaseOS
libluksmeta-devel rhel8-AppStream
libnbd-devel rhel8-AppStream
libtalloc-devel rhel8-BaseOS
libtdb-devel rhel8-BaseOS
Package RHEL 8 repository
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
266

libtevent-devel rhel8-BaseOS
libvirt-devel rhel8-AppStream
libvirt-docs rhel8-AppStream
libvirt-lock-sanlock rhel8-AppStream
libwinpr-devel rhel8-AppStream
lua-guestfs rhel8-AppStream
mariadb-devel rhel8-AppStream
mariadb-embedded-devel rhel8-AppStream
mariadb-test rhel8-AppStream
multilib-rpm-config rhel8-AppStream
mysql-devel rhel8-AppStream
mysql-libs rhel8-AppStream
mysql-test rhel8-AppStream
nbdkit-devel rhel8-AppStream
nbdkit-example-plugins rhel8-AppStream
nginx-mod-devel rhel8-AppStream
nss_db rhel8-BaseOS
openblas-threads rhel8-AppStream
perl-IO-String rhel8-AppStream
perl-Module-Pluggable rhel8-AppStream
perl-Module-Runtime rhel8-AppStream
perl-Parse-Yapp rhel8-BaseOS
postgresql-server-devel rhel8-AppStream
Package RHEL 8 repository
APPENDIX A. CHANGES TO PACKAGES
267

postgresql-test rhel8-AppStream
postgresql-upgrade-devel rhel8-AppStream
protobuf-c-compiler rhel8-AppStream
protobuf-c-devel rhel8-AppStream
protobuf-compiler rhel8-AppStream
python3-gobject-base rhel8-AppStream
python3-hivex rhel8-AppStream
python3-ipatests rhel8-AppStream
python3-libguestfs rhel8-AppStream
qclib-devel rhel8-BaseOS
ruby-hivex rhel8-AppStream
ruby-libguestfs rhel8-AppStream
samba-pidl rhel8-BaseOS
samba-test rhel8-BaseOS
samba-test-libs rhel8-BaseOS
sendmail-milter rhel8-AppStream
spice-protocol rhel8-BaseOS
supermin-devel rhel8-AppStream
swig rhel8-AppStream
swig-doc rhel8-AppStream
swig-gdb rhel8-AppStream
turbojpeg rhel8-AppStream
unixODBC-devel rhel8-AppStream
Package RHEL 8 repository
Red Hat Enterprise Linux 9 Considerations in adopting RHEL 9
268

usbredir-devel rhel8-AppStream
velocity rhel8-AppStream
Package RHEL 8 repository
APPENDIX A. CHANGES TO PACKAGES
269
